DOGE as a National Cyberattack
Schneier on Security
FEBRUARY 13, 2025
There’s a reason why every modification—hardware or software—to these systems goes through a complex planning process and includes sophisticated access-control mechanisms.
This site uses cookies to improve your experience. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country, we will assume you are from the United States. Select your Cookie Settings or view our Privacy Policy and Terms of Use.
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.
Used for the proper function of the website
Used for monitoring website traffic and interactions
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.

Schneier on Security
FEBRUARY 13, 2025
There’s a reason why every modification—hardware or software—to these systems goes through a complex planning process and includes sophisticated access-control mechanisms.

Security Boulevard
OCTOBER 16, 2024
CA/B testing: Ludicrous proposal draws ire from “furious” systems administrators. The post Apple Enrages IT — 45-Day Cert Expiration Fury appeared first on Security Boulevard.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

SecureBlitz
FEBRUARY 28, 2022
IT risk management plans help administrators and workers identify possible risks that threaten the network and connecting systems. The administrators are responsible for managing the entire network and working with data systems administrators to protect customer and business data.
The Last Watchdog
AUGUST 2, 2024
1, 2024, CyberNewsWire — Security Risk Advisors (SRA) announces the launch of VECTR Enterprise Edition , a premium version of its widely-used VECTR platform for purple teams and adversary management program reporting and benchmarking. About VECTR : VECTR™ is developed and maintained by Security Risk Advisors.

Security Boulevard
MARCH 15, 2024
Implementing automated patching tools minimizes the risk of human errors and ensures patching consistency. LibCare offers automated security patching for the OpenSSL library without having to reboot systems. The post OpenSSL Patching: A Comprehensive Guide for System Administrators appeared first on Security Boulevard.

Centraleyes
DECEMBER 16, 2024
Tools like ChatGPT and Bard, powered by large language models, showcase how generative AI transforms business processesbut they also pose new risks. In a recent survey, 93% of respondents admitted to knowingly increasing their companys cybersecurity risks. The challenge? Securing these AI models and the data they generate.
Security Affairs
JULY 2, 2020
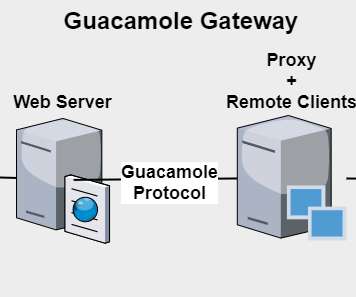
It supports standard protocols like VNC, RDP, and SSH and allows system administrators to remotely access and manage Windows and Linux machines. The post Critical Apache Guacamole flaws expose organizations at risk of hack appeared first on Security Affairs. ” Pierluigi Paganini.

Krebs on Security
MAY 29, 2020
The researchers concluded that for many people involved, cybercrime amounts to little more than a boring office job sustaining the infrastructure on which these global markets rely, work that is little different in character from the activity of legitimate system administrators.

Penetration Testing
JANUARY 2, 2024
PandoraFMS serves as a central hub for systems administrators to monitor and manage the... The post PandoraFMS Enterprise: Unveiling 18 High-Risk Network Vulnerabilities appeared first on Penetration Testing. NCC Group’s security researchers unearthed 18 vulnerabilities in PandoraFMS Enterprise v7.0NG.767,

eSecurity Planet
FEBRUARY 26, 2024
The fix: System administrators are encouraged to install the Exchange Server 2019 Cumulative Update 14 (CU14), which was issued in February 2024 and enabled NTLM credentials Relay Protection. Despite VMware’s three-year-old deprecation statement, unprotected systems remain at risk.

Krebs on Security
OCTOBER 8, 2024
“This creates a risk for employees using these older systems as part of their everyday work, especially if they are accessing sensitive data or performing financial transactions online,” he said. . “Since the discovery of CVE-2024-43572, Microsoft now prevents untrusted MSC files from being opened on a system.”

SecureList
DECEMBER 9, 2024
million systems worldwide. This incident serves as a stark reminder of the critical risks posed by global IT disruptions and supply chain weaknesses. This case underscores the serious risk that social engineering and supply chain attacks pose to open-source projects. Why does it matter? Pager attack in Middle East What happened?

Security Affairs
FEBRUARY 10, 2019
“They all come with a default username and “1234” as the default password, which is rarely changed by system administrators.” Imagine the damages that could be caused by activating the defrost function, especially when dealing with hospitals where refrigeration systems are used to store blood and drugs.

Security Affairs
DECEMBER 7, 2020
“This advisory emphasizes the importance for National Security System (NSS), Department of Defense (DoD), and Defense Industrial Base (DIB) system administrators to apply vendor-provided patches to affected VMware® identity management products and provides further details on how to detect and mitigate compromised networks.”

Heimadal Security
DECEMBER 19, 2024
The holiday season is a time of celebration, but its also a high-risk period for cyberattacks.Cybercriminals look to exploit reduced staffing, remote work, and the surge in online activity. As everyone scrambles for last-minute deals, these attackers find it easier than ever to slip through the cracks in your defenses.

Security Boulevard
JULY 26, 2023
Whether you are new to Linux or a seasoned Linux systems administrator, knowing the hardware and firmware on your systems is essential. Firmware that is out-of-date can pose security and operational risks.

The Last Watchdog
JANUARY 14, 2019
However, lacking robust protection, privileged accounts, which are intended to give administrators the access they need to manage critical systems, can instead be manipulated to enable attackers to move laterally across an organization’s network. LW: As the definition of privilege expands, what areas present the greatest risk? .

The Last Watchdog
AUGUST 12, 2024
When you add AI into the mix, it further intensifies the challenge of managing data sprawl and the associated risks.” I’m referring to the proliferation of fragmented, siloed security systems. For starters the ring is aimed at system administrators and senior executives, but could eventually go mainstream.

The Last Watchdog
MARCH 4, 2019
It was designed to make it convenient for system administrators to automate tasks and manage configurations across all Windows endpoints and servers in a company network. Critical application processes are at the greatest risk, including those that are running in air-gapped environments,” Gupta says.

Security Affairs
FEBRUARY 14, 2021
The FBI is warning companies about the use of out-of-date Windows 7 systems, desktop sharing software TeamViewer, and weak account passwords. The alert urges organizations to review internal networks and mitigate the risks posed by the above factors. ” reported the Reuters.
Security Affairs
AUGUST 4, 2021
US CISA and NSA released new guidance that provides recommendations on how to harden Kubernetes deployments and minimize the risk of hack. Kubernetes is an open-source container-orchestration system for automating computer application deployment, scaling, and management.

Security Affairs
FEBRUARY 20, 2020
One of the flaws patched the IT giant is a critical issue, tracked as CVE-2020-3158 , while six vulnerabilities are rated as high-risk severity. The CVE-2020-3158 flaw is related to the presence of a system account that has a default and static password in the Smart Software Manager tool. ” reads the advisory published by Cisco.
Security Affairs
JANUARY 21, 2020
Many system administrators and companies were rushing to update internet exposed machines, like web servers or gateways, worried about possible remote code execution, reviving the EternalBlue /WannaCry crisis in their mind. . What the NSA states is real: CVE-2020-0601 exposes companies to high risks.

The Security Ledger
MAY 16, 2024
In this Spotlight Podcast, host Paul Roberts talks with Chris Walcutt, the CSO of DirectDefense about the rising cyber threats facing operational technology (OT) and how organizations that manage OT - including critical infrastructure owners can best manage increased cyber risks to OT environments. Read the whole entry. »

eSecurity Planet
OCTOBER 18, 2024
Networking and system administration: Security professionals must instinctively understand network and system concepts. Network giant Cisco Systems Inc. reports that CISOs divide their work efforts among leadership roles (35% of the time), risk assessment management (44%), and data privacy and governance (33%).

Security Affairs
JUNE 2, 2020
Escalate privileges from “Organization Administrator” (normally a customer account) to “System Administrator” with access to all cloud accounts (organization) as an attacker can change the hash for this account. VMware has also released a workaround to mitigate the risk of exploitation for the flaw. and 10.0.0.2.
Duo's Security Blog
JUNE 8, 2023
During the workday, on the other hand, I spend a lot of time talking to systems administrators, security operations analysts, and IT professionals who do love MFA. They’ve seen it drive down incidents and help desk tickets, reduce their risks, and make compliance programs a lot easier.

BH Consulting
MARCH 12, 2025
Identifying unknown privacy risks The tool is free to download from the EU website and is available in five languages. The EDPB says it can help to identify potential unknown risks such as unintentionally set cookies; trust and transparency with website visitors; and improved website performance.

The Last Watchdog
JUNE 23, 2021
The challenge of embracing digital transformation while also quelling the accompanying cyber risks has never been greater for small- and mid-sized businesses. Somehow SMBs must keep pace competitively, while also tamping down the rising risk of suffering a catastrophic network breach. Remote desktop risks.

Security Affairs
OCTOBER 21, 2021
Skorodumov was one of the organization’s lead systems administrators, he configured and managed the clients’ domains and IP addresses, provided technical assistance to help clients optimize their malware and botnets. Follow me on Twitter: @securityaffairs and Facebook. Pierluigi Paganini. SecurityAffairs – hacking, cyber security).

The Last Watchdog
MARCH 29, 2022
These were all obscure open-source components that, over time, became deeply embedded in enterprise systems across the breadth of the Internet, only to have a gaping vulnerability discovered in them late in the game. Its rather mundane function is to record events in a log for a system administrator to review and act upon, later.

Malwarebytes
JULY 6, 2021
Early the next morning, Northshore systems administrator Ski Kacoroski arrived on scene. That was now at risk. As Kacoroski soon found out, he and his team were on a race against time—the ransomware actively spreading across servers holding data necessary for day-to-day operations.
Krebs on Security
SEPTEMBER 30, 2023
“The command requires Windows system administrators,” Truniger’s ads explained. A Semyon Sergeyvich Tretyakov is listed as the composer of a Russian-language rap song called “ Parallels ,” which seems to be about the pursuit of a high-risk lifestyle online. ” Mr.

Security Boulevard
JUNE 9, 2022
How to Overcome Common SSH Machine Identity Risks with Automation. Collecting Risk Intelligence. Prevent breaches by automating the collection of risk intelligence required to quickly identify and respond to SSH machine identity risks, weaknesses or security events. Higher levels of automation for system administrators.

CyberSecurity Insiders
JULY 2, 2021
Thus, in a joint statement released by Department of Defense, National Security Systems, Defense Industrial Base of United States, companies are urged to review their indicators of compromise respectively and take necessary measures to mitigate risks.

SecureList
MARCH 12, 2024
Distribution of Broken Access Control vulnerabilities by risk level, 2021–2023 ( download ) Almost half of the Broken Access Control vulnerabilities carried a medium risk level, and 37%, a high risk level. High-risk vulnerabilities can cause errors in applications and affect customers’ business.

eSecurity Planet
JUNE 21, 2022
It covers seven security domains: security operations and administration; access controls ; risk identification, monitoring and analysis; incident response and recovery; cryptography ; network and communications security; and systems and application security. An online review course and practice quiz are available.

Security Affairs
MAY 2, 2021
It’s also surprising that the malware author would risk criminal prosecution for what must surely be a small amount of profit, given the apparently small customer base. Organizations with effective spam filtering, proper system administration and up-to-date Windows hosts have a much lower risk of infection.”

CyberSecurity Insiders
JANUARY 5, 2022
Telehealth means patients don’t have to risk exposure to COVID-19 as often. Information systems are connecting patients and providers with data. For instance, AI has given surgeons robotic assistants like the Da Vinci Surgical System. By connecting people with care wherever they are, tech is contributing to a safer world.

Hot for Security
MAY 26, 2021
The bureau explains that such attacks are crippling to society, delaying access to real-time information, increasing safety risks to first responders and potentially endangering those who rely on calls for service. The attackers do so by employing throw-away VoIP numbers or via ProtonMail.
eSecurity Planet
FEBRUARY 21, 2023
Blue teams consist of security analysts, network engineers and system administrators. Learn more about Cybersecurity Risk Management Red Teams Red teams simulate the tactics, techniques, and procedures ( TTPs ) an adversary might use against the organization.

SC Magazine
JULY 7, 2021
Philips recently disclosed 15 critical vulnerabilities and provided patches or workarounds to remediate the risk. CISA reminds organizations to perform proper impact analysis and risk assessment prior to deploying defensive measures.”. A physician reviews medical images with the Philips Image Viewer for Vue PACS. Credit: Philips).

eSecurity Planet
SEPTEMBER 10, 2021
Public cloud infrastructure as a service (IaaS) may be less vulnerable than traditional data centers, but that doesn’t mean it’s without its own set of risks. Perhaps most importantly, cloud security training should help employees understand the inherent risk of shadow IT. What is cloud security? Enable security logs.

CyberSecurity Insiders
SEPTEMBER 24, 2021
That is why most companies hire professional information security services to mitigate the risks arising from data breaches. Ensure your employees understand the different external risks, how to identify and prevent the cyberattacks from happening. Your backed-up files might also be at risk of virus threats if not properly secured.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content