Solved: Subzero Spyware Secret — Austrian Firm Fingered
Security Boulevard
JULY 29, 2022
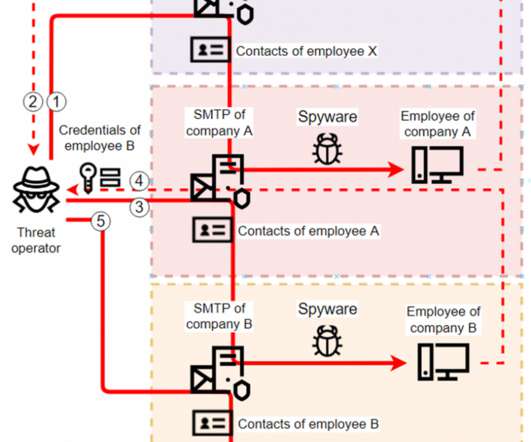
The post Solved: Subzero Spyware Secret — Austrian Firm Fingered appeared first on Security Boulevard. DSIRF GmbH codenamed ‘Knotweed’ by Microsoft and RiskIQ.
This site uses cookies to improve your experience. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country, we will assume you are from the United States. Select your Cookie Settings or view our Privacy Policy and Terms of Use.
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.
Used for the proper function of the website
Used for monitoring website traffic and interactions
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.

Security Boulevard
JULY 29, 2022
The post Solved: Subzero Spyware Secret — Austrian Firm Fingered appeared first on Security Boulevard. DSIRF GmbH codenamed ‘Knotweed’ by Microsoft and RiskIQ.

Security Boulevard
MAY 30, 2023
Intellexa mercenary spyware chains five unpatched bugs—plus ‘Alien’ technology The post ‘Predator’ — Nasty Android Spyware Revealed appeared first on Security Boulevard.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Boulevard
SEPTEMBER 25, 2023
The post More iOS Zero Days, More Mercenary Spyware — This Time: Cytrox Predator appeared first on Security Boulevard. Apple Scrambled to Fix 3 More CVEs: Egyptian opposition presidential candidate Ahmed Eltantawy targeted “by the government.

Security Boulevard
JUNE 28, 2023
The post Ironic: LetMeSpy Spyware Hackers Were Hacked (by Hackers) appeared first on Security Boulevard. Content warning: Abuse, stalking, controlling behavior, Schadenfreude, irony, doxxing.
Security Boulevard
MAY 3, 2022
The notorious spyware, sold by NSO Group “only to governments,” caused large amounts of data to be exfiltrated. Hacked by NSO Pegasus Spyware (or was it?) The prime minister and the defense minister of Spain were infected with Pegasus. The post Spanish Govt. appeared first on Security Boulevard.

SecureList
DECEMBER 9, 2024
This incident serves as a stark reminder of the critical risks posed by global IT disruptions and supply chain weaknesses. This case underscores the serious risk that social engineering and supply chain attacks pose to open-source projects. million systems worldwide. Why does it matter? Why does it matter?

Security Boulevard
AUGUST 22, 2022
NSO, notorious producer of the Pegasus nation-state spyware, is struggling. The post NSO Group Fires CEO — and 100 Staff — in Spyware ‘Streamlining’ appeared first on Security Boulevard. So it’s dumped its CEO, Shalev Hulio, and around 100 employees.
Security Boulevard
JULY 19, 2023
Adds ‘Mercenary Spyware’ Firms to Ban List appeared first on Security Boulevard. European cousins Intellexa and Cytrox essentially banned by Commerce Dept. Predator/ALIEN not welcome in U.S. The post Biden Admin.
Security Affairs
FEBRUARY 9, 2025
What are the risks?

Joseph Steinberg
JULY 13, 2022
Apple last week announced new security features specifically intended to offer “specialized additional protection to users who may be at risk of highly targeted cyberattacks from private companies developing state-sponsored mercenary spyware.”. Even in Lockdown mode, for example, people can easily install apps that spy on them.

Security Boulevard
JUNE 23, 2023
Vulns unpatched for FOUR years: ‘Triangulation’ spyware said to use backdoor Apple gave to NSA. The post Apple Fixes 0-Days — Russia Says US Used for Spying appeared first on Security Boulevard.

eSecurity Planet
FEBRUARY 22, 2022
There is no need for social engineering , as the program can implant backdoors directly without forced consent. NSO Group’s Pegasus software has been routinely in the headlines in recent years for using zero-click attacks to install its spyware. Spyware and Zero-Days: A Troubling Market.

Security Boulevard
JULY 20, 2021
Yet another zero-day bug in iOS has allowed notorious spyware vendor NSO Group to break into the iPhones of journalists and activists. The post Apple’s Insecure iPhone Lets NSO Hack Journalists (Again) appeared first on Security Boulevard.
CyberSecurity Insiders
MARCH 16, 2023
But after the spread of the Covid-19 pandemic, the focus of hackers has shifted more towards the smart phones with more phishing and social engineering attacks recorded in a 2nd quarter of 2022. Agility, awareness and alertness are the only mantra to mitigate risks.
Security Affairs
JUNE 4, 2023
Xplain hack impacted the Swiss cantonal police and Fedpol Zyxel published guidance for protecting devices from ongoing attacks Kimsuky APT poses as journalists and broadcast writers in its attacks New Linux Ransomware BlackSuit is similar to Royal ransomware CISA adds Progress MOVEit Transfer zero-day to its Known Exploited Vulnerabilities catalog (..)
Security Affairs
MARCH 8, 2020
FormBook data-stealing malware was used with cyber espionage purposes, like other spyware it is capable of extracting data from HTTP sessions, keystroke logging, stealing clipboard contents. See Using Caution with Email Attachments and Avoiding Social Engineering and Phishing Scams for more information.

Malwarebytes
JANUARY 25, 2024
Reconnaissance and social engineering are specific fields where AI can be deployed. Currently only state sponsored groups, professional spyware vendors, and the large criminal operations have access to, and know how to use advanced AI tools to increase the effectivity of their attacks.
Security Affairs
JUNE 11, 2023
Gox exchange and operating BTC-e Japanese Pharmaceutical giant Eisai hit by a ransomware attack Clop ransomware gang was testing MOVEit Transfer bug since 2021 Stealth Soldier backdoor used is targeted espionage attacks in Libya Researchers published PoC exploit code for actively exploited Windows elevation of privilege issue Experts detail a new Kimsuky (..)

Hot for Security
JUNE 15, 2021
Mobile security is often overlooked by many technology users, who dismiss the reality of security risks brought by careless interactions with the digital world. Smishing attacks rely on social engineering tactics to fool recipients into handing over personal information or downloading malicious software onto the device.

SecureList
JANUARY 18, 2023
The threat landscape is constantly updated through new malware and spyware, advanced phishing methods, and new social engineering techniques. More personal data leaks; corporate email at risk. In addition, the likelihood of the data being used for phishing and social engineering increases. .

Security Affairs
NOVEMBER 15, 2023
Source: Cybernews The fact that these indices were discovered suggests that the instance was not under regular monitoring, putting users at risk. Cybersecurity neglect endangers gamblers Failure to properly set authentication poses significant risks, as merely knowing the website’s domain is enough for an attacker to access user data.

Hacker's King
MAY 20, 2023
Service providers continually work to address such vulnerabilities, so it’s crucial to keep your software and applications up to date to minimize the risk. Social Engineering: Guarding Against Manipulation Social engineering remains a potent tool in hackers’ arsenal. You may also like: Is Every Hacker Is Same?

Identity IQ
MAY 7, 2021
With more than 15 billion login credentials available on the dark web because of data breaches, millions of online accounts remain at risk of unauthorized access. Social Engineering: Cybercriminals are increasingly using sophisticated social engineering tools to trick people into revealing their login credentials.
Identity IQ
FEBRUARY 18, 2021
The Risks to Digital Identities: Attack Vectors. However, while the benefits of the internet are never-ending, it’s also important to understand the risks involved so you can help avoid exposing your sensitive information to untrusted environments. The Risks to Digital Identities: Attack Vectors. A common example is phishing.
SecureList
MAY 27, 2022
The attackers study their victims carefully and use the information they find to frame social engineering attacks. One of the things you can do to protect yourself from advanced mobile spyware is to reboot your device on a daily basis. When opened, this document eventually downloads a backdoor. Other malware.

Security Boulevard
JANUARY 15, 2025
Dont Mess With Texas Privacy: We will hold all these companies accountable, rants state attorney general Ken Paxton (pictured). The post Allstate Violates Drivers Privacy, Texas AG Alleges appeared first on Security Boulevard.

SecureWorld News
JULY 27, 2023
Cybersecurity vendor experts provided their commentary on the findings: Zane Bond, Head of Product at Keeper Security, said: "The first phase of any breach begins with an external facing risk, such as a software vulnerability or employee who falls victim to phishing. Historically, user errors have been more of a risk than technical issues.

Malwarebytes
JUNE 7, 2021
Malicious hackers might use tools like computer viruses, spyware, ransomware, Trojan horses, and more to further their goals. While there may be financial incentives to hacking, the risks are high too: A malicious hacker can face a long time behind bars and massive fines for their illegal activity.

eSecurity Planet
JUNE 7, 2022
The Rapid7 Insight Platform gives you a broad spectrum of solutions for cloud security, vulnerability risk management, threat detection and response, and threat intelligence. It needs to be maintained for various types of cyber threats like Ransomware, Malware, Social Engineering, and Phishing. Learn more about CyberProof.

Google Security
MAY 15, 2024
Identifier Disclosure Transparency: We’ll help at risk-users like journalists or dissidents by alerting them if a potential false cellular base station or surveillance tool is recording their location using a device identifier. These features require device OEM integration and compatible hardware.

SecureWorld News
MARCH 29, 2024
This ends up executing sketchy code that installs viruses, ransomware, spyware, or adware behind the victim's back. Here's some evidence for those who consider the risk far-fetched. In addition to the risks outlined by CISA, these add-ons don't sift out dubious advertisements on search engines that are increasingly common.

Security Boulevard
AUGUST 6, 2024
Reduced Downtime : In the event of a takedown or disruption of a C2 server, dynamic DNS enables attackers to quickly re-establish communication with compromised systems by updating the DNS records, minimizing downtime and the risk of losing control over their botnet or malware network.
Security Affairs
MARCH 27, 2023
Such was related to a worldwide malware operation known as NullMixer, a controversial and widespread malware delivery maneuver based on SEO poisoning and social engineering technique to lure tech-savvy users, including IT personnel.

BH Consulting
NOVEMBER 15, 2022
He argued that security works when it costs €100,000 for spyware to hack into a politician’s iPhone. Éireann Leverett, CTO of Concinnity Risks, whose talk closed the conference, aimed to hit a similarly optimistic note. Sharon Conheady’s entertaining talk explored the ethical side of social engineering.
Hacker's King
OCTOBER 3, 2024
WhatsApp Pegasus Spyware Attack (2019) One of the most famous zero-day exploits happened on WhatsApp in 2019. Hackers discovered a vulnerability in WhatsApp’s call feature, allowing them to install spyware on phones without the user’s knowledge. Even if the user didn’t answer the call, spyware called Pegasus was installed.
Security Boulevard
MAY 8, 2024
PAFACA SueTok: U.S. Courts “likely” to rule whether new law is constitutional—or even practical. The post TikTok Ban — ByteDance Sues US to Kill Bill appeared first on Security Boulevard.

Security Boulevard
AUGUST 1, 2024
Cyber threats like viruses, spyware, and ransomware constantly evolve, posing significant risks to personal data, privacy, and device functionality. Many online services, including email providers, social media platforms, and financial institutions, offer 2FA options.

ForAllSecure
APRIL 26, 2023
Common Types of Cyber Attacks Common techniques that criminal hackers use to penetrate systems include social engineering, password attacks, malware, and exploitation of software vulnerabilities. It uses psychological manipulation to trick users into making security mistakes or giving away sensitive information.”
Security Boulevard
AUGUST 5, 2024
For You Plague: U.S. Justice Dept. and Federal Trade Commission file lawsuit, alleging TikTok broke the COPPA law, plus a previous injunction. The post TikTok Abuses Kids, say DoJ and FTC appeared first on Security Boulevard.

Thales Cloud Protection & Licensing
JULY 31, 2024
Cyber threats like viruses, spyware, and ransomware constantly evolve, posing significant risks to personal data, privacy, and device functionality. Many online services, including email providers, social media platforms, and financial institutions, offer 2FA options.
Security Boulevard
JUNE 2, 2023
Tit-For-Tat Triangulation Trojan Talk: Backdoor inserted at U.S. behest, alleges FSB. The post Russia Says NSA Hacked iOS With Apple’s Help — we Triangulate Kaspersky’s Research appeared first on Security Boulevard.
Security Boulevard
MAY 8, 2023
Clock Ticking for U.S. Ban: FT’s Cristina Criddle claims ByteDance spied on her—because she wrote damaging stories about TikTok. The post Knives Out for TikTok as Journo Reveals her Spy Story appeared first on Security Boulevard.
Security Boulevard
MARCH 8, 2024
Hilltop BillTok: ByteDance mobilizing addicted user base, as U.S. TikTok ban steamrolls through Capitol Hill after unanimous committee vote. The post TikTok Ban Incoming — but ByteDance Fights Back appeared first on Security Boulevard.

Security Boulevard
DECEMBER 1, 2023
For you plague, still: States can’t just ban apps, says federal judge. The post TikTok Ban Banned — Montana Loses in US Court appeared first on Security Boulevard.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content