How phishing attacks evade traditional security defenses
Tech Republic Security
MARCH 30, 2021
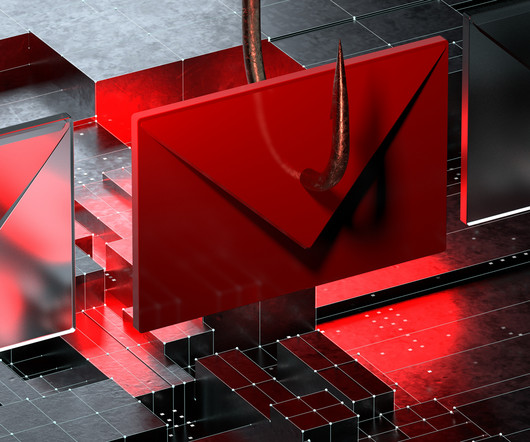
Two of three phishing pages analyzed by Armorblox were hosted on legitimate services to try to sneak past the usual security protection.
This site uses cookies to improve your experience. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country, we will assume you are from the United States. Select your Cookie Settings or view our Privacy Policy and Terms of Use.
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.
Used for the proper function of the website
Used for monitoring website traffic and interactions
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.

Tech Republic Security
MARCH 30, 2021
Two of three phishing pages analyzed by Armorblox were hosted on legitimate services to try to sneak past the usual security protection.

eSecurity Planet
FEBRUARY 26, 2025
Cybercriminals are shifting their focus from emails to text messages, using mishing a more deceptive form of phishing to target mobile users and infiltrate corporate networks, according to new security research by Zimperium. Vishing: Also known as voice phishing. What is mishing? and 9%in Brazil.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Digital Shadows
JANUARY 22, 2025
Phishing Remains Top Tactic, Fueled by Teams Abuse Figure 1: Top attack techniques in true-positive customer incidents for finance & insurance sector, H2 2024 vs H2 2023 Phishing dominated cyber attacks in H2 2024, accounting for over 90% of incidents across industries due to its simplicity and effectiveness.

Tech Republic Security
MARCH 11, 2020
A Trend Micro report finds that spammers are using public and hosted cloud infrastructure to slip malicious emails past security defenses.
Security Affairs
DECEMBER 1, 2024
From generating deepfakes to enhancing phishing campaigns, GAI is evolving into a tool for large-scale cyber offenses GAI has captured the attention of researchers and investors for its transformative potential across industries. GAI is also a boon for attackers seeking financial gain.

Security Affairs
APRIL 25, 2019
Experts at Proofpoint discovered that free code repositories on GitHub have been abused since at least 2017 to host phishing websites. Researchers at Proofpoint reported that crooks are abusing free code repositories on GitHub to host phishing websites and bypass security defenses. Pierluigi Paganini.
SC Magazine
MAY 11, 2021
Researchers last week spotted a phishing campaign that leveraged an online email authentication solution from Zix, in hopes that potential victims would be lulled into a false sense of security. The post Zix tricks: Phishing campaign creates false illusion that emails are safe appeared first on SC Media.

Security Boulevard
APRIL 24, 2025
Gone are the days of mass phishing campaigns. Evolving phishing trends to watch in 2025ThreatLabz uncovered many significant evolving trends in phishing attacks, with attackers adopting advanced tactics to bypass defenses and exploit human trust.

eSecurity Planet
AUGUST 23, 2023
Spear phishing is a more targeted and effective phishing technique that attempts to exploit specific individuals or groups within an organization. While phishing uses a broader range of tactics, such as mass emailing to random recipients, spear phishing is often well-researched and tailored to high-value targets.

Threatpost
FEBRUARY 4, 2021
A savvy phishing campaign manages to evade native Microsoft security defenses, looking to steal O365 credentials.

Threatpost
MARCH 11, 2020
Attackers are using YouTube redirect links, whitelisted by various security defense mechanisms, to evade detection.

Security Boulevard
FEBRUARY 10, 2025
As phishing attacks continue to evolve, so should our defenses. Phishing predictions for 2025In our ThreatLabz 2024 Phishing Report, we shared the following key predictions for the year to come: Prediction 1: AI vs. AI will be an enduring challengeEnhanced AI capabilities increase the speed, scale, and automation of cyberattacks.

Security Affairs
FEBRUARY 28, 2024
Emerging Threats and Trends The landscape of email threats continues to evolve, with VIPRE’s report shedding light on several alarming trends: Deepfake and AI Exploitation: Attackers increasingly leverage deepfake technology and AI to craft more convincing phishing emails, significantly raising the stakes for email security.
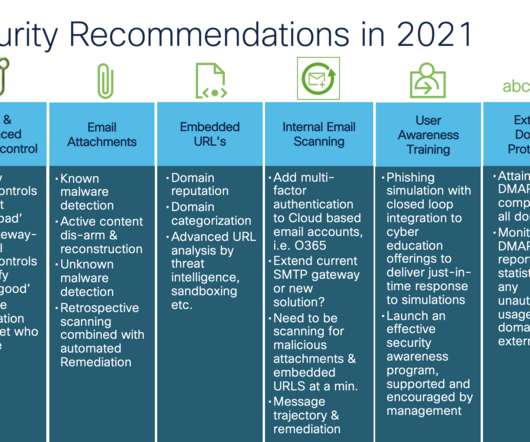
Cisco Security
AUGUST 17, 2021
Now mix in architectural changes that support cloud productivity suites like Microsoft 365 and Google’s G-Suite to accelerate your business to cloud-based email security services. When it comes to safeguarding email against today’s advanced threats like phishing and malware information is power.

Webroot
APRIL 4, 2022
High-risk URLs are phishing for your data in the most benign of locations. To make matters worse, almost 66% of them involved phishing. Our complete list of top brands that are most impersonated is available in the phishing section of our full report. Thwarting cyber threats through cyber resilience.

Security Affairs
MAY 21, 2020
The company is investigating the incident and announced that it is taking action to strengthen its security defenses and prevent similar incidents in the future. Home Chef users should remain vigilant against phishing attacks and suspicious activity in their accounts. Subscription”).

SC Magazine
JULY 6, 2021
Microsoft CEO Satya Nadella has been a strong proponent for average users facing phishing scams, especially during the COVID-19 pandemic. Today’s columnist, Tony Pepper of Egress, writes about how people have become the new perimeter and they must be properly trained to spot phishing attacks. They’re also not perfect.

eSecurity Planet
SEPTEMBER 16, 2024
AI-Powered Security Tools AI-powered security tools are revolutionizing how organizations approach cybersecurity. These tools use advanced algorithms to protect against various threats, from malware to phishing attacks. They offer real-time analysis and responses, making them a valuable asset in any security strategy.

SiteLock
AUGUST 27, 2021
Even a company with the most sophisticated cybersecurity tools and expert security teams can fall prey to cybercriminals if they overlook one area of vulnerability: their people. In fact, 97% of us can’t tell a phishing email from a legitimate one. Business Email Compromise (BEC) is similar to phishing. billion.

Hacker Combat
APRIL 6, 2022
The best ransomware protection combines solid, layered security defenses with data backups that an attacker can’t encrypt. Being Wary of Phishing Emails. Be on the lookout for phishing emails that appear to come from legitimate companies or individuals. Regular Software Updates.
eSecurity Planet
JULY 13, 2023
“WormGPT produced an email that was not only remarkably persuasive but also strategically cunning, showcasing its potential for sophisticated phishing and BEC attacks” (screenshot below). ” Just last week, Acronis reported that AI tools like ChatGPT have been behind a 464% increase in phishing attacks this year.

eSecurity Planet
JULY 10, 2024
In the wrong hands, it could be used for fraudulent purchases or earmarked phishing scams aimed at exploiting user trust. Also, phishing emails and messages often rely on a sense of familiarity to trick users into clicking malicious links or revealing personal information.

IT Security Guru
DECEMBER 15, 2022
By shifting security professionals’ mindset from a disparate, tool-based approach to a platform approach, businesses can improve their identity security defenses to protect against the modern threat landscape.” .

Malwarebytes
MARCH 5, 2021
Threat actors often vary their techniques to thwart security defenses and increase the efficiency of their attacks. Researchers found several actors that have exploited this conflict via phishing lures to drop AgentTesla and PoetRat. This blog post was authored by Hossein Jazi. C2: vnedoprym.kozow[.]com com 111.90.150[.]37.

eSecurity Planet
OCTOBER 6, 2023
Despite all the advances in cybersecurity, email remains the starting point for the vast majority of cyberattacks, as phishing, malware and social engineering remain effective attack techniques. That makes email security software a worthwhile investment for organizations of all sizes. The Complete Protect plan, which costs $6.00

eSecurity Planet
OCTOBER 8, 2024
Phishing: Among the possible methods used was phishing , where attackers deceive employees into revealing sensitive credentials, allowing them access to internal systems. Learn network security best practices to strengthen your security measures further and avoid such breaches. telecom networks.

SecureWorld News
NOVEMBER 8, 2023
Whether manifesting itself in a sophisticated phishing email or as a calculated series of conversations between employees and seemingly innocuous or "legitimate" parties with ulterior motives, a social engineering attack can have dire consequences. The average business faces more than 700 of these types of attacks every single year.

eSecurity Planet
AUGUST 30, 2023
A new Cloudflare phishing report notes that most of the 1 billion brand impersonation emails the company detected “passed” SPF, DKIM, and DMARC email authentication protocols. At the same time, an organization is also quite likely to fall for business email compromise and phishing attacks from their vendors.
eSecurity Planet
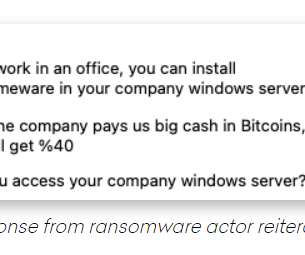
AUGUST 23, 2021
The bad actor told Hassold that he initially sent senior-level executives at the targeted companies phishing emails in hopes of compromising their accounts, but after that failed, he turned to trying to lure employees to unleash the ransomware themselves. Threat Traced to Nigeria. But this is just the start.”.

eSecurity Planet
AUGUST 20, 2024
Regularly check for updates to any software that doesn’t automatically update, including antivirus programs, firewalls, and other security tools. Be Wary of Phishing Scams Phishing attacks trick you into giving away personal information or installing malware by posing as legitimate contacts or companies.

eSecurity Planet
SEPTEMBER 5, 2024
The exposure of PII opens the door to targeted phishing campaigns , where attackers could pose as legitimate entities to extract further sensitive information. Urge users to change their passwords and be vigilant against phishing attempts, providing detailed guidance on recognizing and avoiding such attacks.

eSecurity Planet
OCTOBER 24, 2023
About 90% of cyber attacks begin with a phishing email, text or malicious link, so training users not to click on anything they’re not sure about could have the highest return on investment (ROI) of any prevention technique — if those training efforts are successful and reinforced. Don’t click on anything you’re unsure of.
eSecurity Planet
AUGUST 3, 2023
None of these security best practices are new, but increasingly sophisticated adversaries make it more important than ever to get them right. None of these security best practices are new, but increasingly sophisticated adversaries make it more important than ever to get them right.

Security Boulevard
APRIL 30, 2021
Almost every week we see new examples of highly sophisticated organizations and enterprises falling victim to another nation-state cyberattack or other security breach. Most security defenses focus on network protection and authorization, while memory-based attacks happen in the guts of applications.
Security Affairs
NOVEMBER 3, 2022
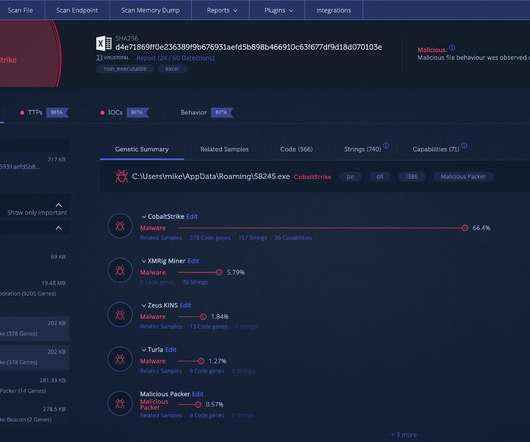
It focused on deploying POS malware and launching targeted spear-phishing attacks against organizations worldwide. In order to weaken the security defenses installed on the target machine, Black Basta targets installed security solutions with specific batch scripts downloaded into the Windows directory.

CyberSecurity Insiders
FEBRUARY 2, 2022
.–( BUSINESS WIRE )– Menlo Security , a leader in cloud security, today announced it has identified a surge in cyberthreats, termed Highly Evasive Adaptive Threats (HEAT), that bypass traditional security defenses. The top three brands impersonated in phishing attacks are Microsoft, PayPal, and Amazon.

eSecurity Planet
SEPTEMBER 13, 2024
Below, we explore the banking sector’s most common cyber security threats, highlighting real-world incidents and current trends. Phishing Attacks Phishing remains one of the most prevalent threats in the banking industry. AI is particularly effective at mitigating phishing and fraud attacks.

eSecurity Planet
DECEMBER 10, 2023
This can be done through a variety of attacks, such as spear phishing , and may require the attacker to steal multiple sets of credentials before they reach the information they need. Computer systems and networks that use default or factory credentials for servers and applications are more susceptible to this kind of attack.

eSecurity Planet
JANUARY 30, 2024
Breaches often stem from exploited vulnerabilities in cloud infrastructure or applications, with hackers using methods such as software vulnerabilities, phishing, or compromised credentials. Malicious insiders may also leverage successful phishing attempts or lax credential security, resulting in unauthorized access to cloud resources.

eSecurity Planet
OCTOBER 11, 2023
“This is typically achieved through social engineering attacks with spear phishing to gain initial access to a host before searching for other internal vulnerable targets. Just because your Exchange Server doesn’t have internet-facing authentication doesn’t mean it’s protected.”
eSecurity Planet
MARCH 14, 2022
Pentesting involves vulnerability exploitation and post-exploitation actions – the idea is to conduct a real attack, like cybercriminals would do, except with an explicit authorization from the company in order to identify weaknesses and improve security defenses.

eSecurity Planet
AUGUST 22, 2024
Attackers steal cookies through phishing, malware, and MITM attacks, resulting in data theft, financial loss, and identity theft. Long-term threats need a serious effort to secure stolen data and safeguard your privacy against further misuse. Phishing scams and rogue websites can spread cookie-stealing software.

Security Boulevard
SEPTEMBER 20, 2021
The dissemination phase consists of active processing and dissemination of the processed data for the purpose of communicating the actionable intelligence for the purpose of ensuring that an organizations defense is actively aware of the threats facing its infrastructure and security defense mechanisms.

Duo's Security Blog
JULY 27, 2023
" Organizations use this information to audit, assess, and implement security defense-in-depth strategies to mitigate cybersecurity attacks. MITRE ATT&CK is a "globally accessible knowledge base of adversary tactics and techniques based on real-world observations."
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content