What Is EDR in Cyber Security: Overview & Capabilities
eSecurity Planet
SEPTEMBER 24, 2024
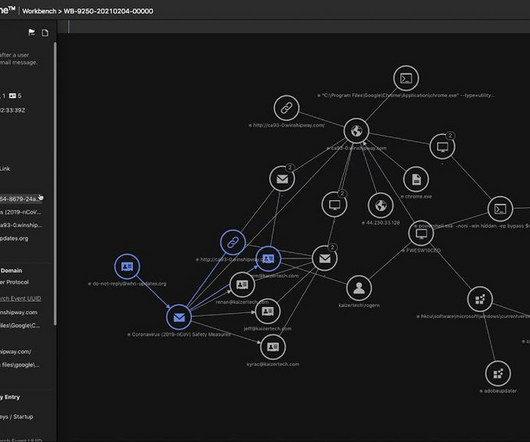
Configuring the EDR tool: Tailor the EDR policies according to your organization’s specific security requirements. This step provides configurable flexibility for best performance. It’s well-known for its high-security performance and usability, particularly in threat hunting and incident triage.











Let's personalize your content