TajMahal Spyware
Schneier on Security
APRIL 11, 2019
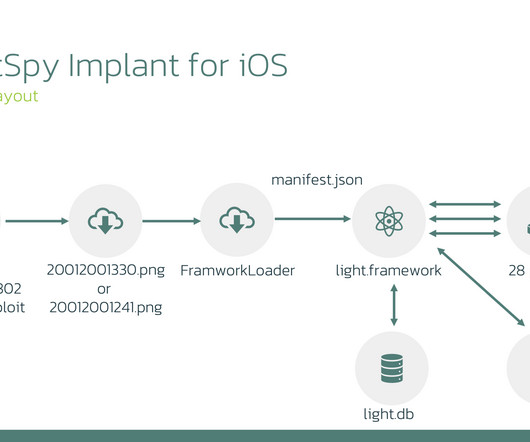
Kaspersky has released details about a sophisticated nation-state spyware it calls TajMahal: The TajMahal framework's 80 modules, Shulmin says, comprise not only the typical keylogging and screengrabbing features of spyware, but also never-before-seen and obscure tricks. No speculation on who wrote and controls it. More details.















Let's personalize your content