Solved: Subzero Spyware Secret — Austrian Firm Fingered
Security Boulevard
JULY 29, 2022
The post Solved: Subzero Spyware Secret — Austrian Firm Fingered appeared first on Security Boulevard. DSIRF GmbH codenamed ‘Knotweed’ by Microsoft and RiskIQ.
This site uses cookies to improve your experience. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country, we will assume you are from the United States. Select your Cookie Settings or view our Privacy Policy and Terms of Use.
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.
Used for the proper function of the website
Used for monitoring website traffic and interactions
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.

Security Boulevard
JULY 29, 2022
The post Solved: Subzero Spyware Secret — Austrian Firm Fingered appeared first on Security Boulevard. DSIRF GmbH codenamed ‘Knotweed’ by Microsoft and RiskIQ.

Security Boulevard
MAY 30, 2023
Intellexa mercenary spyware chains five unpatched bugs—plus ‘Alien’ technology The post ‘Predator’ — Nasty Android Spyware Revealed appeared first on Security Boulevard.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

SecureWorld News
OCTOBER 31, 2024
Vampire malware: draining systems dry This malware creeps in undetected, draining resources and stealing data in the dark. Like vampires, malware strains can operate quietly, leeching data or encrypting files without warning, making ransomware and spyware infections incredibly haunting.

Security Boulevard
SEPTEMBER 25, 2023
The post More iOS Zero Days, More Mercenary Spyware — This Time: Cytrox Predator appeared first on Security Boulevard. Apple Scrambled to Fix 3 More CVEs: Egyptian opposition presidential candidate Ahmed Eltantawy targeted “by the government.
Security Boulevard
JUNE 22, 2022
It could be via virus malware, phishing, social engineering, fileless malware, etc. So, we’re here to talk about one such common tactic: Spyware. What is spyware and how does it work? The post What is Spyware and How to Protect Against it? The post What is Spyware and How to Protect Against it?

Security Boulevard
JUNE 28, 2023
The post Ironic: LetMeSpy Spyware Hackers Were Hacked (by Hackers) appeared first on Security Boulevard. Content warning: Abuse, stalking, controlling behavior, Schadenfreude, irony, doxxing.
Security Boulevard
MAY 3, 2022
The notorious spyware, sold by NSO Group “only to governments,” caused large amounts of data to be exfiltrated. Hacked by NSO Pegasus Spyware (or was it?) appeared first on Security Boulevard. The prime minister and the defense minister of Spain were infected with Pegasus. The post Spanish Govt.

Security Boulevard
AUGUST 22, 2022
NSO, notorious producer of the Pegasus nation-state spyware, is struggling. The post NSO Group Fires CEO — and 100 Staff — in Spyware ‘Streamlining’ appeared first on Security Boulevard. So it’s dumped its CEO, Shalev Hulio, and around 100 employees.
Security Boulevard
JULY 19, 2023
Adds ‘Mercenary Spyware’ Firms to Ban List appeared first on Security Boulevard. European cousins Intellexa and Cytrox essentially banned by Commerce Dept. Predator/ALIEN not welcome in U.S. The post Biden Admin.

Security Boulevard
APRIL 11, 2024
Apple reportedly is alerting iPhone users in 92 countries that they may have been the targets of attacks using “mercenary spyware,” a term that the company is now using in such alerts in place of “state-sponsored” malware. Apple’s messages to affected users said they were being “targeted by a mercenary spyware attacks that is trying.

CyberSecurity Insiders
JANUARY 31, 2021
Regardless of how familiar you are with Information Security, you’ve probably come across the term ‘malware’ countless times. From accessing your business-critical resources and sensitive information to halting business operations and services, a malware infection can quickly become an organization’s worst nightmare come true.

Spinone
MARCH 20, 2019
When considering a fully-featured and well thought out security plan , the human factor is an extremely important part of the equation, and arguably just as important as the technology component of the solution. In this article, we will take a look at cyber security awareness across an SMB organization.

The Last Watchdog
FEBRUARY 28, 2021
Regardless of how familiar you are with Information Security, you’ve probably come across the term ‘malware’ countless times. From accessing your business-critical resources and sensitive information to halting business operations and services, a malware infection can quickly become an organization’s worst nightmare come true.

Security Boulevard
AUGUST 5, 2021
That culprit could be spyware. Spyware is software that tracks your internet surfing and [.]. The post Spyware: What It Is, How It Works, and How to Prevent It appeared first on TechSpective. The post Spyware: What It Is, How It Works, and How to Prevent It appeared first on Security Boulevard.

Security Boulevard
JULY 20, 2021
Yet another zero-day bug in iOS has allowed notorious spyware vendor NSO Group to break into the iPhones of journalists and activists. The post Apple’s Insecure iPhone Lets NSO Hack Journalists (Again) appeared first on Security Boulevard.
SiteLock
AUGUST 27, 2021
In the three years since those first IoT botnet attacks, threats to IoT security have increased to include crypto-jacking , denial of service (DDoS) attacks, and various other types of malware and online malfeasance. What Can You Do to Protect Your Networked Devices? The Bottom Line.
Security Affairs
DECEMBER 21, 2020
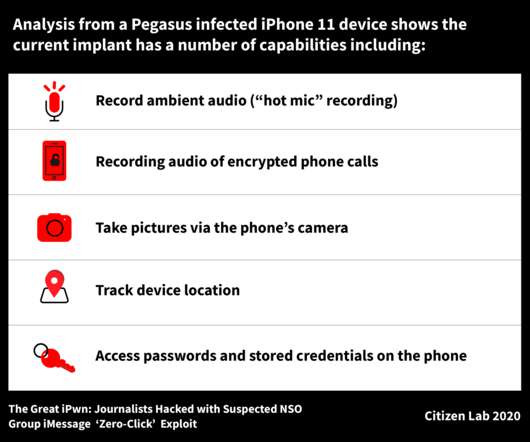
The attackers used an exploit chain named Kismet that was part of the arsenal of the controversial Pegasus spyware that is sold by the surveillance firm NSO Group. “However, the zero-click techniques used against Al Jazeera staff were sophisticated, difficult to detect, and largely focused on the personal devices of reporters.

BH Consulting
OCTOBER 6, 2022
These virtual identities are then used to open accounts, purchase merchandise and services, or further distribute malware for other purposes (e.g., spyware, ransomware).”. Education and awareness are powerful weapons against scammers. Is it up to date on teaching people about the latest criminal techniques? Use common sense.” .

Security Boulevard
MAY 3, 2021
Millions in the UK Targeted by Malware via a DHL Scam Text Message. That link would attempt to install spyware called Flubot, malware designed to steal online banking data from Andriod devices. . That link would attempt to install spyware called Flubot, malware designed to steal online banking data from Andriod devices. .

eSecurity Planet
JUNE 7, 2022
They earned the highest score among providers named "Customer's Choice" in Gartner's 2022 "Voice of the Customer” Security Awareness Computer-Based Training report. Application security, information security, network security, disaster recovery, operational security, etc. Improved Data Security.

Security Boulevard
JANUARY 15, 2025
The post Allstate Violates Drivers Privacy, Texas AG Alleges appeared first on Security Boulevard. Dont Mess With Texas Privacy: We will hold all these companies accountable, rants state attorney general Ken Paxton (pictured).
Responsible Cyber
APRIL 8, 2020
To mitigate this security challenge, businesses must educate their employees on the basics of cybersecurity and include cybersecurity policies in the onboarding process of every new employee. Security awareness should be ongoing and evolving. The Cloud Is not a Safe Haven from Security Flaws.

SecureWorld News
JUNE 15, 2020
After the user enters their credentials into the app and attempt to log in, the credentials are harvested, and security codes can be bypassed.". And here's more on banking trojans: "In another scenario, banking trojans can be used as a “dropper” to install malware onto a user’s phone, particularly spyware (aka stalkerware).
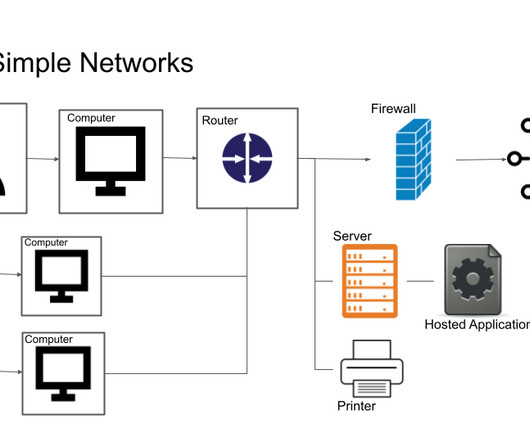
eSecurity Planet
MARCH 14, 2023
Network security excludes any unauthorized access to assets or communication. Better network security monitors for attempts to exceed permissions, unusual behavior from authorized users, and network activity that may indicate compromise or malware activity. or network traffic.
Security Boulevard
JUNE 2, 2023
The post Russia Says NSA Hacked iOS With Apple’s Help — we Triangulate Kaspersky’s Research appeared first on Security Boulevard. Tit-For-Tat Triangulation Trojan Talk: Backdoor inserted at U.S. behest, alleges FSB.
Security Boulevard
MAY 8, 2023
The post Knives Out for TikTok as Journo Reveals her Spy Story appeared first on Security Boulevard. Clock Ticking for U.S. Ban: FT’s Cristina Criddle claims ByteDance spied on her—because she wrote damaging stories about TikTok.

Security Boulevard
DECEMBER 6, 2021
The compromise was carried out, according to Apple, The post Apple Warns of Further Compromises by Israel’s NSO Group appeared first on Security Boulevard. Embassy Kampala mission that their iPhones had been compromised.

Security Boulevard
DECEMBER 17, 2021
The post NSO Zero-Click Exploit: Turing-Complete CPU in Image File appeared first on Security Boulevard. Researchers have reverse engineered NSO group’s recent zero-click iPhone exploit. And it’s a doozy.
Security Boulevard
AUGUST 5, 2024
The post TikTok Abuses Kids, say DoJ and FTC appeared first on Security Boulevard. For You Plague: U.S. Justice Dept. and Federal Trade Commission file lawsuit, alleging TikTok broke the COPPA law, plus a previous injunction.

Security Boulevard
SEPTEMBER 16, 2021
On September 14, 2021, two unrelated incidents demonstrated not only the vulnerability of users to state-sponsored attacks but the fact that defenders are relegated to playing “cat and mouse” with attackers (including government attackers), and the fact that when we provide computer and network attack (CNA) tools just to the “good guys”—we really don’t (..)
Security Boulevard
MARCH 8, 2024
The post TikTok Ban Incoming — but ByteDance Fights Back appeared first on Security Boulevard. Hilltop BillTok: ByteDance mobilizing addicted user base, as U.S. TikTok ban steamrolls through Capitol Hill after unanimous committee vote.

BH Consulting
NOVEMBER 15, 2022
He argued that security works when it costs €100,000 for spyware to hack into a politician’s iPhone. Georgia Bafoutsou of ENISA, the EU’s information security agency, called on those attending to amplify messages about security awareness. “Creating exploits for modern operating systems today is hard.

SecureList
MARCH 8, 2023
To calculate the statistics, the consumer line of Kaspersky’s mobile security solutions has been reviewed according to the Coalition Against Stalkerware’s detection criteria on stalkerware. Other types of monitoring or spyware apps that fall outside of the Coalition’s definition are not included in the report statistics.

Security Boulevard
OCTOBER 28, 2022
Cybersecurity is a battle that all organizations must fight, and there is really no point in doing it alone. Sharing information – the latest attack vectors, shifts in tactics, new-found defenses – helps everyone.

Security Boulevard
OCTOBER 21, 2022
The post TikTok ‘Will’ Spy on US Citizens — Say Sources appeared first on Security Boulevard. TikTok parent ByteDance is planning to track the location of certain targeted individuals on U.S. soil, using a specialist Chinese team.

SecureList
MARCH 13, 2024
Not unlike malware, stalkerware apps are much less frequent on iPhones than on Android devices due to the proprietary and closed nature of iOS. To calculate the statistics, data from the consumer line of Kaspersky’s mobile security solutions was reviewed according to the Coalition Against Stalkerware detection criteria.

Security Boulevard
OCTOBER 9, 2024
The post Digital Crack for Kids: TikTok Sued Again by 14 AGs appeared first on Security Boulevard. For You Plague: TikTok’s in trouble once more—this time, some states complain it’s breaking laws by harvesting children’s data and keeping them addicted.

Security Boulevard
MARCH 18, 2024
The post TikTok ‘Ban’ — ByteDance CEO and EFF are BFFs appeared first on Security Boulevard. 7521 momentum builds: Shou Zi Chew plays for time, while Electronic Frontier Foundation says TikTok-kill bill is DOA.
Security Boulevard
JULY 11, 2022
NSO Group, notorious makers of the notorious Pegasus spyware, has been in acquisition talks with huge defense contractor L3Harris. The post US Gov’t Flip-Flops on NSO Group Sale to L3Harris appeared first on Security Boulevard.

eSecurity Planet
OCTOBER 21, 2022
Anyone who has used a computer for any significant length of time has probably at least heard of malware. Malware has been present in the digital space since the 1980s, with early prank malware like the Morris Worm or the (c)Brain. However, malware is not quite as amusing in a modern context. How Does Malware Work?

SecureWorld News
SEPTEMBER 14, 2021
The Toronto-based research group works to protect journalists and activists from cyberattacks and spyware. And oftentimes they come across new tech-enabled spying efforts from Israel-based NSO Group, which claims to carefully vet sales of its spyware. Citizen Lab discovers zero-day and zero-click spyware. gif” extension.

Herjavec Group
AUGUST 26, 2021
2 – It demonstrates the importance of security awareness training for your employees! After being released in 2003, he uses WiFi to commit attacks, program malware and steal credit card information. This puts customers relying on them to secure their networks at risk. I love it for a few reasons. #1 east coast.

Security Boulevard
JANUARY 21, 2025
Ban appeared first on Security Boulevard. Not For You: Protecting Americans from Foreign Adversary Controlled Applications Act shouldnt be enforced, orders President Trump. The post Trump U-Turn: TikToks On-Again/Off-Again U.S.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content