Are the Police using Smart-Home IoT Devices to Spy on People?
Schneier on Security
OCTOBER 22, 2018
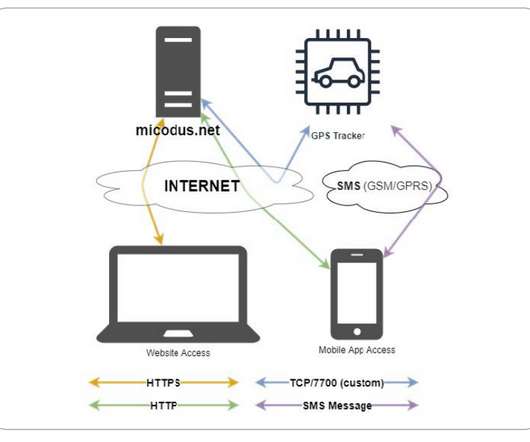
IoT devices are surveillance devices, and manufacturers generally use them to collect data on their customers. Surveillance is still the business model of the Internet, and this data is used against the customers' interests: either by the device manufacturer or by some third-party the manufacturer sells the data to.



































Let's personalize your content