2020 Workshop on Economics of Information Security
Schneier on Security
OCTOBER 14, 2020
The Workshop on Economics of Information Security will be online this year. Register here.
This site uses cookies to improve your experience. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country, we will assume you are from the United States. Select your Cookie Settings or view our Privacy Policy and Terms of Use.
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.
Used for the proper function of the website
Used for monitoring website traffic and interactions
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.

Schneier on Security
OCTOBER 14, 2020
The Workshop on Economics of Information Security will be online this year. Register here.

Schneier on Security
DECEMBER 4, 2020
The workshop on Economics and Information Security is always an interesting conference. This year, it will be online. Here’s the program. Registration is free.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Schneier on Security
JUNE 11, 2019
Last week, I hosted the eighteenth Workshop on the Economics of Information Security at Harvard. Ross Anderson liveblogged the talks.

Schneier on Security
JUNE 27, 2022
I did not attend WEIS this year , but Ross Anderson was there and liveblogged all the talks.

Schneier on Security
FEBRUARY 18, 2021
The 20th Annual Workshop on the Economics of Information Security (WEIS 2021) will be held online in June. We just published the call for papers.

Schneier on Security
MARCH 31, 2024
Of course it was before 2008, when we created the Security and Human Behavior workshop. It was well before 2001, when we created the Workshop on Economics and Information Security. I know I was at the Fast Software Encryption workshop in December 1993, another conference he created.

Security Boulevard
FEBRUARY 17, 2022
The post BSidesAugusta 2021 – Chris Truncer’s ‘Offensive WMI Workshop’ appeared first on Security Boulevard. Many thanks to BSidesAugusta for publishing their outstanding videos from the BSidesAugusta 2021 Conference on the organization’s YouTube channel.

Troy Hunt
NOVEMBER 22, 2019
i speak at conferences around the world and run workshops on how to build more secure software within organisations. i'm a pluralsight author, microsoft regional director and most valued professional (mvp) specialising in online security and cloud development.

Security Boulevard
SEPTEMBER 19, 2021
The post DEF CON 29 Cloud Village – Magno Logan’s ‘Workshop Kubernetes Security 101 Best Practices’ appeared first on Security Boulevard. Our thanks to DEFCON for publishing their tremendous DEFCON Conference Cloud Village videos on the groups' YouTube channel.
Notice Bored
AUGUST 5, 2022
A glossy, nicely-constructed and detailed PowerPoint slide deck by Microsoft Security caught my beady this morning.

Security Boulevard
MAY 14, 2024
Check out these featured classes: Cyber Security Specialist Live Workshop – a total of 64 hours of instruction that cover the breadth of issues for operational specialists. SOC Analyst (Blue Team) Live Workshop – a live, hands-on course designed for front-line tier-1 Security Operations Center analysts.

Adam Shostack
JANUARY 2, 2025
A paper at the Workshop on the Economics of Information Security titled Valuing CyberSecurity Research Datasets focuses on the value of the IMPACT data sharing platform at DHS, and how the availability of data shapes research. There was a really interesting paper at the Workshop on the Economics of Information Security.

Adam Shostack
DECEMBER 7, 2019
Earlier this year, I helped to organize a workshop at Schloss Dagstuhl on Empirical Evaluation of Secure Development Processes. I’m also pleased to say that the workshop report is now available at [link].

Dark Reading
JUNE 14, 2019
Researchers at the Workshop on the Economics of Information Security highlight the cost savings of sharing cybersecurity data and push for greater access to information on breaches, attacks, and incidents.

Security Boulevard
AUGUST 10, 2021
Our thanks to Security BSides Athens for publishing their outstanding Security BSides Athens 2021 Conference videos on the groups' YouTube channel. The post Security BSides Athens 2021 – Workshop: Romansh Yadav”s ‘Attacking Defending Android Apps Training’ appeared first on Security Boulevard.

Security Boulevard
AUGUST 11, 2021
Our thanks to Security BSides Athens for publishing their outstanding Security BSides Athens 2021 Conference videos on the groups' YouTube channel.

Adam Shostack
JULY 26, 2019
There was a really interesting paper at the Workshop on the Economics of Information Security. The paper is “ Valuing CyberSecurity Research Datasets.” ” The paper focuses on the value of the IMPACT data sharing platform at DHS, and how the availability of data shapes the research that’s done.

Security Boulevard
AUGUST 30, 2021
Sources and Sinks interviews car hacker and IoT security expert, Aaron Guzman. Information security is no longer staying on our laptops and in our browsers. As our devices become increasingly interconnected too, we have to start thinking about the security of our IoT devices. Photo by Hiroyoshi Urushima on Unsplash.

Security Boulevard
AUGUST 10, 2021
Our thanks to Security BSides Athens for publishing their outstanding Security BSides Athens 2021 Conference videos on the groups' YouTube channel. The post Security BSides Athens 2021 – Workshop: Juan Escobar’s ‘ICS Intrusion KillChain Explained With Real Simulation’ appeared first on Security Boulevard.

Security Boulevard
AUGUST 10, 2021
Our thanks to Security BSides Athens for publishing their outstanding Security BSides Athens 2021 Conference videos on the groups' YouTube channel.

SecureWorld News
JANUARY 22, 2025
Meet the instructors Larry Wilson , CISSP, CISA, was formerly the Chief Information Security Officer for Sumitomo Pharma Americas, Inc., In the CISO role, Larry was responsible for developing, implementing, and overseeing compliance with the SMPA / WPI / UMass Information Security Policy and Written Information Security Plan (WISP).
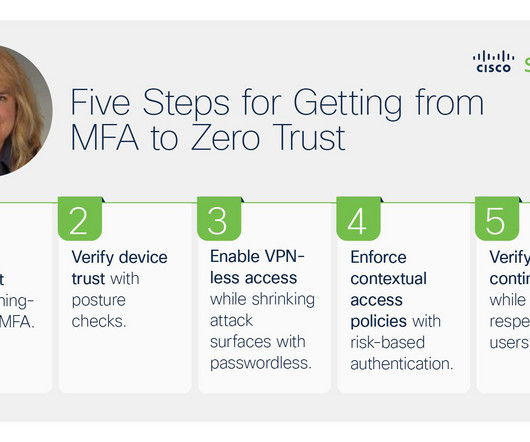
Duo's Security Blog
OCTOBER 6, 2023
For example, outcomes like adapting to external events, creating a security culture, and cost-effective programs, all improve when organizations make progress towards zero trust security (based on survey responses from 4,751 active information security and privacy professionals from 26 countries).
Security Affairs
MAY 9, 2021
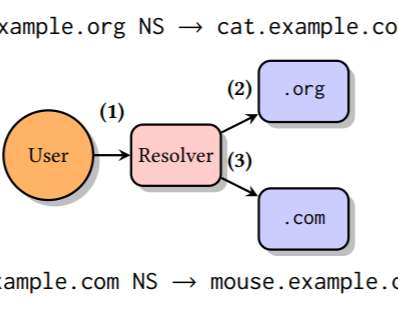
The researchers disclosed the tsuNAME flaw during the DNS OARC35 workshop and shared their findings with impacted organizations giving 90 days to address it before the vulnerability was disclosed. queries/s).” ” reads the research paper published by the experts.
Security Affairs
MAY 16, 2021
The findings about the two attacks will be presented by two research teams at this year’s 15th IEEE Workshop on Offensive Technologies (WOOT’21).

Security Boulevard
MAY 10, 2021
If so, come join us in talks, workshops, and our developer challenge! Bug Hunting Workshop. Hunt bugs, detect malware, and win some snacks! Are you going to the RSA conference coming up on May 17th to 20th? Here’s what we are up to at RSA and RSA DevOpsConnect. Photo by Adam Solomon on Unsplash.

CyberSecurity Insiders
MAY 27, 2021
Registration for the 11th annual (ISC)² Security Congress is now open! The renowned global three-day conference, focused on continuing education for cybersecurity professionals and information security specialists, will be hosted as a hybrid event for the first time in 2021.

The Last Watchdog
NOVEMBER 28, 2023
But that’s not enough to assuage their anxiety and instill confidence that they’re well protected against security threats. Their top areas of concern include cybersecurity risk (58%), information security risk (53%) and compliance risk (39%). Human error is among the top causes of security breaches.

CyberSecurity Insiders
OCTOBER 6, 2022
The CISM or Certified Information Security Manager certification is another highly coveted credential that is often key for accessing higher-paid roles within the industry. It includes practical skills with performance-based questions and is designed for those looking to move from entry-level to intermediate cybersecurity roles.

IT Security Guru
SEPTEMBER 25, 2023
Businesses and other organisations are being pushed both by customers and regulators to evidence how they are keeping their information secure. Consumers have increasing expectations of organisations that any information they provide will be kept safe and actively avoid organisations that have a history of breaches.

SecureWorld News
FEBRUARY 8, 2021
The NIST Cybersecurity Framework (CSF) helps thousands of organizations around the world to better understand and improve their information security posture. It recently announced it is making new, bold pushes relating to information security and privacy for 2021 and beyond. Trustworthy platforms.
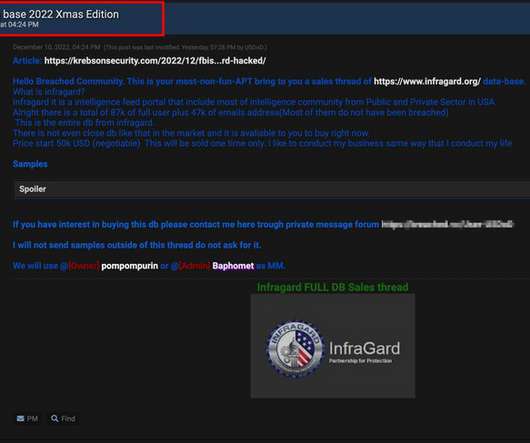
Security Affairs
DECEMBER 15, 2022
Through seamless collaboration, InfraGard connects owners and operators within critical infrastructure to the FBI, to provide education, information sharing, networking, and workshops on emerging technologies and threats. “InfraGard, a program run by the U.S.

CyberSecurity Insiders
APRIL 13, 2021
Domain 1: Information Security Risk Management Program. Information Security Risk Management Program. Domain 2: Categorization of Information Systems. Scope of the Information System. Domain 3: Selection of Security Controls. CAP as of August 15, 2021. %. org with your member ID #. What is Changing?

Security Affairs
MARCH 28, 2023
“The identified use cases that emerged from the workshops Europol carried out with its experts are by no means exhaustive. . “As such, ChatGPT can be used to learn about a vast number of potential crime areas with no prior knowledge, ranging from how to break into a home, to terrorism, cybercrime and child sexual abuse.”

CyberSecurity Insiders
SEPTEMBER 24, 2021
Even with high-level security measures, no one is safe from such threats. That is why most companies hire professional information security services to mitigate the risks arising from data breaches. Therefore, you need to invest in your employees by conducting cybersecurity workshops and training regularly.

Duo's Security Blog
JULY 13, 2022
Every time we had a workshop, one thing we constantly heard from people was, ‘That was so good! We had the space and the structure that allowed us to exchange so much information and do things together collaboratively.” How do design thinking principles uniquely benefit information security?

Troy Hunt
JANUARY 3, 2019
So yes, travel went up but I also did a bunch of remote workshops which helped keep that down, as well sending Scott Helme to run in-person ones that contributed to keeping me on Aussie soil. Flight wise, App in the Air captured things in a nice visual fashion: That's up 15,000km, 17 hours and 3 flights from last year.

Centraleyes
MARCH 13, 2025
Enhanced Governance Requirements Entities must appoint a qualified Chief Information Security Officer (CISO) with a direct reporting line to the board of directors. phishing attacks), and their specific roles in protecting sensitive information. These changes took effect in 2024. Here are the highlights: 1.

SecureWorld News
JULY 25, 2023
As organizations across industries grapple with escalating cyber risks, the demand for skilled information security professionals has skyrocketed. You can stay up to date with the latest trends, technologies, and best practices in the cybersecurity field through conferences, webinars, workshops, and other learning opportunities.

CyberSecurity Insiders
NOVEMBER 9, 2021
They are hosting a joint meeting soon with IAPP to bring privacy and cyber professionals together, formalizing a personalized mentorship program, starting a CCSP study group, providing a heavily discounted CISSP training class and a resume workshop. We caught up with Ken to discuss the impact and learn more about their upcoming events.

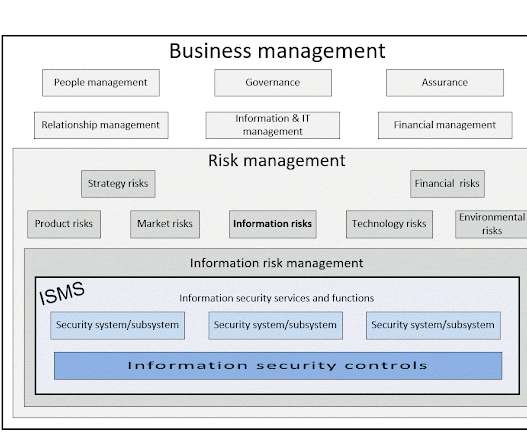
Centraleyes
MARCH 17, 2025
This guide breaks down the fundamental principles and risk assessment methodologies in information security. Instead, it uses descriptive labels like “High,” “Medium,” or “Low” to evaluate risks based on expert opinions, brainstorming sessions, or workshops. What Is Risk Assessment?
Thales Cloud Protection & Licensing
SEPTEMBER 27, 2023
You’ll find Thales on stand 152, level Daghilev, and don’t miss our workshop at 3pm on October 11th as Didier Espinet, Chief Information Security Officer, Thales DIS and Laini Cultier, IAM expert at Thales will present a session entitled “Trust and Security: The Keys to Success in the Public Cloud”.

CyberSecurity Insiders
MARCH 25, 2021
Although this does take time, with training and upskilling programs , insightful workshops, and “Hacker Fridays” (where employees can try to hack a specific smart device), team members will become more capable of dealing with the new diagnostics support work, as well as any general IoT problems.
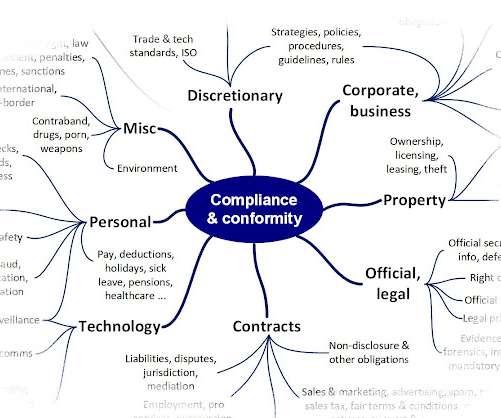
Notice Bored
JULY 4, 2022
At the CISO, Information Security Manager or Privacy Officer level, the view is no less scary despite narrower knowledge gaps. and that's a jolly good reason to arrange a management workshop or study to explore the entire mind map, talking it through and carving it up appropriately. We're definitely in the discomfort zone here.
Lenny Zeltser
JANUARY 6, 2021
You’ll also find my Analyzing Malicious Documents cheat sheet useful. Continue Reading, Experimenting, and Learning. Reading and watching the resources mentioned above will help you learn about malware analysis approaches, but you’ll need to find time for focused, deliberate practice to learn how to apply them.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content