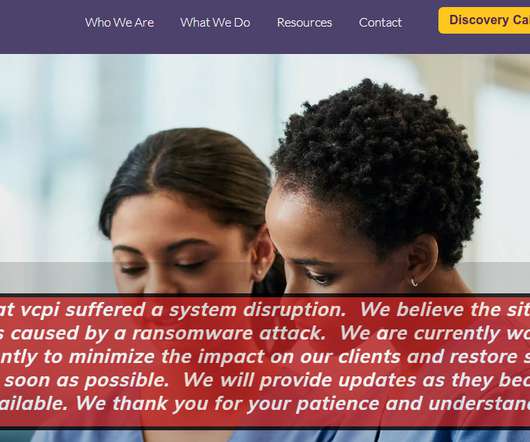
UnitedHealth almost doubles victim numbers from massive Change Healthcare data breach
Malwarebytes
JANUARY 27, 2025
UnitedHealth says it now estimates that the data breach on its subsidiary Change Healthcare affected 190 million people, nearly doubling its previous estimate from October. In October, this was largely confirmed when Change Healthcare reported a number of 100,000,000 affected individuals. Change your password.












































Let's personalize your content