Forging the Path to Continuous Audit Readiness
CyberSecurity Insiders
JANUARY 9, 2023
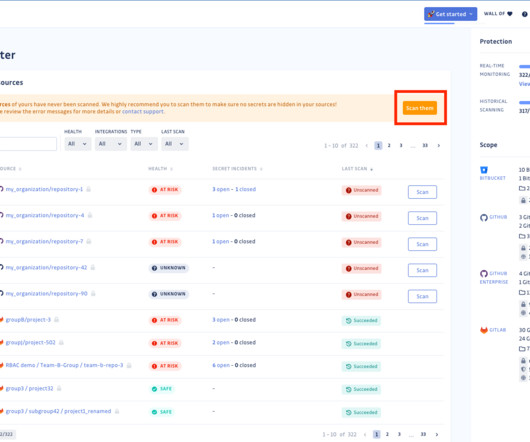
Second, the tasks required to ascertain control and policy compliance details, resolve violations and provide adherence proof are resource intensive and error prone. Protection mechanisms incorporates a wide variety of cyber defenses such as malware, encryption, vulnerability management and firewall technologies.












Let's personalize your content