Experts Flag Security, Privacy Risks in DeepSeek AI App
Krebs on Security
FEBRUARY 6, 2025
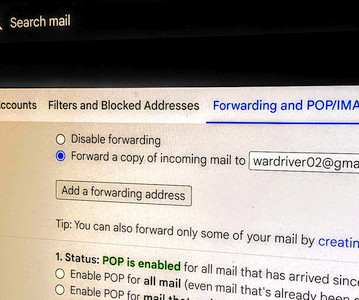
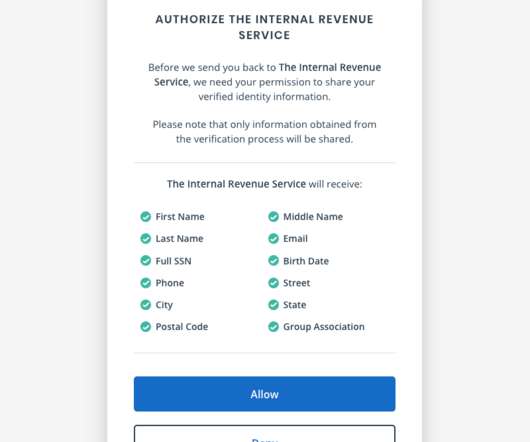
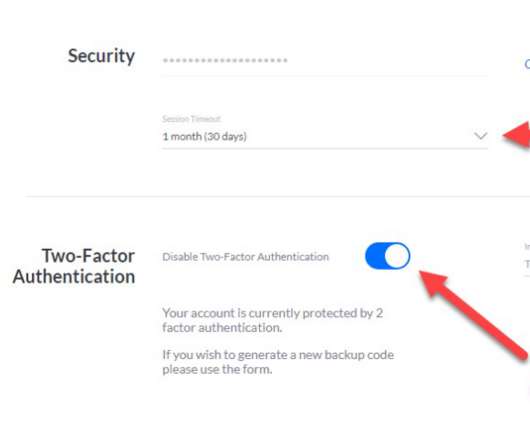
New mobile apps from the Chinese artificial intelligence (AI) company DeepSeek have remained among the top three “free” downloads for Apple and Google devices since their debut on Jan. ” Hoog said the app does selectively encrypt portions of the responses coming from DeepSeek servers. . Image: NowSecure.









































Let's personalize your content