Introducing Secure Firewall version 7.3
Cisco Security
DECEMBER 14, 2022
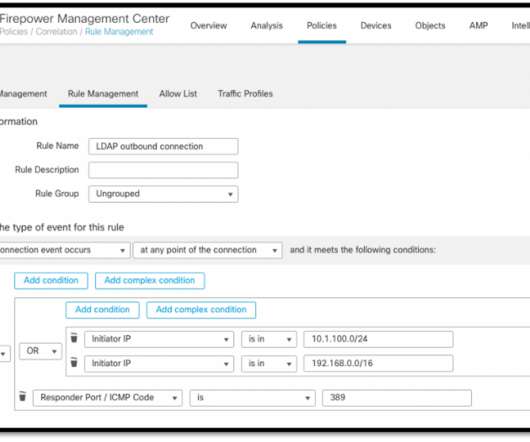
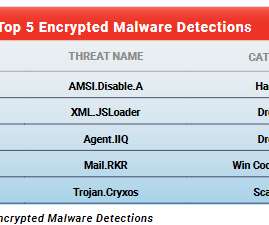
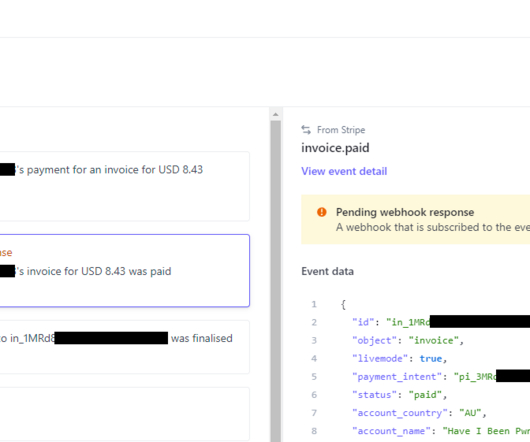
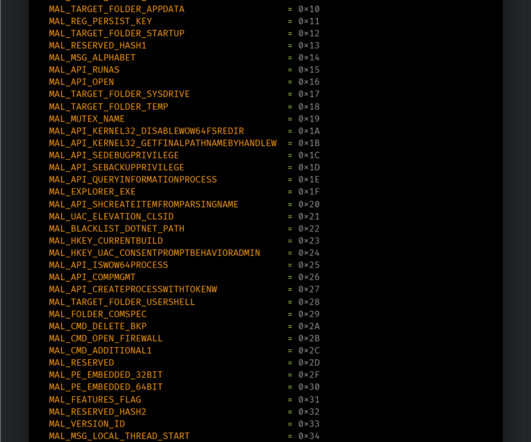
Introduction to Cisco Secure Firewall 7.3. Cisco’s latest release of Secure Firewall operating system, Secure Firewall Threat Defence Version 7.3, addresses key concerns for today’s firewall customers. Further enhancements to Cisco’s Encrypted Visibility Engine (EVE), first launched a year ago in 7.1,







































Let's personalize your content