Problems with Georgia’s Voter Registration Portal
Schneier on Security
AUGUST 7, 2024
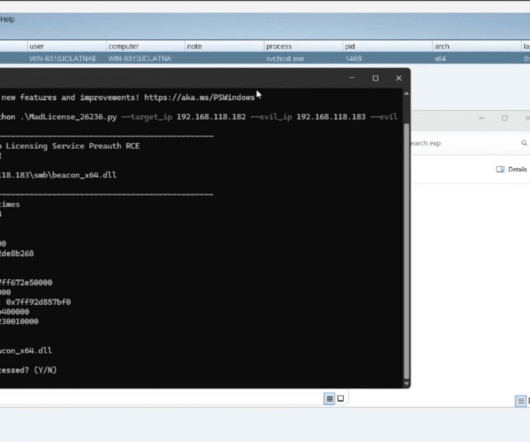
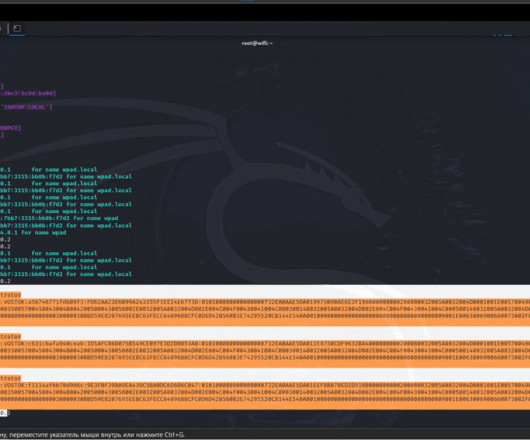
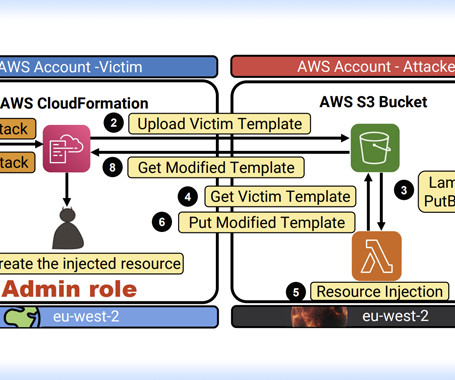
It’s possible to cancel other people’s voter registration: On Friday, four days after Georgia Democrats began warning that bad actors could abuse the state’s new online portal for canceling voter registrations, the Secretary of State’s Office acknowledged to ProPublica that it had identified multiple such attempts… …the portal suffered at least two security glitches that briefly exposed voters’ dates of birth, the last four digits of their Social Securit






















Let's personalize your content