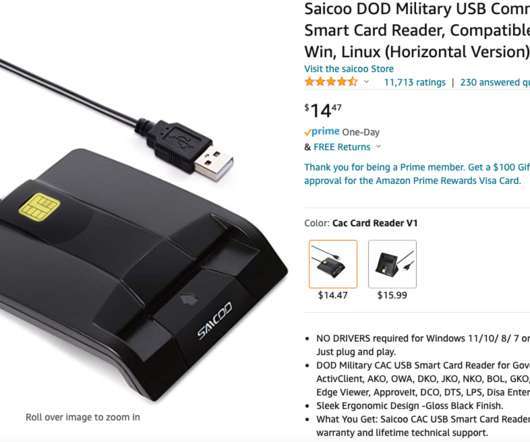
When Your Smart ID Card Reader Comes With Malware
Krebs on Security
MAY 17, 2022
Millions of U.S. government employees and contractors have been issued a secure smart ID card that enables physical access to buildings and controlled spaces, and provides access to government computer networks and systems at the cardholder’s appropriate security level.





 271
271 










Let's personalize your content