New Privacy Features in iOS 14
Schneier on Security
OCTOBER 7, 2020
A good rundown.

Krebs on Security
OCTOBER 9, 2020
A week ago, KrebsOnSecurity broke the news that someone was attempting to disrupt the Trickbot botnet , a malware crime machine that has infected millions of computers and is often used to spread ransomware. A new report Friday says the coordinated attack was part of an operation carried out by the U.S. military’s Cyber Command. Image: Shuttstock.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Troy Hunt
OCTOBER 9, 2020
It's a bit of a mega one this week running over the 1-hour mark, but there's been an awful lot happen during the last week that I reckon is of interest. There's a decidedly adult theme running across the topics not by design, but just by pure coincidence between the Grindr incident, a query I got regarding erasing one's adult website browsing history and the IoT male chastity device full of security holes and potential requiring a grinder (not Grindr!

Tech Republic Security
OCTOBER 9, 2020
Hackers accidentally allowed into company software by security noncompliant employees cost businesses millions annually; we asked experts to weigh in on best safety practices.

Advertisement
Many cybersecurity awareness platforms offer massive content libraries, yet they fail to enhance employees’ cyber resilience. Without structured, engaging, and personalized training, employees struggle to retain and apply key cybersecurity principles. Phished.io explains why organizations should focus on interactive, scenario-based learning rather than overwhelming employees with excessive content.

Schneier on Security
OCTOBER 5, 2020
Interesting usability study: “ More Than Just Good Passwords? A Study on Usability and Security Perceptions of Risk-based Authentication “: Abstract : Risk-based Authentication (RBA) is an adaptive security measure to strengthen password-based authentication. RBA monitors additional features during login, and when observed feature values differ significantly from previously seen ones, users have to provide additional authentication factors such as a verification code.

Krebs on Security
OCTOBER 8, 2020
There’s an old adage in information security: “Every company gets penetration tested, whether or not they pay someone for the pleasure.” Many organizations that do hire professionals to test their network security posture unfortunately tend to focus on fixing vulnerabilities hackers could use to break in. But judging from the proliferation of help-wanted ads for offensive pentesters in the cybercrime underground, today’s attackers have exactly zero trouble gaining that in
Cyber Security Informer brings together the best content for cyber security professionals from the widest variety of industry thought leaders.

Tech Republic Security
OCTOBER 8, 2020
The goal is to not only secure your remote devices and endpoints but to make that security part of your overall strategy, says NordVPN Teams.

Schneier on Security
OCTOBER 6, 2020
Previously I have written about the Swedish-owned Swiss-based cryptographic hardware company: Crypto AG. It was a CIA-owned Cold War operation for decades. Today it is called Crypto International , still based in Switzerland but owned by a Swedish company. It’s back in the news : Late last week, Swedish Foreign Minister Ann Linde said she had canceled a meeting with her Swiss counterpart Ignazio Cassis slated for this month after Switzerland placed an export ban on Crypto International , a

Krebs on Security
OCTOBER 7, 2020
September featured two stories on a phony tech investor named John Bernard , a pseudonym used by a convicted thief named John Clifton Davies who’s fleeced dozens of technology companies out of an estimated $30 million with the promise of lucrative investments. Those stories prompted a flood of tips from Davies’ victims that paint a much clearer picture of this serial con man and his cohorts, including allegations of hacking, smuggling, bank fraud and murder.

Security Affairs
OCTOBER 5, 2020
Threat actors have hacked at least three Swiss universities, including the University of Basel and managed to drain employee salary transfers. Threat actors have managed to steal employee salary payments at several Swiss universities, including the University of Basel. “According to our information, several universities in Switzerland have been affected,” explained Martina Weiss, Secretary General of the Rectors’ Conference of the Swiss Universities.

Advertisement
The DHS compliance audit clock is ticking on Zero Trust. Government agencies can no longer ignore or delay their Zero Trust initiatives. During this virtual panel discussion—featuring Kelly Fuller Gordon, Founder and CEO of RisX, Chris Wild, Zero Trust subject matter expert at Zermount, Inc., and Principal of Cybersecurity Practice at Eliassen Group, Trey Gannon—you’ll gain a detailed understanding of the Federal Zero Trust mandate, its requirements, milestones, and deadlines.
Tech Republic Security
OCTOBER 7, 2020
Bad actors use machine learning to break passwords more quickly and build malware that knows how to hide, experts warn.

CompTIA on Cybersecurity
OCTOBER 6, 2020
Interested in a career in cybersecurity? Find out more about the top nine cybersecurity job titles in the United States as told by Cyberseek, and understand what education, certifications and skills you need to start a career in cybersecurity.

Threatpost
OCTOBER 8, 2020
Two flaws in Microsoft's cloud-based Azure App Services could have allowed server-side forgery request (SSFR) and remote code-execution attacks.
Security Affairs
OCTOBER 5, 2020
Security researchers provided technical details about an IoT botnet dubbed Ttint that has been exploiting two zero-days in Tenda routers. Security researchers at Netlab, the network security division Qihoo 360, have published a report that details an IoT botnet dubbed Ttint. The experts are monitoring the Mirai-based botnet since November 2019 and observed it exploiting two Tenda router 0-day vulnerabilities to spread a Remote Access Trojan (RAT).

Advertisement
Keeper Security is transforming cybersecurity for people and organizations around the world. Keeper’s affordable and easy-to-use solutions are built on a foundation of zero-trust and zero-knowledge security to protect every user on every device. Our next-generation privileged access management solution deploys in minutes and seamlessly integrates with any tech stack to prevent breaches, reduce help desk costs and ensure compliance.

Tech Republic Security
OCTOBER 7, 2020
A survey of business leaders by PwC finds the pandemic is causing rapid changes in the roles CISOs play, and offers five tips for ensuring that security remains stable as we enter a new normal.
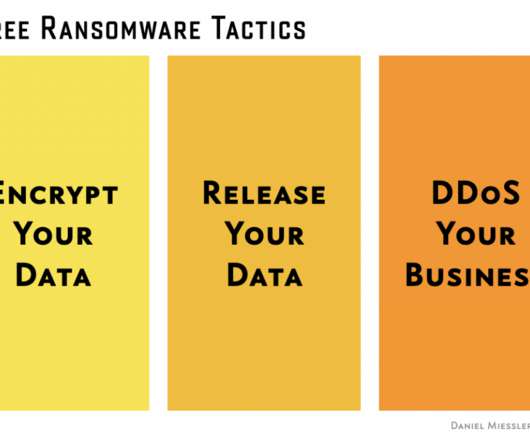
Daniel Miessler
OCTOBER 4, 2020
I’ve been writing a lot on ransomware recently , and wanted to comment on an interesting new development in attackers’ toolchests. At first they started with: If you don’t pay, you won’t get your data back. This is the original ransomware tactic. It’s a denial of service against your data. You pay, and you (sometimes) get your data back.

Threatpost
OCTOBER 9, 2020
Immersive Labs Researcher takes advantage of lax Fitbit privacy controls to build a malicious spyware watch face.

Security Affairs
OCTOBER 3, 2020
University Hospital New Jersey paid a $670,000 ransom this month to prevent the leak of 240 GB of stolen data, including patient information. The University Hospital New Jersey (UHNJ) in Newark (New Jersey) has finally paid a $670,000 ransom to prevent the publishing of 240 GB of stolen data, including patient info. In September, systems at the University Hospital New Jersey (UHNJ) were encrypted with the SunCrypt ransomware , threat actors also stolen documents from the institution and leaked

Advertisement
Many software teams have migrated their testing and production workloads to the cloud, yet development environments often remain tied to outdated local setups, limiting efficiency and growth. This is where Coder comes in. In our 101 Coder webinar, you’ll explore how cloud-based development environments can unlock new levels of productivity. Discover how to transition from local setups to a secure, cloud-powered ecosystem with ease.

Tech Republic Security
OCTOBER 7, 2020
Remote work will lead to more phishing attacks and threats to accounting and marketing departments, according to IT security managers.
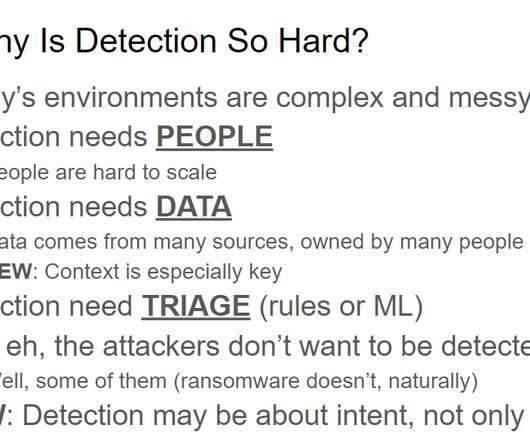
Anton on Security
OCTOBER 7, 2020
While creating a recent presentation, I needed a slide on “threat detection is hard.” And it got me thinking, why is threat detection so hard for so many organizations today? We can trace the “cyber” threat detection to 1986 ( “Cuckoo’s Egg” ) and 1987 ( first IDS ) and perhaps even earlier events (like viruses of the early 1980s). This means we are “celebrating” ~35 years of cyber threat detection.

Adam Shostack
OCTOBER 7, 2020
I haven’t talked about it much, but I spent the first few months of the pandemic learning how to deliver effective training in a distributed (online) model. I’m really proud that our distributed class NPS customer satisfaction scores are now comparable to our in-person classes. Also it’s been a lot of hard work, and in addition to our core classes (Threat Modeling for Architects and Threat Modeling in Depth), we now have classes for champs and trainers.

Security Affairs
OCTOBER 4, 2020
Visa revealed that two unnamed North American hospitality merchants have been infected with some strains of point-of-sale (POS) malware. US payments processor Visa revealed that two North American hospitality merchants have been hacked, threat actors infected the systems of the two unnamed organizations with some strains of point-of-sale (POS) malware.

Advertisement
How many people would you trust with your house keys? Chances are, you have a handful of trusted friends and family members who have an emergency copy, but you definitely wouldn’t hand those out too freely. You have stuff that’s worth protecting—and the more people that have access to your belongings, the higher the odds that something will go missing.

Tech Republic Security
OCTOBER 7, 2020
The phishing page tries to obtain email credentials, Social Security numbers, driver's license numbers, and tax numbers, says Armorblox.

WIRED Threat Level
OCTOBER 6, 2020
The Checkm8 vulnerability that exposed years of iPhones to jailbreaking has finally been exploited in Macs as well.

Threatpost
OCTOBER 9, 2020
Ethical hackers so far have earned nearly $300K in payouts from the Apple bug-bounty program for discovering 55 bugs, 11 of them critical, during a three-month hack.

Security Affairs
OCTOBER 8, 2020
Cybersecurity researchers from Cyble have spotted a threat actor sharing leaked data of Airlink International UAE for free on two different platforms. Cybersecurity researchers from Cyble have found a threat actor sharing leaked data of Airlink International UAE for free on two platforms on the dark web. The availability of the data on the dark web could pose organizations to serious risk, threat actors could use this data to carry out multiple malicious attacks.

Advertisement
After a year of sporadic hiring and uncertain investment areas, tech leaders are scrambling to figure out what’s next. This whitepaper reveals how tech leaders are hiring and investing for the future. Download today to learn more!

Tech Republic Security
OCTOBER 6, 2020
Data breaches occur despite tight security. Arctic Wolf explains how to increase your security effectiveness.

WIRED Threat Level
OCTOBER 5, 2020
Seven distinct factors between now and the election threaten to combine, compound, and reinforce each other in unpredictable ways.

Threatpost
OCTOBER 7, 2020
Researchers disclosed the 'WarezTheRemote' attack, affecting Comcast's XR11 voice remote control.

Security Affairs
OCTOBER 4, 2020
HP published details of three vulnerabilities in the HP Device Manager that could be exploited by attackers to take over Windows systems. HP released a security advisory that includes details for three critical and high severity vulnerabilities, tracked as CVE-2020-6925, CVE-2020-6926, and CVE-2020-6927, that impact the HP Device Manager. The IT giant revealed that an attacker could exploit the vulnerabilities to take over Windows systems.

Advertiser: Revenera
In a recent study, IDC found that 64% of organizations said they were already using open source in software development with a further 25% planning to in the next year. Most organizations are unaware of just how much open-source code is used and underestimate their dependency on it. As enterprises grow the use of open-source software, they face a new challenge: understanding the scope of open-source software that's being used throughout the organization and the corresponding exposure.
Let's personalize your content