Many Cyber Attacks Begin by Breaking Human Trust
Lohrman on Security
OCTOBER 1, 2023
Sophisticated social engineering attacks have led to hundreds of data breaches this year. What can be done? And what new resources can help?

Lohrman on Security
OCTOBER 1, 2023
Sophisticated social engineering attacks have led to hundreds of data breaches this year. What can be done? And what new resources can help?

Schneier on Security
OCTOBER 3, 2023
Turns out pumps at gas stations are controlled via Bluetooth, and that the connections are insecure. No details in the article, but it seems that it’s easy to take control of the pump and have it dispense gas without requiring payment. It’s a complicated crime to monetize, though. You need to sell access to the gas pump to others.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Troy Hunt
OCTOBER 4, 2023
Imagine you wanted to buy some s**t on the internet. Not the metaphorical kind in terms of "I bought some random s**t online", but literal s**t. Turds. Faeces. The kind of thing you never would have thought possible to buy online until. Shitexpress came along. Here's a service that enables you to send an actual piece of smelly s**t to "An irritating colleague.

Krebs on Security
OCTOBER 2, 2023
Many organizations — including quite a few Fortune 500 firms — have exposed web links that allow anyone to initiate a Zoom video conference meeting as a valid employee. These company-specific Zoom links, which include a permanent user ID number and an embedded passcode, can work indefinitely and expose an organization’s employees, customers or partners to phishing and other social engineering attacks.

Advertisement
Many cybersecurity awareness platforms offer massive content libraries, yet they fail to enhance employees’ cyber resilience. Without structured, engaging, and personalized training, employees struggle to retain and apply key cybersecurity principles. Phished.io explains why organizations should focus on interactive, scenario-based learning rather than overwhelming employees with excessive content.

Joseph Steinberg
OCTOBER 4, 2023
CyberSecurity and Artificial Intelligence Expert , Joseph Steinberg, will keynote the upcoming Securing the Future: Cloud, Cybersecurity, and AI Summit , taking place on Wednesday, October 11, 2023, in Pennsylvania, USA. The summit, sponsored by Avail Technology Solutions, will allow participants to learn about the latest advancements and trends in cloud technology, cybersecurity practices, and the exciting world of Artificial Intelligence (AI) — topics that Steinberg will cover in his key

Schneier on Security
OCTOBER 4, 2023
Malicious ads are creeping into chatbots.
Cyber Security Informer brings together the best content for cyber security professionals from the widest variety of industry thought leaders.
Krebs on Security
SEPTEMBER 30, 2023
Earlier this week, KrebsOnSecurity revealed that the darknet website for the Snatch ransomware group was leaking data about its users and the crime gang’s internal operations. Today, we’ll take a closer look at the history of Snatch, its alleged founder, and their claims that everyone has confused them with a different, older ransomware group by the same name.

Joseph Steinberg
OCTOBER 4, 2023
A little over a decade ago I wrote a piece for Forbes describing a method of protecting electronic communications from unauthorized access, through the hiding of message contents within photos and video files. At the time, I even created a contest – embedding an unencrypted Amazon gift card number within an image displayed on the Forbes website alongside my article; despite my having provided clues as to what was hidden, and in what image it was hidden, and despite a hundred thousand peopl

Schneier on Security
OCTOBER 2, 2023
The NSA is starting a new artificial intelligence security center: The AI security center’s establishment follows an NSA study that identified securing AI models from theft and sabotage as a major national security challenge, especially as generative AI technologies emerge with immense transformative potential for both good and evil. Nakasone said it would become “NSA’s focal point for leveraging foreign intelligence insights, contributing to the development of best practices g

Tech Republic Security
OCTOBER 6, 2023
Microsoft, the Dark Web and the name John Malkovich all factor into this EvilProxy phishing attack. The good news is there are steps IT can take to mitigate this security threat.

Advertisement
The DHS compliance audit clock is ticking on Zero Trust. Government agencies can no longer ignore or delay their Zero Trust initiatives. During this virtual panel discussion—featuring Kelly Fuller Gordon, Founder and CEO of RisX, Chris Wild, Zero Trust subject matter expert at Zermount, Inc., and Principal of Cybersecurity Practice at Eliassen Group, Trey Gannon—you’ll gain a detailed understanding of the Federal Zero Trust mandate, its requirements, milestones, and deadlines.

The Last Watchdog
OCTOBER 5, 2023
Editor’s note: I recently had the chance to participate in a discussion about the overall state of privacy and cybersecurity with Erin Kapczynski, OneRep’s senior vice president of B2B marketing. OneRep provides a consumer service that scrubs your personal information from Google and dozens of privacy-breaching websites. Here is Erin’s Q&A column, which originally went live on OneRep’s well-done blog.

Thales Cloud Protection & Licensing
OCTOBER 2, 2023
Cybersecurity Awareness Month 2023 – What it is and why we should be aware madhav Tue, 10/03/2023 - 05:33 The inception of Cybersecurity Awareness Month in 2004 came at a critical juncture in our technological history. As we are well and truly in the digital-first age, the need for robust cybersecurity measures is glaringly evident. Though significant, the early days' threats vastly differed from today's sophisticated cyberattacks.

Schneier on Security
OCTOBER 6, 2023
Well designed and well timed deepfake or two Slovakian politicians discussing how to rig the election: Šimečka and Denník N immediately denounced the audio as fake. The fact-checking department of news agency AFP said the audio showed signs of being manipulated using AI. But the recording was posted during a 48-hour moratorium ahead of the polls opening, during which media outlets and politicians are supposed to stay silent.

Tech Republic Security
OCTOBER 5, 2023
Microsoft OneDrive is adding new SharePoint features and will let the Copilot AI summarize and interpret files.

Advertisement
Keeper Security is transforming cybersecurity for people and organizations around the world. Keeper’s affordable and easy-to-use solutions are built on a foundation of zero-trust and zero-knowledge security to protect every user on every device. Our next-generation privileged access management solution deploys in minutes and seamlessly integrates with any tech stack to prevent breaches, reduce help desk costs and ensure compliance.

The Last Watchdog
OCTOBER 2, 2023
Surrounded by the invisible hum of electromagnetic energy, we’ve harnessed its power to fuel our technological marvels for decades. Related: MSFT CEO calls for regulating facial recognition tech Tesla’s visionary insights from 1900 hinted at the potential, and today, we bask in the glow of interconnected networks supporting our digital lives.

Bleeping Computer
OCTOBER 6, 2023
23andMe has confirmed to BleepingComputer that it is aware of user data from its platform circulating on hacker forums and attributes the leak to a credential-stuffing attack. [.

WIRED Threat Level
OCTOBER 6, 2023
At least a million data points from 23andMe accounts appear to have been exposed on BreachForums. While the scale of the campaign is unknown, 23andMe says it's working to verify the data.

Tech Republic Security
OCTOBER 2, 2023
Don't be surprised when connecting multiple iPhones to one Apple ID. Learn how to prevent common errors and issues with this guide.

Advertisement
Many software teams have migrated their testing and production workloads to the cloud, yet development environments often remain tied to outdated local setups, limiting efficiency and growth. This is where Coder comes in. In our 101 Coder webinar, you’ll explore how cloud-based development environments can unlock new levels of productivity. Discover how to transition from local setups to a secure, cloud-powered ecosystem with ease.

We Live Security
OCTOBER 5, 2023
ESET researchers uncover a cyberespionage campaign that they called Operation Jacana and that targeted a governmental entity in Guyana.
Security Affairs
OCTOBER 4, 2023
Sony Interactive Entertainment has notified current and former employees and their family members about a data breach. Sony Interactive Entertainment (SIE) has notified current and former employees and their family members about a data breach that exposed their personal information. Sony notified about 6,800 individuals, it confirmed that the security breach was the result of the exploitation of the zero-day vulnerability CVE-2023-34362 in the MOVEit Transfer platform.

The Hacker News
OCTOBER 4, 2023
Apple on Wednesday rolled out security patches to address a new zero-day flaw in iOS and iPadOS that it said has come under active exploitation in the wild. Tracked as CVE-2023-42824, the kernel vulnerability could be abused by a local attacker to elevate their privileges. The iPhone maker said it addressed the problem with improved checks.

Tech Republic Security
OCTOBER 3, 2023
This high-speed, unlimited VPN offers quality connections all over the globe. Get huge savings now when you sign up for life at TechRepublic Academy.

Advertisement
How many people would you trust with your house keys? Chances are, you have a handful of trusted friends and family members who have an emergency copy, but you definitely wouldn’t hand those out too freely. You have stuff that’s worth protecting—and the more people that have access to your belongings, the higher the odds that something will go missing.
Duo's Security Blog
OCTOBER 6, 2023
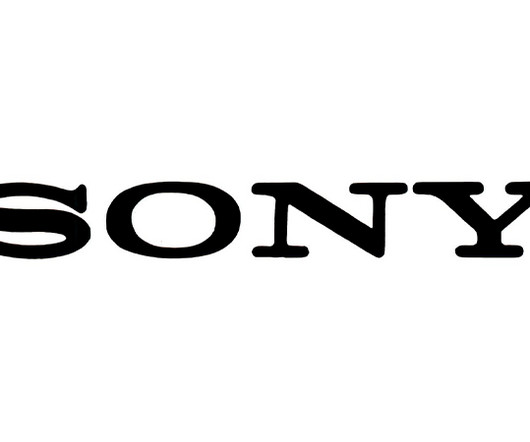
When organizations started to embark on zero trust security back in 2020, it was in response to a dramatic and unforeseen change – the public health crisis. This made zero trust access a ‘must have’ exercise just to keep businesses operational. Securing remote user access became the first use case for adopting zero trust security principles. At the time, expediency rather than zero trust maturity became the guiding principle.
Security Affairs
OCTOBER 3, 2023
Researchers have identified the exfiltration infrastructure of a LockBit affiliate while investigating a LockBit extortion incident that occurred in Q3 2023. Executive Summary We investigated a recent LockBit extortion incident that occurred in Q3 2023, which involved an unusual FTP server located in Moscow. The hostname of this server was identified as matching many hostnames found in various posts on the LockBit leak site.

The Hacker News
OCTOBER 3, 2023
Firewall and distributed denial-of-service (DDoS) attack prevention mechanisms in Cloudflare can be circumvented by exploiting gaps in cross-tenant security controls, defeating the very purpose of these safeguards, it has emerged.

Tech Republic Security
OCTOBER 3, 2023
It doesn’t matter whether your organization is a huge multinational business enterprise or a one-person operation. At some point, your computer networks and systems will be attacked by someone with criminal intent. Cybersecurity attacks, in all their various forms, are inevitable and relentless. This quick glossary from TechRepublic Premium explains the terminology behind the most.

Advertisement
After a year of sporadic hiring and uncertain investment areas, tech leaders are scrambling to figure out what’s next. This whitepaper reveals how tech leaders are hiring and investing for the future. Download today to learn more!

Malwarebytes
OCTOBER 2, 2023
Post anything publicly on Facebook and Instagram? Meta has likely been using those posts to train its AI, according to the company's top policy executive. In an interview with Reuters , Meta President of Global Affairs Nick Clegg said the company used the public posts to train the LLM (large language model) that feeds into its new Meta AI virtual assistant.
Security Affairs
OCTOBER 5, 2023
NATO is investigating claims that a group called SiegedSec has breached its systems and leaked a cache of unclassified documents online. NATO announced it is investigating claims that a politically motivated threat actor called SiegedSec has breached its systems and leaked unclassified documents online. “NATO cyber experts are actively addressing incidents affecting some unclassified NATO websites,” reads a statement issued by s NATO official to media outlets.

WIRED Threat Level
OCTOBER 4, 2023
Elon Musk’s brain-chip startup conducted years of tests at UC Davis, a public university. A WIRED investigation reveals how Neuralink and the university keep the grisly images of test subjects hidden.

Tech Republic Security
OCTOBER 6, 2023
Read our comprehensive review of IPVanish VPN. Discover its features, pricing, and more to determine if it meets your online security and privacy needs.

Advertiser: Revenera
In a recent study, IDC found that 64% of organizations said they were already using open source in software development with a further 25% planning to in the next year. Most organizations are unaware of just how much open-source code is used and underestimate their dependency on it. As enterprises grow the use of open-source software, they face a new challenge: understanding the scope of open-source software that's being used throughout the organization and the corresponding exposure.
Let's personalize your content