Hacking ChatGPT by Planting False Memories into Its Data
Schneier on Security
OCTOBER 1, 2024
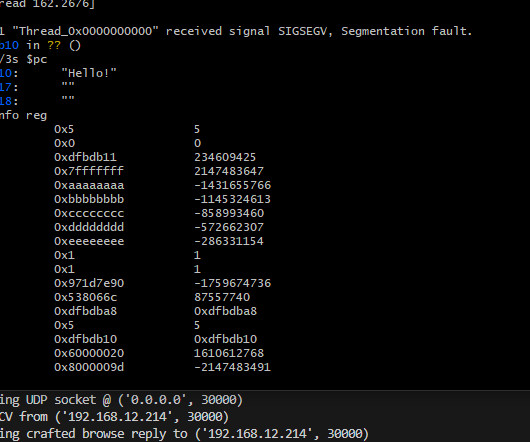
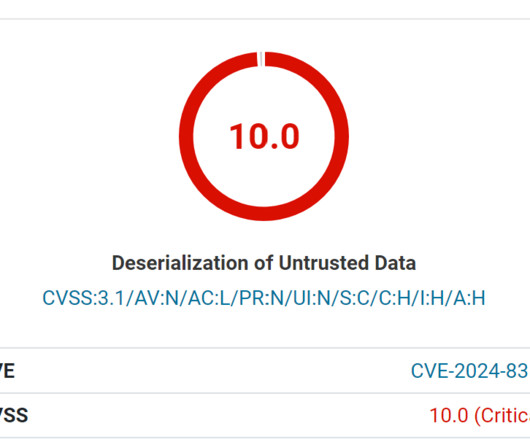
This vulnerability hacks a feature that allows ChatGPT to have long-term memory, where it uses information from past conversations to inform future conversations with that same user. A researcher found that he could use that feature to plant “false memories” into that context window that could subvert the model. A month later, the researcher submitted a new disclosure statement.















Let's personalize your content