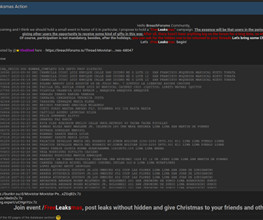
Operation Triangulation: The last (hardware) mystery
SecureList
DECEMBER 27, 2023
Today, on December 27, 2023, we ( Boris Larin , Leonid Bezvershenko , and Georgy Kucherin ) delivered a presentation, titled, “Operation Triangulation: What You Get When Attack iPhones of Researchers”, at the 37th Chaos Communication Congress (37C3), held at Congress Center Hamburg. The presentation summarized the results of our long-term research into Operation Triangulation, conducted with our colleagues, Igor Kuznetsov , Valentin Pashkov , and Mikhail Vinogradov.
































Let's personalize your content