Numbers Don't Lie: Exposing the Harsh Truths of Cyberattacks in New Report
The Hacker News
AUGUST 31, 2023
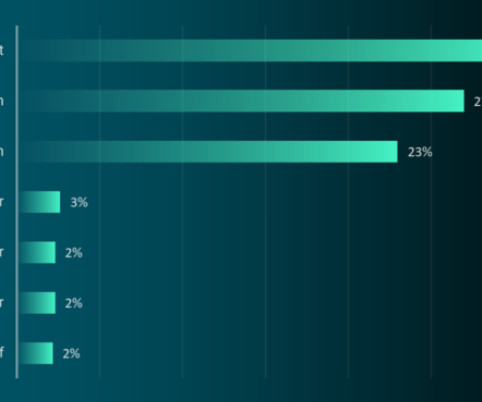
How often do cyberattacks happen? How frequently do threat actors target businesses and governments around the world? The BlackBerry® Threat Research and Intelligence Team recently analyzed 90 days of real-world data to answer these questions. Full results are in the latest BlackBerry Global Threat Intelligence Report, but read on for a teaser of several interesting cyber attack statistics.















Let's personalize your content