James Bamford on Section 702 Extension
Schneier on Security
JUNE 28, 2024
Longtime NSA-watcher James Bamford has a long article on the reauthorization of Section 702 of the Foreign Intelligence Surveillance Act (FISA).

Schneier on Security
JUNE 28, 2024
Longtime NSA-watcher James Bamford has a long article on the reauthorization of Section 702 of the Foreign Intelligence Surveillance Act (FISA).

Malwarebytes
JUNE 28, 2024
Chinese online shopping giant Temu is facing a lawsuit filed by State of Arkansas Attorney General Tim Griffin, alleging that the retailer’s mobile app spies on users. “Temu purports to be an online shopping platform, but it is dangerous malware, surreptitiously granting itself access to virtually all data on a user’s cellphone.” Temu quickly denied the allegations.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Boulevard
JUNE 28, 2024
Chinese fast-fashion-cum-junk retailer “is a data-theft business.” The post Temu is Malware — It Sells Your Info, Accuses Ark. AG appeared first on Security Boulevard.

Bleeping Computer
JUNE 28, 2024
RMM software developer TeamViewer says a Russian state-sponsored hacking group known as Midnight Blizzard is believed to be behind a breach of their corporate network this week. [.

Speaker: Speakers:
In today's digital age, having an untrained workforce can be a significant risk to your business. Cyber threats are evolving; without proper training, your employees could be the weakest link in your defense. This webinar empowers leaders like you with the tools and strategies needed to transform your employees into a robust frontline defense against cyber attacks.

Security Boulevard
JUNE 28, 2024
The rate of cyberattacks is rising as the threat level continues to evolve, according to BlackBerry Limited’s latest Global Threat Intelligence Report. The post Cyberattack Rate Surges as Novel Malware Growth Accelerates appeared first on Security Boulevard.

The Hacker News
JUNE 28, 2024
The North Korea-linked threat actor known as Kimsuky has been linked to the use of a new malicious Google Chrome extension that's designed to steal sensitive information as part of an ongoing intelligence collection effort.
Cyber Security Informer brings together the best content for cyber security professionals from the widest variety of industry thought leaders.
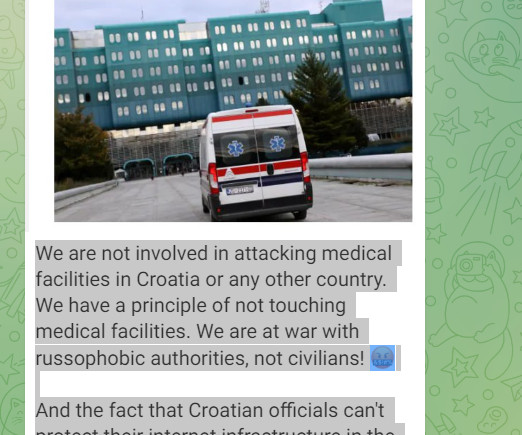
Security Affairs
JUNE 28, 2024
A cyber attack started targeting the University Hospital Centre Zagreb (KBC Zagreb) on Wednesday night, reported the Croatian Radiotelevision. A cyber attack began targeting the University Hospital Centre Zagreb (KBC Zagreb), the largest Croatian hospital, on Wednesday night, according to a report by Croatian Radiotelevision. The hospital has shut down its IT infrastructure in response to the cyber attack.

Security Boulevard
JUNE 28, 2024
Let’s examine why so many applications remain vulnerable despite high-severity warnings and how to minimize the threat to your organization. The post The Urgency to Uplevel AppSec: Securing Your Organization’s Vulnerable Building Blocks appeared first on Security Boulevard.

The Hacker News
JUNE 28, 2024
A group of security researchers from the Graz University of Technology have demonstrated a new side-channel attack known as SnailLoad that could be used to remotely infer a user's web activity. "SnailLoad exploits a bottleneck present on all Internet connections," the researchers said in a study released this week.

Bleeping Computer
JUNE 28, 2024
Ticketmaster has started to notify customers who were impacted by a data breach after hackers stole the company's Snowflake database, containing the data of millions of people. [.

Advertisement
How many people would you trust with your house keys? Chances are, you have a handful of trusted friends and family members who have an emergency copy, but you definitely wouldn’t hand those out too freely. You have stuff that’s worth protecting—and the more people that have access to your belongings, the higher the odds that something will go missing.

Security Boulevard
JUNE 28, 2024
For two decades or so now, web applications have been the backbone of many businesses, making their security paramount. Dynamic Application Security Testing (DAST) and penetration testing are crucial for identifying and mitigating security vulnerabilities in web application security. While both aim to enhance application security, they differ significantly in their approach, execution, and outcomes. … DAST Vs.

eSecurity Planet
JUNE 28, 2024
Millions of WordPress websites are under threat after a critical security breach involving several popular plugins. Security researchers discovered malicious code injected into these plugins, granting hackers the ability to create unauthorized administrator accounts. This compromise can lead to severe consequences for website owners, including data breaches and total website takeovers.

WIRED Threat Level
JUNE 28, 2024
WIRED was able to download stories from publishers like The New York Times and The Atlantic using Poe’s Assistant bot. One expert calls it “prima facie copyright infringement,” which Quora disputes.

Bleeping Computer
JUNE 28, 2024
The recent large scale supply chain attack conducted via multiple CDNs, namely Polyfill.io, BootCDN, Bootcss, and Staticfile that affected up to tens of millions of websites has been traced to a common operator. Researchers discovered a public GitHub repository with leaked API keys helping them draw a conclusion. [.

Advertiser: Revenera
In a recent study, IDC found that 64% of organizations said they were already using open source in software development with a further 25% planning to in the next year. Most organizations are unaware of just how much open-source code is used and underestimate their dependency on it. As enterprises grow the use of open-source software, they face a new challenge: understanding the scope of open-source software that's being used throughout the organization and the corresponding exposure.

The Hacker News
JUNE 28, 2024
GitLab has released security updates to address 14 security flaws, including one critical vulnerability that could be exploited to run continuous integration and continuous deployment (CI/CD) pipelines as any user. The weaknesses, which affect GitLab Community Edition (CE) and Enterprise Edition (EE), have been addressed in versions 17.1.1, 17.0.3, and 16.11.5.

Security Boulevard
JUNE 28, 2024
Crypto-Agility Required to Migrate to a New Certificate Authority (CA) Seamlessly and Highlights Need for Post-Quantum Cryptography (PQC) Readiness This week Google announced that the Google Chrome browser will no longer trust TLS certificates issued by the Entrust Certificate Authority (CA) starting November 1, 2024. Certificates issued by Entrust before October 31, 2024 will remain […] The post Attention: Google To Distrust Entrust TLS Certificates appeared first on Security Boulevard.

The Hacker News
JUNE 28, 2024
Security researchers have shed more light on the cryptocurrency mining operation conducted by the 8220 Gang by exploiting known security flaws in the Oracle WebLogic Server.

Security Boulevard
JUNE 28, 2024
Insight #1 Most ransomware deploys a remote-access Trojan (RAT), which allows for secondary infections to occur and enables access to victims’ networks to be sold in Darkweb forums. Insight #2 Most ransomware is delivered initially through the exploitation of a vulnerability. Runtime Security can mitigate this: It’s a highly effective exploit prevention for zero days , unknown vulnerabilities and a broad array of exploit techniques.

Advertisement
Within the past few years, ransomware attacks have turned to critical infrastructure, healthcare, and government entities. Attackers have taken advantage of the rapid shift to remote work and new technologies. Add to that hacktivism due to global conflicts and U.S. elections, and an increased focus on AI, and you have the perfect recipe for a knotty and turbulent 2024.

The Hacker News
JUNE 28, 2024
Multiple security flaws have been disclosed in Emerson Rosemount gas chromatographs that could be exploited by malicious actors to obtain sensitive information, induce a denial-of-service (DoS) condition, and even execute arbitrary commands. The flaws impact GC370XA, GC700XA, and GC1500XA and reside in versions 4.1.5 and prior.

Bleeping Computer
JUNE 28, 2024
Infosys McCamish Systems (IMS) disclosed that the LockBit ransomware attack it suffered earlier this year impacted sensitive information of more than six million individuals. [.

The Hacker News
JUNE 28, 2024
The modern kill chain is eluding enterprises because they aren’t protecting the infrastructure of modern business: SaaS. SaaS continues to dominate software adoption, and it accounts for the greatest share of public cloud spending. But enterprises and SMBs alike haven’t revised their security programs or adopted security tooling built for SaaS.

Digital Guardian
JUNE 28, 2024
Congress' sweeping privacy bill was stopped in its tracks, CISA's own tool was targeted in a January breach, concerns are arising over open-source code, & more. Read more about all these stories in this week's Friday Five.

Advertisement
The healthcare industry has massively adopted web tracking tools, including pixels and trackers. Tracking tools on user-authenticated and unauthenticated web pages can access personal health information (PHI) such as IP addresses, medical record numbers, home and email addresses, appointment dates, or other info provided by users on pages and thus can violate HIPAA Rules that govern the Use of Online Tracking Technologies by HIPAA Covered Entities and Business Associates.

Graham Cluley
JUNE 28, 2024
More of Microsoft's clients are being warned that emails they exchanged with the company were accessed by Russian hackers who broke into its systems and spied on staff inboxes. Read more in my article on the Hot for Security blog.

Digital Guardian
JUNE 28, 2024
Congress' sweeping privacy bill was stopped in its tracks, CISA's own tool was targeted in a January breach, concerns are arising over open-source code, & more. Read more about all these stories in this week's Friday Five.

Graham Cluley
JUNE 28, 2024
There's some possibly good news on the ransomware front. Companies are becoming more resilient to attacks, and the ransom payments extorted from businesses by hackers are on a downward trend. Read more in my article on the Tripwire State of Security blog.

Heimadal Security
JUNE 28, 2024
A new critical authentication bypass flaw in Progress MOVEit Transfer was disclosed, and threat actors are already trying their best to exploit it. The new security flaw, which goes by the number CVE-2024-5806, enables attackers to get around the Secure File Transfer Protocol (SFTP) module’s authentication procedure, which is in charge of handling file transfers […] The post New MOVEit Transfer Critical Vulnerability Targeted by Threat Actors appeared first on Heimdal Security Blog.

Advertisement
The losses companies suffered in 2023 ransomware attacks increased by 74% compared to those of the previous year, according to new data from the Federal Bureau of Investigation (FBI). The true figure is likely to be even higher, though, as many identity theft and phishing attacks go unreported. Ransomware attackers can potentially paralyze not just private sector organizations but also healthcare facilities, schools, and entire police departments.

Bleeping Computer
JUNE 28, 2024
Agropur, one of the largest dairy cooperatives in North America, is notifying customers of a data breach after some of its shared online directories were exposed. [.

Graham Cluley
JUNE 28, 2024
Car dealerships have been brought to a standstill across the United States after a software provider was hit by a ransomware attack. The attack, believed to be by the BlackSuit ransomware gang, forced CDK Global, makers of a platform widely used by car dealerships to conduct their everyday business, to down its IT systems and data centers. Read more in my article on the Exponential-e blog.
Heimadal Security
JUNE 28, 2024
We are excited to announce a special release, substantiating our key cross-platform product direction. New features and improvements are rolling out for Linux Ubuntu, macOS, and Windows. The updates are available in the Release Candidate and Production versions of the Heimdal dashboard (4.2.2 RC and 4.1.4 Production), and in the dedicated agent versions: Heimdal for […] The post Cross-Platform Product Release: Heimdal Integrates with HaloPSA appeared first on Heimdal Security Blog.

SecureBlitz
JUNE 28, 2024
Learn why small businesses should invest in managed IT. Running a small business is challenging enough without wrestling with tech issues. You're juggling countless tasks, from managing team members to keeping your customers happy. Amid all this, you can easily overlook your technological needs. But here's the thing: neglecting your Information Technology (IT) can cost […] The post Why Small Businesses Should Invest In Managed IT appeared first on SecureBlitz Cybersecurity.

Speaker: Blackberry, OSS Consultants, & Revenera
Software is complex, which makes threats to the software supply chain more real every day. 64% of organizations have been impacted by a software supply chain attack and 60% of data breaches are due to unpatched software vulnerabilities. In the U.S. alone, cyber losses totaled $10.3 billion in 2022. All of these stats beg the question, “Do you know what’s in your software?
Let's personalize your content