Ross Anderson’s Memorial Service
Schneier on Security
JUNE 21, 2024
The memorial service for Ross Anderson will be held on Saturday, at 2:00 PM BST. People can attend remotely on Zoom.

Schneier on Security
JUNE 21, 2024
The memorial service for Ross Anderson will be held on Saturday, at 2:00 PM BST. People can attend remotely on Zoom.

The Last Watchdog
JUNE 21, 2024
Dubai, UAE, June 20, 2024, CyberNewsWire — 1inch , a leading DeFi aggregator that provides advanced security solutions to users across the entire space, has announced today the launch of the 1inch Shield. This solution, that is offering enhanced protection against a wide range of potential threats, was completed in partnership with Blockaid , a major provider of Web3 security tools.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Tech Republic Security
JUNE 21, 2024
According to Gartner, there are gotchas that can impede an organization’s ability to embrace Copilot. Here’s what enterprises interested in implementing Copilot should keep in mind.

Malwarebytes
JUNE 21, 2024
The cybercriminal acting under the name “Sp1d3r” gave away the first 1 million records that are part of the data set that they claimed to have stolen from Ticketmaster/Live Nation. The files were released without a price, for free. When Malwarebytes Labs first learned about this data breach, it happened to be the first major event that was shared on the resurrected BreachForums , and someone acting under the handle “ShinyHunters” offered the full details (name, address, e

Speaker: Speakers:
In today's digital age, having an untrained workforce can be a significant risk to your business. Cyber threats are evolving; without proper training, your employees could be the weakest link in your defense. This webinar empowers leaders like you with the tools and strategies needed to transform your employees into a robust frontline defense against cyber attacks.

Tech Republic Security
JUNE 21, 2024
Immersing yourself in best practices for ethical hacking, pen-testing and information security can set you up for a career or better-protected business.

Security Boulevard
JUNE 21, 2024
Spend more on security! Car and truck dealers fall back on pen and paper as huge SaaS provider gets hacked (again). The post 30,000 Dealerships Down — ‘Ransomware’ Outage Outrage no. 2 at CDK Global appeared first on Security Boulevard.
Cyber Security Informer brings together the best content for cyber security professionals from the widest variety of industry thought leaders.

Penetration Testing
JUNE 21, 2024
A critical vulnerability in js2py, a widely-used Python library with over 1 million monthly downloads, has left countless web scrapers and applications exposed to remote code execution (RCE) attacks. The flaw, designated CVE-2024-28397 and... The post CVE-2024-28397: js2py Vulnerability Exposes Millions of Python Users to RCE appeared first on Cybersecurity News.

The Last Watchdog
JUNE 21, 2024
Cary, NC, June 20, 2024, CyberNewsWire — 2024 is rapidly shaping up to be a defining year in generative AI. While 2023 saw its emergence as a potent new technology, business leaders are now grappling with how to best leverage its transformative power to grow efficiency, security, and revenue. With the near-universal integration of AI into global technology, the need for AI-ready cybersecurity teams is more critical than ever.

WIRED Threat Level
JUNE 21, 2024
Experts aren't unanimous about whether the AI-powered search startup's practices could expose it to legal claims ranging from infringement to defamation—but some say plaintiffs would have strong cases.

Security Affairs
JUNE 21, 2024
French information security agency ANSSI reported that Russia-linked threat actor Nobelium is behind a series of cyber attacks that targeted French diplomatic entities. The French information security agency ANSSI reported that Russia-linked APT Nobelium targeted French diplomatic entities. Despite the French agency linked the attacks to the cyberespionage group Nobelium (aka APT29 , SVR group , Cozy Bear , Midnight Blizzard , BlueBravo , and The Dukes ), ANSSI differentiates these groups i

Advertisement
How many people would you trust with your house keys? Chances are, you have a handful of trusted friends and family members who have an emergency copy, but you definitely wouldn’t hand those out too freely. You have stuff that’s worth protecting—and the more people that have access to your belongings, the higher the odds that something will go missing.
The Hacker News
JUNE 21, 2024
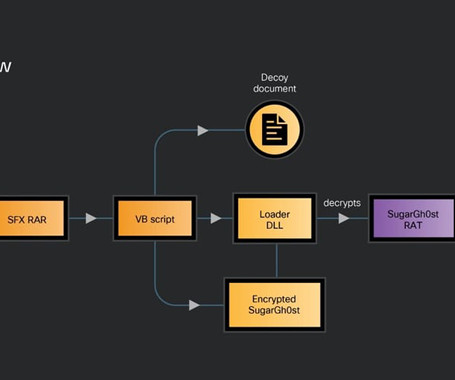
A previously undocumented Chinese-speaking threat actor codenamed SneakyChef has been linked to an espionage campaign primarily targeting government entities across Asia and EMEA (Europe, Middle East, and Africa) with SugarGh0st malware since at least August 2023.

Security Boulevard
JUNE 21, 2024
Long simmering suspicions about the loyalty of Kaspersky Software, a cybersecurity firm headquartered in Russia, came to a head this week after the U.S. government banned the sale of the company’s software, effective July 20th, to both companies and individual consumers. In addition, the U.S. Treasury Department has placed sanctions on 12 senior leaders of.

The Hacker News
JUNE 21, 2024
The U.S. Department of the Treasury's Office of Foreign Assets Control (OFAC) imposed sanctions against a dozen individuals serving executive and senior leadership roles at Kaspersky Lab, a day after the Russian company was banned by the Commerce Department.

Bleeping Computer
JUNE 21, 2024
The Los Angeles Unified School District has confirmed a data breach after threat actors stole student and employee data by breaching the company's Snowflake account. [.

Advertiser: Revenera
In a recent study, IDC found that 64% of organizations said they were already using open source in software development with a further 25% planning to in the next year. Most organizations are unaware of just how much open-source code is used and underestimate their dependency on it. As enterprises grow the use of open-source software, they face a new challenge: understanding the scope of open-source software that's being used throughout the organization and the corresponding exposure.
The Hacker News
JUNE 21, 2024
A malvertising campaign is leveraging trojanized installers for popular software such as Google Chrome and Microsoft Teams to drop a backdoor called Oyster (aka Broomstick and CleanUpLoader). That's according to findings from Rapid7, which identified lookalike websites hosting the malicious payloads that users are redirected to after searching for them on search engines like Google and Bing.

Bleeping Computer
JUNE 21, 2024
CDK Global has cautioned customers about unscrupulous actors calling them and posing as CDK agents or affiliates to gain unauthorized systems access. The warning follows ongoing cyberattacks that have hit CDK, a software-as-a-service (SaaS) platform that thousands of US car dealerships rely upon. [.

The Hacker News
JUNE 21, 2024
A recently patched high-severity flaw impacting SolarWinds Serv-U file transfer software is being actively exploited by malicious actors in the wild. The vulnerability, tracked as CVE-2024-28995 (CVSS score: 8.6), concerns a directory transversal bug that could allow attackers to read sensitive files on the host machine. Affecting all versions of the software prior to and including Serv-U 15.4.
Security Affairs
JUNE 21, 2024
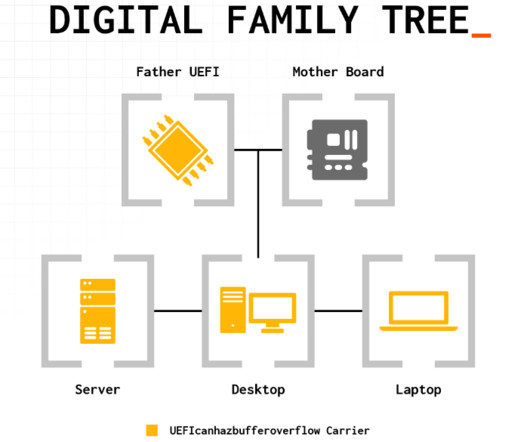
A serious vulnerability (CVE-2024-0762) in the Phoenix SecureCore UEFI firmware potentially impacts hundreds of PC and server models. Firmware security firm Eclypsium discovered a vulnerability, tracked as CVE-2024-0762 (CVSS of 7.5), in the Phoenix SecureCore UEFI firmware. The issue, called UEFIcanhazbufferoverflow , potentially impacts hundreds of PC and server models that use Intel Core desktop and mobile processors.

Advertisement
Within the past few years, ransomware attacks have turned to critical infrastructure, healthcare, and government entities. Attackers have taken advantage of the rapid shift to remote work and new technologies. Add to that hacktivism due to global conflicts and U.S. elections, and an increased focus on AI, and you have the perfect recipe for a knotty and turbulent 2024.

The Hacker News
JUNE 21, 2024
Cybersecurity researchers have shed light on a new phishing campaign that has been identified as targeting people in Pakistan using a custom backdoor. Dubbed PHANTOM#SPIKE by Securonix, the unknown threat actors behind the activity have leveraged military-related phishing documents to activate the infection sequence.

Bleeping Computer
JUNE 21, 2024
The Treasury Department's Office of Foreign Assets Control (OFAC) has sanctioned twelve Kaspersky Lab executives for operating in the technology sector of Russia. [.

Heimadal Security
JUNE 21, 2024
Massive hack forces CDK Global, a provider of software-as-a-service for car dealerships, to shut down its servers, leaving customers unable to run their businesses as usual. A SaaS platform from CDK Global serves clients in the auto sector, managing all facets of vehicle dealership operations, such as inventory management, CRM, financing, payroll, support, and servicing. […] The post CDK Group Falls Victim to Two Cyberattacks appeared first on Heimdal Security Blog.

Bleeping Computer
JUNE 21, 2024
UnitedHealth has confirmed for the first time what types of medical and patient data were stolen in the massive Change Healthcare ransomware attack, stating that data breach notifications will be mailed in July. [.

Advertisement
The healthcare industry has massively adopted web tracking tools, including pixels and trackers. Tracking tools on user-authenticated and unauthenticated web pages can access personal health information (PHI) such as IP addresses, medical record numbers, home and email addresses, appointment dates, or other info provided by users on pages and thus can violate HIPAA Rules that govern the Use of Online Tracking Technologies by HIPAA Covered Entities and Business Associates.

Security Boulevard
JUNE 21, 2024
Modern chief information security officers (CISOs) are navigating tough circumstances due to complex challenges and heightened regulatory pressures. The post It’s a Hard Time to Be a CISO. Transformational Leadership is More Important Than Ever. appeared first on Security Boulevard.

Bleeping Computer
JUNE 21, 2024
The Tor Project has released Tor Browser 13.5, bringing several improvements and enhancements for Android and desktop versions. [.

Security Boulevard
JUNE 21, 2024
The post The dos and don’ts of gamified cyber security training appeared first on Click Armor. The post The dos and don’ts of gamified cyber security training appeared first on Security Boulevard.

Bleeping Computer
JUNE 21, 2024
A federal jury in Las Vegas convicted five men for their involvement in the operation of Jetflicks, one of the largest and most popular illegal streaming services in the United States. [.

Advertisement
The losses companies suffered in 2023 ransomware attacks increased by 74% compared to those of the previous year, according to new data from the Federal Bureau of Investigation (FBI). The true figure is likely to be even higher, though, as many identity theft and phishing attacks go unreported. Ransomware attackers can potentially paralyze not just private sector organizations but also healthcare facilities, schools, and entire police departments.
Penetration Testing
JUNE 21, 2024
Over 30,000 WooCommerce-powered online stores may be at risk of a serious data breach due to a critical security flaw in the popular “Themify – WooCommerce Product Filter” plugin. The vulnerability, tracked as CVE-2024-6027... The post Over 30,000 WooCommerce Sites Exposed by Critical Plugin Flaw (CVE-2024-6027) appeared first on Cybersecurity News.

Zero Day
JUNE 21, 2024
With the sudden arrival of ChatGPT, educators and editors face a worrying surge of automated content submissions. We look at the problem and what can be done about it.

Security Boulevard
JUNE 21, 2024
With insider incidents on the rise, security leaders are taking a proactive approach to help blunt the negative impacts For most organizations, people are their greatest asset. However, employees with access to information, technology, and facilities can also be your company’s greatest vulnerability — intentionally and unintentionally. In light of recent mass layoffs and the… The post Creating an Effective Insider Risk Program appeared first on Ontic.

Lenny Zeltser
JUNE 21, 2024
Organizing events that gather cybersecurity leaders requires significant effort and sponsorships. Unfortunately, some events and communities exclude CISOs who work for security vendors. This stance, though well-meaning, harms the industry and allows hidden conflicts of interest to go unchecked. Here's why and how we can address this issue to improve such events and the community at large.

Speaker: Blackberry, OSS Consultants, & Revenera
Software is complex, which makes threats to the software supply chain more real every day. 64% of organizations have been impacted by a software supply chain attack and 60% of data breaches are due to unpatched software vulnerabilities. In the U.S. alone, cyber losses totaled $10.3 billion in 2022. All of these stats beg the question, “Do you know what’s in your software?
Let's personalize your content