Ross Anderson’s Memorial Service
Schneier on Security
JUNE 21, 2024
The memorial service for Ross Anderson will be held on Saturday, at 2:00 PM BST. People can attend remotely on Zoom.

Schneier on Security
JUNE 21, 2024
The memorial service for Ross Anderson will be held on Saturday, at 2:00 PM BST. People can attend remotely on Zoom.

Tech Republic Security
JUNE 21, 2024
Immersing yourself in best practices for ethical hacking, pen-testing and information security can set you up for a career or better-protected business.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Last Watchdog
JUNE 21, 2024
Dubai, UAE, June 20, 2024, CyberNewsWire — 1inch , a leading DeFi aggregator that provides advanced security solutions to users across the entire space, has announced today the launch of the 1inch Shield. This solution, that is offering enhanced protection against a wide range of potential threats, was completed in partnership with Blockaid , a major provider of Web3 security tools.

Tech Republic Security
JUNE 21, 2024
In this TechRepublic exclusive, Gartner VP Analyst Dionisio Zumerle shares three leadership strategies for achieving cybersecurity platform consolidation.

Speaker: Erroll Amacker
Automation is transforming finance but without strong financial oversight it can introduce more risk than reward. From missed discrepancies to strained vendor relationships, accounts payable automation needs a human touch to deliver lasting value. This session is your playbook to get automation right. We’ll explore how to balance speed with control, boost decision-making through human-machine collaboration, and unlock ROI with fewer errors, stronger fraud prevention, and smoother operations.

Malwarebytes
JUNE 21, 2024
The cybercriminal acting under the name “Sp1d3r” gave away the first 1 million records that are part of the data set that they claimed to have stolen from Ticketmaster/Live Nation. The files were released without a price, for free. When Malwarebytes Labs first learned about this data breach, it happened to be the first major event that was shared on the resurrected BreachForums , and someone acting under the handle “ShinyHunters” offered the full details (name, address, e

Tech Republic Security
JUNE 21, 2024
According to Gartner, there are gotchas that can impede an organization’s ability to embrace Copilot. Here’s what enterprises interested in implementing Copilot should keep in mind.
Cyber Security Informer brings together the best content for cyber security professionals from the widest variety of industry thought leaders.
Security Affairs
JUNE 21, 2024
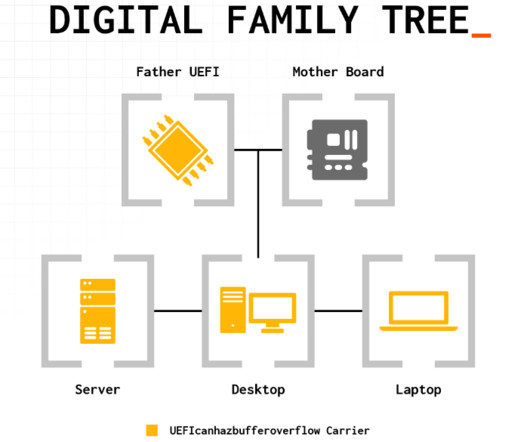
A serious vulnerability (CVE-2024-0762) in the Phoenix SecureCore UEFI firmware potentially impacts hundreds of PC and server models. Firmware security firm Eclypsium discovered a vulnerability, tracked as CVE-2024-0762 (CVSS of 7.5), in the Phoenix SecureCore UEFI firmware. The issue, called UEFIcanhazbufferoverflow , potentially impacts hundreds of PC and server models that use Intel Core desktop and mobile processors.
The Hacker News
JUNE 21, 2024
A malvertising campaign is leveraging trojanized installers for popular software such as Google Chrome and Microsoft Teams to drop a backdoor called Oyster (aka Broomstick and CleanUpLoader). That's according to findings from Rapid7, which identified lookalike websites hosting the malicious payloads that users are redirected to after searching for them on search engines like Google and Bing.

Security Affairs
JUNE 21, 2024
French information security agency ANSSI reported that Russia-linked threat actor Nobelium is behind a series of cyber attacks that targeted French diplomatic entities. The French information security agency ANSSI reported that Russia-linked APT Nobelium targeted French diplomatic entities. Despite the French agency linked the attacks to the cyberespionage group Nobelium (aka APT29 , SVR group , Cozy Bear , Midnight Blizzard , BlueBravo , and The Dukes ), ANSSI differentiates these groups i

The Hacker News
JUNE 21, 2024
A recently patched high-severity flaw impacting SolarWinds Serv-U file transfer software is being actively exploited by malicious actors in the wild. The vulnerability, tracked as CVE-2024-28995 (CVSS score: 8.6), concerns a directory transversal bug that could allow attackers to read sensitive files on the host machine. Affecting all versions of the software prior to and including Serv-U 15.4.

Advertisement
Many cybersecurity awareness platforms offer massive content libraries, yet they fail to enhance employees’ cyber resilience. Without structured, engaging, and personalized training, employees struggle to retain and apply key cybersecurity principles. Phished.io explains why organizations should focus on interactive, scenario-based learning rather than overwhelming employees with excessive content.

Security Boulevard
JUNE 21, 2024
Spend more on security! Car and truck dealers fall back on pen and paper as huge SaaS provider gets hacked (again). The post 30,000 Dealerships Down — ‘Ransomware’ Outage Outrage no. 2 at CDK Global appeared first on Security Boulevard.

The Hacker News
JUNE 21, 2024
The U.S. Department of the Treasury's Office of Foreign Assets Control (OFAC) imposed sanctions against a dozen individuals serving executive and senior leadership roles at Kaspersky Lab, a day after the Russian company was banned by the Commerce Department.

Penetration Testing
JUNE 21, 2024
A critical vulnerability in js2py, a widely-used Python library with over 1 million monthly downloads, has left countless web scrapers and applications exposed to remote code execution (RCE) attacks. The flaw, designated CVE-2024-28397 and... The post CVE-2024-28397: js2py Vulnerability Exposes Millions of Python Users to RCE appeared first on Cybersecurity News.

The Hacker News
JUNE 21, 2024
Cybersecurity researchers have shed light on a new phishing campaign that has been identified as targeting people in Pakistan using a custom backdoor. Dubbed PHANTOM#SPIKE by Securonix, the unknown threat actors behind the activity have leveraged military-related phishing documents to activate the infection sequence.

Advertisement
The DHS compliance audit clock is ticking on Zero Trust. Government agencies can no longer ignore or delay their Zero Trust initiatives. During this virtual panel discussion—featuring Kelly Fuller Gordon, Founder and CEO of RisX, Chris Wild, Zero Trust subject matter expert at Zermount, Inc., and Principal of Cybersecurity Practice at Eliassen Group, Trey Gannon—you’ll gain a detailed understanding of the Federal Zero Trust mandate, its requirements, milestones, and deadlines.

Malwarebytes
JUNE 21, 2024
A moderator of the notorious data breach trading platform BreachForums is offering data for sale they claim comes from a data breach at T-Mobile. The moderator, going by the name of IntelBroker, describes the data as containing source code, SQL files, images, Terraform data, t-mobile.com certifications, and “Siloprograms.” (We’ve not heard of siloprograms, and can’t find a reference to them anywhere, so perhaps it’s a mistranslation or typo.

WIRED Threat Level
JUNE 21, 2024
Experts aren't unanimous about whether the AI-powered search startup's practices could expose it to legal claims ranging from infringement to defamation—but some say plaintiffs would have strong cases.

Security Boulevard
JUNE 21, 2024
Long simmering suspicions about the loyalty of Kaspersky Software, a cybersecurity firm headquartered in Russia, came to a head this week after the U.S. government banned the sale of the company’s software, effective July 20th, to both companies and individual consumers. In addition, the U.S. Treasury Department has placed sanctions on 12 senior leaders of.

Bleeping Computer
JUNE 21, 2024
The Tor Project has released Tor Browser 13.5, bringing several improvements and enhancements for Android and desktop versions. [.

Speaker: Sierre Lindgren
Fraud is a battle that every organization must face – it’s no longer a question of “if” but “when.” Every organization is a potential target for fraud, and the finance department is often the bullseye. From cleverly disguised emails to fraudulent payment requests, the tactics of cybercriminals are advancing rapidly. Drawing insights from real-world cases and industry expertise, we’ll explore the vulnerabilities in your processes and how to fortify them effectively.

eSecurity Planet
JUNE 21, 2024
Keeper and Dashlane are top password managers prioritizing multi-layered encryption systems for secure password sharing. Keeper emphasizes extensive security measures and is a more affordable option, while Dashlane promotes a user-friendly interface and robust administrative tools perfect for streamlining logins. To assist you in making your decision, I’ve compared the two solutions, focusing on their distinctive features, use cases, benefits, pros, and cons.

Bleeping Computer
JUNE 21, 2024
The Los Angeles Unified School District has confirmed a data breach after threat actors stole student and employee data by breaching the company's Snowflake account. [.

The Last Watchdog
JUNE 21, 2024
Cary, NC, June 20, 2024, CyberNewsWire — 2024 is rapidly shaping up to be a defining year in generative AI. While 2023 saw its emergence as a potent new technology, business leaders are now grappling with how to best leverage its transformative power to grow efficiency, security, and revenue. With the near-universal integration of AI into global technology, the need for AI-ready cybersecurity teams is more critical than ever.

Bleeping Computer
JUNE 21, 2024
CDK Global has cautioned customers about unscrupulous actors calling them and posing as CDK agents or affiliates to gain unauthorized systems access. The warning follows ongoing cyberattacks that have hit CDK, a software-as-a-service (SaaS) platform that thousands of US car dealerships rely upon. [.

Advertisement
Keeper Security is transforming cybersecurity for people and organizations around the world. Keeper’s affordable and easy-to-use solutions are built on a foundation of zero-trust and zero-knowledge security to protect every user on every device. Our next-generation privileged access management solution deploys in minutes and seamlessly integrates with any tech stack to prevent breaches, reduce help desk costs and ensure compliance.

Security Boulevard
JUNE 21, 2024
Modern chief information security officers (CISOs) are navigating tough circumstances due to complex challenges and heightened regulatory pressures. The post It’s a Hard Time to Be a CISO. Transformational Leadership is More Important Than Ever. appeared first on Security Boulevard.

Heimadal Security
JUNE 21, 2024
Massive hack forces CDK Global, a provider of software-as-a-service for car dealerships, to shut down its servers, leaving customers unable to run their businesses as usual. A SaaS platform from CDK Global serves clients in the auto sector, managing all facets of vehicle dealership operations, such as inventory management, CRM, financing, payroll, support, and servicing. […] The post CDK Group Falls Victim to Two Cyberattacks appeared first on Heimdal Security Blog.

Bleeping Computer
JUNE 21, 2024
The Treasury Department's Office of Foreign Assets Control (OFAC) has sanctioned twelve Kaspersky Lab executives for operating in the technology sector of Russia. [.

Cisco Security
JUNE 21, 2024
This playbook will serve as a great resource for coordinating AI security incidents among industry peers and global partners, ensuring a resilient and secure technological future This playbook will serve as a great resource for coordinating AI security incidents among industry peers and global partners, ensuring a resilient and secure technological future

Advertisement
Many software teams have migrated their testing and production workloads to the cloud, yet development environments often remain tied to outdated local setups, limiting efficiency and growth. This is where Coder comes in. In our 101 Coder webinar, you’ll explore how cloud-based development environments can unlock new levels of productivity. Discover how to transition from local setups to a secure, cloud-powered ecosystem with ease.

Bleeping Computer
JUNE 21, 2024
UnitedHealth has confirmed for the first time what types of medical and patient data were stolen in the massive Change Healthcare ransomware attack, stating that data breach notifications will be mailed in July. [.

Security Boulevard
JUNE 21, 2024
The post The dos and don’ts of gamified cyber security training appeared first on Click Armor. The post The dos and don’ts of gamified cyber security training appeared first on Security Boulevard.

Bleeping Computer
JUNE 21, 2024
A federal jury in Las Vegas convicted five men for their involvement in the operation of Jetflicks, one of the largest and most popular illegal streaming services in the United States. [.

Cisco Security
JUNE 21, 2024
Organizations face a critical challenge today: attackers are exploiting the weakest links in their networks, such as unsecured users, devices, and workloads. This threat landscape is complicated by the shift from traditional data centers to a distributed environment, where protecting dispersed data across multiple touchpoints becomes complex. To address these threats, many organizations resort to […] Organizations face a critical challenge today: attackers are exploiting the weakest links

Advertisement
After a year of sporadic hiring and uncertain investment areas, tech leaders are scrambling to figure out what’s next. This whitepaper reveals how tech leaders are hiring and investing for the future. Download today to learn more!
Let's personalize your content