Black Hat Fireside Chat: User feedback, AI-infused email security are both required to deter phishing
The Last Watchdog
AUGUST 21, 2024
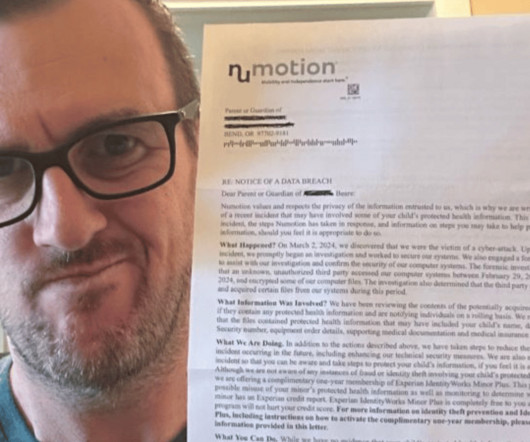
I recently learned all about the state-of-the art of phishing attacks – the hard way. Related: GenAI-powered attacks change the game An email arrived from the head of a PR firm whom I’ve known for 20 years asking me to click on a link to check out a proposal. Foolishly, I did so all too quickly. Within a few minutes, many of my contacts, and even strangers, were receiving a similar malicious email from me.







































Let's personalize your content