Breaking the M-209
Schneier on Security
JUNE 25, 2024
Interesting paper about a German cryptanalysis machine that helped break the US M-209 mechanical ciphering machine. The paper contains a good description of how the M-209 works.

Schneier on Security
JUNE 25, 2024
Interesting paper about a German cryptanalysis machine that helped break the US M-209 mechanical ciphering machine. The paper contains a good description of how the M-209 works.
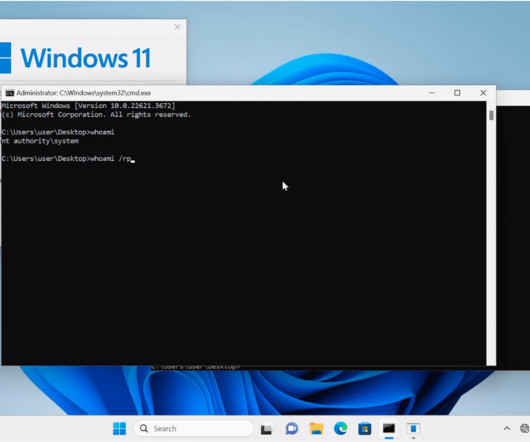
Penetration Testing
JUNE 25, 2024
A security researcher has published a proof-of-concept (PoC) exploit code targeting a recent high-severity vulnerability (CVE-2024-30088) in Microsoft Windows. This critical flaw holds a risk severity score of 7.0 and impacts systems across the... The post PoC Exploit Published for Windows Kernel Elevation of Privilege Vulnerability (CVE-2024-30088) appeared first on Cybersecurity News.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Boulevard
JUNE 25, 2024
Copying users’ files and deleting some? Even a cartoon hound knows this isn’t fine. The post Microsoft Privacy FAIL: Windows 11 Silently Backs Up to OneDrive appeared first on Security Boulevard.
The Hacker News
JUNE 25, 2024
Google has taken steps to block ads for e-commerce sites that use the Polyfill.io service after a Chinese company acquired the domain and modified the JavaScript library ("polyfill.js") to redirect users to malicious and scam sites. More than 110,000 sites that embed the library are impacted by the supply chain attack, Sansec said in a Tuesday report.

Speaker: Speakers:
In today's digital age, having an untrained workforce can be a significant risk to your business. Cyber threats are evolving; without proper training, your employees could be the weakest link in your defense. This webinar empowers leaders like you with the tools and strategies needed to transform your employees into a robust frontline defense against cyber attacks.

Bleeping Computer
JUNE 25, 2024
The Medusa banking trojan for Android has re-emerged after almost a year of keeping a lower profile in campaigns targeting France, Italy, the United States, Canada, Spain, the United Kingdom, and Turkey. [.

Security Boulevard
JUNE 25, 2024
Red Teaming security assessments aim to demonstrate to clients how attackers in the real world might link together various exploits and attack methods to reach their objectives. The post Stepping Into the Attacker’s Shoes: The Strategic Power of Red Teaming (Insights from the Field) appeared first on Security Boulevard.
Cyber Security Informer brings together the best content for cyber security professionals from the widest variety of industry thought leaders.

Jane Frankland
JUNE 25, 2024
Gordon Moore, a co-founder of Intel, the “father of Silicon Valley,” and well known for “Moore’s Law” once famously said, “Whatever has been done can be outdone.” Tech leaders understand this. They know that becoming agile, strategic, and resilient is not just a goal but a necessity. To compete and win in challenging times such as these, means investing in tech wisely, reducing CapEx and OpEx spend, attracting and retaining top talent, innovating continu
The Hacker News
JUNE 25, 2024
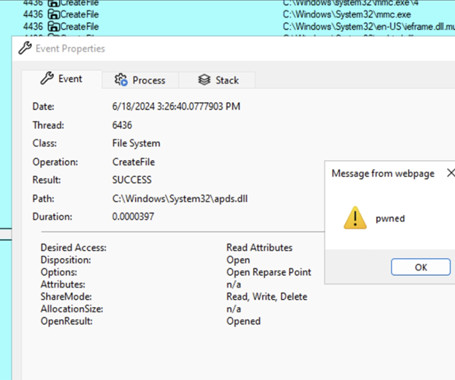
Threat actors are exploiting a novel attack technique in the wild that leverages specially crafted management saved console (MSC) files to gain full code execution using Microsoft Management Console (MMC) and evade security defenses. Elastic Security Labs has codenamed the approach GrimResource after identifying an artifact ("sccm-updater.

Bleeping Computer
JUNE 25, 2024
P2PInfect, originally a dormant peer-to-peer malware botnet with unclear motives, has finally come alive to deploy a ransomware module and a cryptominer in attacks on Redis servers. [.

Security Boulevard
JUNE 25, 2024
The LockBit ransomware group is claiming that it hacked into systems at the U.S. Federal Reserve and stole 33TB of data that it will begin leaking as early as Tuesday if the institution doesn’t pay the unspecified ransom. The notorious cybercriminals announced the attack on its dark web leak site on June 23, giving the. The post LockBit Claims Ransomware Attack on U.S.

Advertisement
How many people would you trust with your house keys? Chances are, you have a handful of trusted friends and family members who have an emergency copy, but you definitely wouldn’t hand those out too freely. You have stuff that’s worth protecting—and the more people that have access to your belongings, the higher the odds that something will go missing.

Bleeping Computer
JUNE 25, 2024
A threat actor modified the source code of at least five plugins hosted on WordPress.org to include malicious PHP scripts that create new accounts with administrative privileges on websites running them. [.

Security Boulevard
JUNE 25, 2024
By introducing a mobile device management (MDM) platform into the existing infrastructure, administrators gain the ability to restrict sideloading on managed devices. The post EU Opens the App Store Gates: A Call to Arms for MDM Implementation appeared first on Security Boulevard.

Bleeping Computer
JUNE 25, 2024
The FBI is warning of cybercriminals posing as law firms and lawyers that offer cryptocurrency recovery services to victims of investment scams and steal funds and personal information. [.

Security Boulevard
JUNE 25, 2024
Let’s explore some of the details behind this escalating threat to SaaS applications, what may be driving it, and what you can do to better protect your SaaS footprint from these types of threats. The post Why SaaS Identity Abuse is This Year’s Ransomware appeared first on RevealSecurity. The post Why SaaS Identity Abuse is This Year’s Ransomware appeared first on Security Boulevard.

Advertiser: Revenera
In a recent study, IDC found that 64% of organizations said they were already using open source in software development with a further 25% planning to in the next year. Most organizations are unaware of just how much open-source code is used and underestimate their dependency on it. As enterprises grow the use of open-source software, they face a new challenge: understanding the scope of open-source software that's being used throughout the organization and the corresponding exposure.

eSecurity Planet
JUNE 25, 2024
Kaspersky Lab is a widely known name in the world of cybersecurity. Founded in 1997, the Russian firm has grown into a global leader, boasting millions of users for its antivirus software and other security solutions. With a presence in over 200 countries and territories, Kaspersky Lab protects individuals, businesses, and critical infrastructure from a wide range of cyber threats.

Security Boulevard
JUNE 25, 2024
Effective April 30, 2024 Airbnb, the global vacation rental giant, announced a significant policy change: the prohibition of all indoor security cameras in its listings worldwide. This decision, aims to bolster the privacy of guests and address longstanding concerns about hidden cameras. While the majority of Airbnb’s over 7 million listings did not report having […] The post Airbnb’s Ban on Indoor Security Cameras: What It Means for Your Personal Cybersecurity appeared first on BlackCloak |

Security Affairs
JUNE 25, 2024
Researchers warn that a Mirai-based botnet is exploiting a recently disclosed critical vulnerability in EoL Zyxel NAS devices. Researchers at the Shadowserver Foundation warn that a Mirai -based botnet has started exploiting a recently disclosed vulnerability tracked as CVE-2024-29973 (CVSS score 9.8) in end-of-life NAS devices Zyxel NAS products. The flaw is a command injection vulnerability in the “setCookie” parameter in Zyxel NAS326 firmware versions before V5.21(AAZF.17)C0 and NAS542 firmwa

Security Boulevard
JUNE 25, 2024
Security analysts at Google are developing a framework that they hope will enable large language models (LLMs) to eventually be able to run automated vulnerability research, particularly analyses of malware variants. The analysts with Google’s Project Zero – a group founded a decade ago whose job it is to find zero-day vulnerabilities – have been. The post Google’s Project Naptime Aims for AI-Based Vulnerability Research appeared first on Security Boulevard.

Advertisement
Within the past few years, ransomware attacks have turned to critical infrastructure, healthcare, and government entities. Attackers have taken advantage of the rapid shift to remote work and new technologies. Add to that hacktivism due to global conflicts and U.S. elections, and an increased focus on AI, and you have the perfect recipe for a knotty and turbulent 2024.

Security Affairs
JUNE 25, 2024
WikiLeaks founder Julian Assange has been released in the U.K. and has left the country after five years in Belmarsh prison. Julian Assange is free after five years in Belmarsh prison, the WikiLeaks founder has been released in the U.K. and is flying to the island of Saipan in the Northern Mariana Islands, to make a brief court appearance before flying to Australia where he will be a free man in Australia.

WIRED Threat Level
JUNE 25, 2024
How accurate are gunshot detection systems, really? For years, it's been a secret, but new reports from San Jose and NYC show these systems have operated well below their advertised accuracy rates.

The Hacker News
JUNE 25, 2024
A previously undocumented threat actor dubbed Boolka has been observed compromising websites with malicious scripts to deliver a modular trojan codenamed BMANAGER.

Tech Republic Security
JUNE 25, 2024
Email-based cyberattacks are rampant. If we go by figures, the U.S. Cybersecurity and Infrastructure Security Agency reports that 90% of successful cyberattacks begin with phishing emails. While phishing emails can target individuals and businesses of all sizes, attackers may prefer to double down their aim at senior-level employees to increase their chances of catching a.

Advertisement
The healthcare industry has massively adopted web tracking tools, including pixels and trackers. Tracking tools on user-authenticated and unauthenticated web pages can access personal health information (PHI) such as IP addresses, medical record numbers, home and email addresses, appointment dates, or other info provided by users on pages and thus can violate HIPAA Rules that govern the Use of Online Tracking Technologies by HIPAA Covered Entities and Business Associates.

WIRED Threat Level
JUNE 25, 2024
WikiLeaks founder Julian Assange has agreed to plead guilty to one count of espionage in US court on Wednesday, ending a years-long legal battle between the US government and a controversial publisher.

Tech Republic Security
JUNE 25, 2024
Nearly half of Americans, 46%, have had a password stolen in the past year. Out of all the accounts that were breached, more than three-quarters (77%) of those users had their personal information stolen, such as their personal address, credit card number and Social Security Number. Password attacks on businesses can expose even more critical.

Heimadal Security
JUNE 25, 2024
If you’re in the market for an endpoint detection and response (XDR) product, there are plenty of options available. But within the word salad of overlapping terms (XDR, EDR, ASM, and more), it can be a real challenge to actually understand what features you need and where they’re available. This means choosing the right XDR […] The post Sophos vs.

Malwarebytes
JUNE 25, 2024
Luxury retail chain Neiman Marcus has begun to inform customers about a cyberattack it discovered in May. The attacker compromised a database platform storing customers’ personal information. The letter tells customers: “Promptly after learning of the issue, we took steps to contain it, including by disabling access to the relevant database platform.

Advertisement
The losses companies suffered in 2023 ransomware attacks increased by 74% compared to those of the previous year, according to new data from the Federal Bureau of Investigation (FBI). The true figure is likely to be even higher, though, as many identity theft and phishing attacks go unreported. Ransomware attackers can potentially paralyze not just private sector organizations but also healthcare facilities, schools, and entire police departments.
Bleeping Computer
JUNE 25, 2024
Luxury retailer Neiman Marcus confirmed it suffered a data breach after hackers attempted to sell the company's database stolen in recent Snowflake data theft attacks. [.

The Hacker News
JUNE 25, 2024
Browser security is becoming increasingly popular, as organizations understand the need to protect at the point of risk - the browser. Network and endpoint solutions are limited in their ability to protect from web-borne threats like phishing websites or malicious browser extensions. They also do not protect from internal data exfiltration, like employees pasting sensitive data to ChatGPT.
SecureList
JUNE 25, 2024
Small and medium-sized businesses (SMBs) are increasingly targeted by cybercriminals. Despite adopting digital technology for remote work, production, and sales, SMBs often lack robust cybersecurity measures. SMBs face significant cybersecurity challenges due to limited resources and expertise. The cost of data breaches can cripple operations, making preventive measures essential.
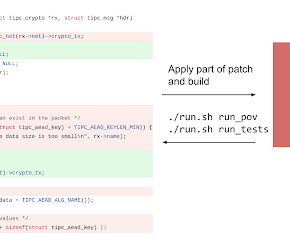
Google Security
JUNE 25, 2024
Oliver Chang, Jonathan Metzman, OSS-Fuzz and Alex Rebert, Security Engineering The US Defense Advanced Research Projects Agency, DARPA , recently kicked off a two-year AI Cyber Challenge (AIxCC) , inviting top AI and cybersecurity experts to design new AI systems to help secure major open source projects which our critical infrastructure relies upon.

Speaker: Blackberry, OSS Consultants, & Revenera
Software is complex, which makes threats to the software supply chain more real every day. 64% of organizations have been impacted by a software supply chain attack and 60% of data breaches are due to unpatched software vulnerabilities. In the U.S. alone, cyber losses totaled $10.3 billion in 2022. All of these stats beg the question, “Do you know what’s in your software?
Let's personalize your content