Zscaler Report: Mobile, IoT, and OT Cyber Threats Surge in 2024
Tech Republic Security
OCTOBER 16, 2024
Zscaler ThreatLabz report reveals a 2024 surge in mobile, IoT, and OT cyberattacks, highlighting key trends and the need for zero trust security.

Tech Republic Security
OCTOBER 16, 2024
Zscaler ThreatLabz report reveals a 2024 surge in mobile, IoT, and OT cyberattacks, highlighting key trends and the need for zero trust security.

Malwarebytes
OCTOBER 16, 2024
Millions of people are turning normal pictures into nude images, and it can be done in minutes. Journalists at Wired found at least 50 “nudify” bots on Telegram that claim to create explicit photos or videos of people with only a couple of clicks. Combined, these bots have millions of monthly users. Although there is no sure way to find out how many unique users that are, it’s appalling, and highly likely there are much more than those they found.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Tech Republic Security
OCTOBER 16, 2024
Getting buy-in can be difficult. Safe-U founder and CEO Jorge Litvin explains how to create a common language between the CISO and the rest of the C-suite.

Security Boulevard
OCTOBER 16, 2024
CA/B testing: Ludicrous proposal draws ire from “furious” systems administrators. The post Apple Enrages IT — 45-Day Cert Expiration Fury appeared first on Security Boulevard.

Advertisement
Many software teams have migrated their testing and production workloads to the cloud, yet development environments often remain tied to outdated local setups, limiting efficiency and growth. This is where Coder comes in. In our 101 Coder webinar, you’ll explore how cloud-based development environments can unlock new levels of productivity. Discover how to transition from local setups to a secure, cloud-powered ecosystem with ease.

Tech Republic Security
OCTOBER 16, 2024
With its questionable privacy policy, slow VPN performance, and lack of independent audits, Urban VPN fails to offer a secure and quality VPN experience.

Schneier on Security
OCTOBER 16, 2024
The men’s world conkers champion is accused of cheating with a steel chestnut.
Cyber Security Informer brings together the best content for cyber security professionals from the widest variety of industry thought leaders.

The Hacker News
OCTOBER 16, 2024
The FIDO Alliance said it's working to make passkeys and other credentials more easier to export across different providers and improve credential provider interoperability, as more than 12 billion online accounts become accessible with the passwordless sign-in method.

Security Boulevard
OCTOBER 16, 2024
A survey of IT professionals by Hornetsecurity found that while the number of ransomware victims are paying the ransoms, more of the data is being lost. In addition, while ransomware protection is a top priority, many feared their organizations were unprepared for an attack. The post More Ransoms Being Paid and More Data Being Lost: Hornetsecurity appeared first on Security Boulevard.
The Hacker News
OCTOBER 16, 2024
The North Korean threat actor known as ScarCruft has been linked to the zero-day exploitation of a now-patched security flaw in Windows to infect devices with malware known as RokRAT. The vulnerability in question is CVE-2024-38178 (CVSS score: 7.5), a memory corruption bug in the Scripting Engine that could result in remote code execution when using the Edge browser in Internet Explorer Mode.

Security Boulevard
OCTOBER 16, 2024
Fortinet has made generally available a version of the CNAPP it gained that is now integrated with the Fortinet Security Fabric, an orchestration framework the company developed to centralize the management of its cybersecurity portfolio. The post Fortinet Integrates Lacework CNAPP into Cybersecurity Portfolio appeared first on Security Boulevard.

Advertisement
After a year of sporadic hiring and uncertain investment areas, tech leaders are scrambling to figure out what’s next. This whitepaper reveals how tech leaders are hiring and investing for the future. Download today to learn more!

The Hacker News
OCTOBER 16, 2024
Threat actors are attempting to abuse the open-source EDRSilencer tool as part of efforts to tamper endpoint detection and response (EDR) solutions and hide malicious activity. Trend Micro said it detected "threat actors attempting to integrate EDRSilencer in their attacks, repurposing it as a means of evading detection.

Tech Republic Security
OCTOBER 16, 2024
An IT and security compliance analyst distilled seven ways to forge effective synergies between IT and broader business goals.

SecureWorld News
OCTOBER 16, 2024
What did the robot vacuum say to its homeowner? You suck. All kidding aside, in a bizarre turn of events, owners of robot vacuums across the U.S. have reported that their devices have been hacked. One particularly alarming case involved a man whose Ecovacs Deebot X2 began yelling racial slurs at him. The incidents appear to be linked to a security vulnerability in the Chinese-made Ecovacs Deebot X2 model, according to a report by the Australian Broadcast Corporation.

WIRED Threat Level
OCTOBER 16, 2024
The US has accused two brothers of being part of the hacker group Anonymous Sudan, which allegedly went on a wild cyberattack spree that hit hundreds of targets—and, for one of the two men, even put lives at risk.

Advertisement
Cloud Development Environments (CDEs) are changing how software teams work by moving development to the cloud. Our Cloud Development Environment Adoption Report gathers insights from 223 developers and business leaders, uncovering key trends in CDE adoption. With 66% of large organizations already using CDEs, these platforms are quickly becoming essential to modern development practices.

Security Boulevard
OCTOBER 16, 2024
What Is NIST? What Is NIST Compliance? Importance of Being NIST Compliant The Benefits of Meeting NIST Cybersecurity Standards Five Main NIST Frameworks Achieve Continuous NIST Compliance with FireMon Frequently Asked Questions Get a Demo National Institute of Standards and Technology (NIST) security standards have become a core competency for organizations aiming to strengthen their cybersecurity posture.

Security Affairs
OCTOBER 16, 2024
U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Windows Kernel, Mozilla Firefox and SolarWinds Web Help Desk bugs to its Known Exploited Vulnerabilities catalog. The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added the following vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog : CVE-2024-30088 (CVSS score 7.0) Microsoft Windows Kernel TOCTOU Race Condition Vulnerability CVE-2024-9680 Mozilla Firefox Use-After-Free Vulnerability CVE-2024-2

The Hacker News
OCTOBER 16, 2024
A new spear-phishing campaign targeting Brazil has been found delivering a banking malware called Astaroth (aka Guildma) by making use of obfuscated JavaScript to slip past security guardrails. "The spear-phishing campaign's impact has targeted various industries, with manufacturing companies, retail firms, and government agencies being the most affected," Trend Micro said in a new analysis.
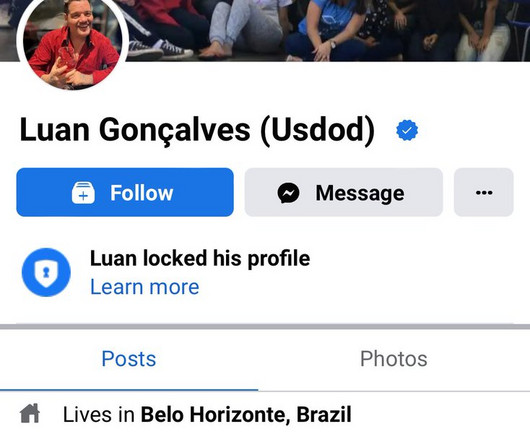
Security Affairs
OCTOBER 16, 2024
Brazil’s Polícia Federal has arrested hacker USDoD, the hacker behind the National Public Data and InfraGard breaches. Brazil’s Polícia Federal (PF) announced the arrest in Belo Horizonte/MG of the notorious hacker USDoD. In August, a CrowdStrike investigation revealed that the hacker USDoD (aka EquationCorp), who is known for high-profile data leaks, is a man from Brazil.

Advertisement
Tech leaders today are facing shrinking budgets and investment concerns. This whitepaper provides insights from over 1,000 tech leaders on how to stay secure and attract top cybersecurity talent, all while doing more with less. Download today to learn more!

The Hacker News
OCTOBER 16, 2024
To defend your organization against cyber threats, you need a clear picture of the current threat landscape. This means constantly expanding your knowledge about new and ongoing threats. There are many techniques analysts can use to collect crucial cyber threat intelligence. Let’s consider five that can greatly improve your threat investigations.

GlobalSign
OCTOBER 16, 2024
The recent proposed change by Apple suggests that certificate lifespans will be reduced even further. Learn how automating can help you prepare.

Malwarebytes
OCTOBER 16, 2024
Mozilla has announced a security fix for its Firefox browser which also impacts the closely related Tor Browser. The new version fixes one critical security vulnerability which is reportedly under active exploitation. To address the flaw, both Mozilla and Tor recommend that users update their browsers to the most current versions available. Firefox users that have automatic updates enabled should have the new version available as soon or shortly after they open the browser.

Security Affairs
OCTOBER 16, 2024
Finnish Customs shut down the Tor darknet marketplace Sipulitie and seized the servers hosting the platform. Finnish Customs, with the help of Europol, Swedish and Polish law enforcement authorities and researchers at Bitdefender , shut down the Tor marketplace Sipulitie. “Finnish customs has closed the web servers of the Sipulitie marketplace, which has been operating on the Tor network since 2023, in cooperation with the Swedish police, and confiscated their contents.

Advertisement
Explore how enterprises can enhance developer productivity and onboarding by adopting self-hosted Cloud Development Environments (CDEs). This whitepaper highlights the simplicity and flexibility of cloud-based development over traditional setups, demonstrating how large teams can leverage economies of scale to boost efficiency and developer satisfaction.

The Hacker News
OCTOBER 16, 2024
A critical security flaw has been disclosed in the Kubernetes Image Builder that, if successfully exploited, could be abused to gain root access under certain circumstances. The vulnerability, tracked as CVE-2024-9486 (CVSS score: 9.8), has been addressed in version 0.1.38. The project maintainers acknowledged Nicolai Rybnikar for discovering and reporting the vulnerability.
Graham Cluley
OCTOBER 16, 2024
WordPress's emperor, Matt Mullenweg, demands a hefty tribute from WP Engine, and a battle erupts, leaving millions of websites hanging in the balance. Meanwhile, the Internet Archive, a digital library preserving our online history, is under siege from hackers. All this and more is discussed in the latest edition of the "Smashing Security" podcast by cybersecurity veterans Graham Cluley and Carole Theriault.

Cisco Security
OCTOBER 16, 2024
Image-based fraud in email can be challenging to detect and prevent. By leveraging AI, security teams can make inboxes more secure. Image-based fraud in email can be challenging to detect and prevent. By leveraging AI, security teams can make inboxes more secure.

Zero Day
OCTOBER 16, 2024
Ecovacs just launched the Deebot N30 Omni, a robot vacuum with high-end features that are worth way more than its cost—especially with this limited-time deal.

Advertisement
IT leaders are experiencing rapid evolution in AI amid sustained investment uncertainty. As AI evolves, enhanced cybersecurity and hiring challenges grow. This whitepaper offers real strategies to manage risks and position your organization for success.
The Hacker News
OCTOBER 16, 2024
AI from the attacker’s perspective: See how cybercriminals are leveraging AI and exploiting its vulnerabilities to compromise systems, users, and even other AI applications Cybercriminals and AI: The Reality vs. Hype “AI will not replace humans in the near future.

Zero Day
OCTOBER 16, 2024
Some fine-tuning and adjustments turned the TCL S55 into a monster home entertainment set -- and currently it's $1,000 off.

CompTIA on Cybersecurity
OCTOBER 16, 2024
Dr. James Stanger, Chief Technology Evangelist at CompTIA, shares the challenges faced by technologists and the paradigm shifts occurring to address these challenges.

Zero Day
OCTOBER 16, 2024
The Fire HD 10 Kids Pro was a pleasant surprise. Its smooth performance for the price is even more remarkable.
Advertisement
Leverage the Cloud Development Environment Maturity Model to elevate your software development practices with scalable, secure cloud-based workspaces. This model offers a structured approach to modernizing development, aligning technology, developer experience, security, and workflows. By implementing Cloud Development Environments (CDEs), teams can boost efficiency, improve security, and streamline operations through centralized governance.
Let's personalize your content