Unauthorized data access vulnerability in macOS is detailed by Microsoft
Malwarebytes
OCTOBER 18, 2024
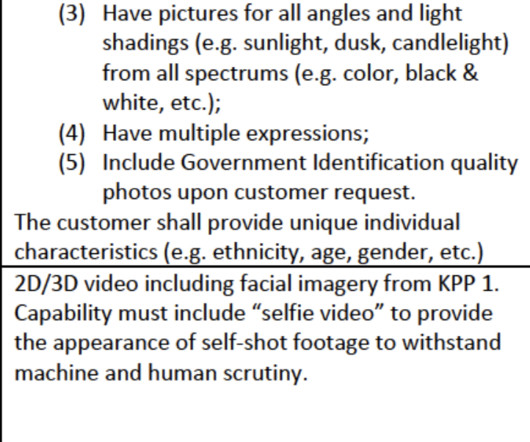
The Microsoft Threat Intelligence team disclosed details about a macOS vulnerability, dubbed “HM Surf,” that could allow an attacker to gain access to the user’s data in Safari. The data the attacker could access without users’ consent includes browsed pages, along with the device’s camera, microphone, and location. The vulnerability, tracked as CVE-2024-44133 was fixed in the September 16 update for Mac Studio (2022 and later), iMac (2019 and later), Mac Pro (2019 and later), Mac Mi










































Let's personalize your content