It’s the Most Wonderful Time to Secure Your eCommerce Website
SiteLock
AUGUST 27, 2021
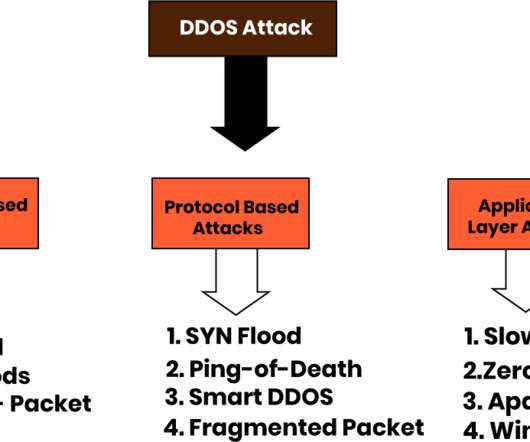
The holiday season is a busy time for online retailers and other ecommerce websites. Instead, get ahead securing your ecommerce website by knowing what to expect. Anticipating their behaviors can help mitigate risk and prevent an attack. Secure Your eCommerce Website. Anticipate an Attack.


































Let's personalize your content