Predatory app downloaded 100,000 times from Google Play Store steals data, uses it for blackmail
Malwarebytes
FEBRUARY 25, 2025
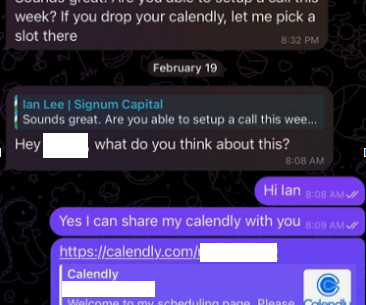
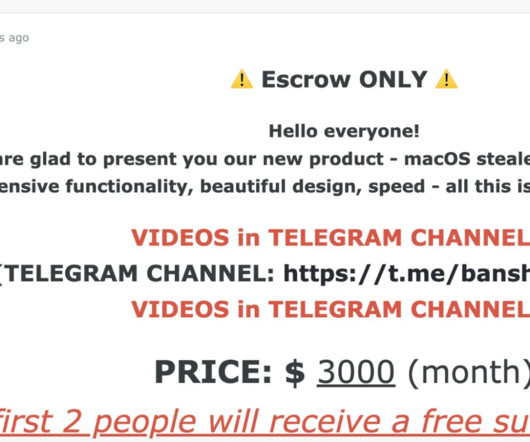
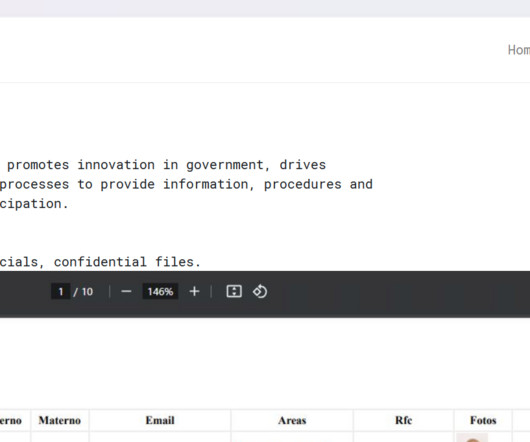
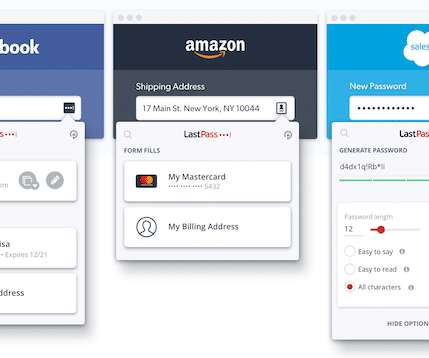
A malicious app claiming to be a financial management tool has been downloaded 100,000 times from the Google Play Store. Sometimes malware creators manage to get their apps listed in the official app store. You can make a stolen password useless to thieves by changing it. Better yet, let a password manager choose one for you.




























Let's personalize your content