Privacy Roundup: Week 3 of Year 2025
Security Boulevard
JANUARY 20, 2025
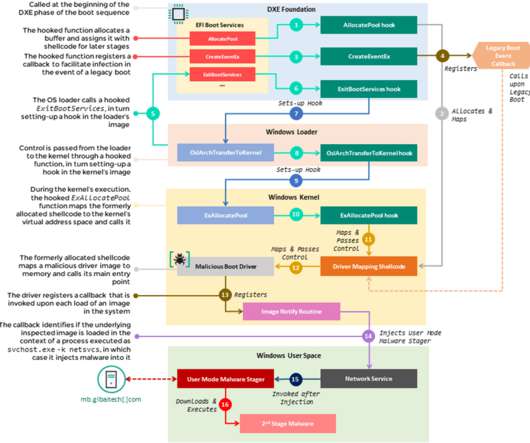
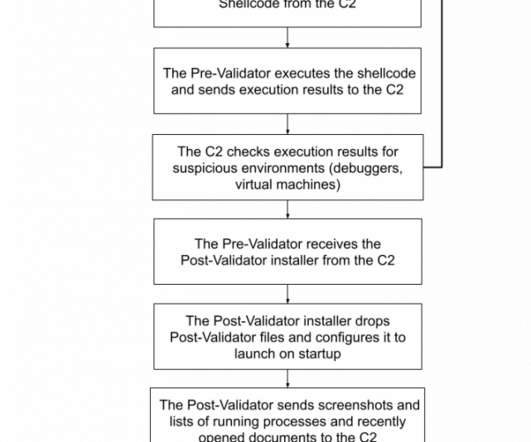
Inside the Black Box of Predictive Travel Surveillance Wired Covers the use of powerful surveillance technology in predicting who might be a "threat." Vulnerabilities and Malware Primarily includes severe and exploited vulnerabilities in devices or software used by end users (ex: a major router firmware flaw).






















Let's personalize your content