What are Common Types of Social Engineering Attacks?
eSecurity Planet
JULY 29, 2021
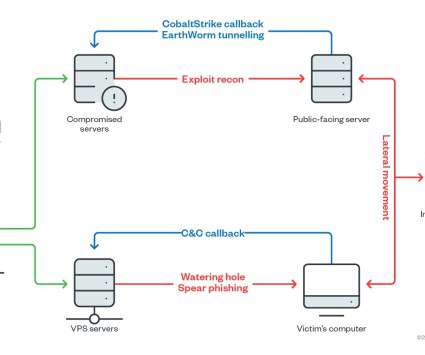
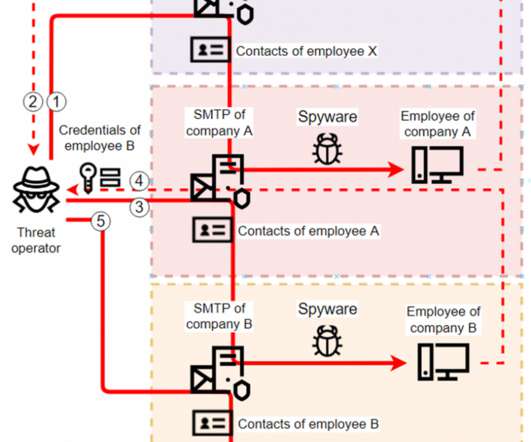
Social engineering is a common technique that cybercriminals use to lure their victims into a false sense of security. As social engineering tactics become more advanced, it’s important to know how to identify them in the context of cybersecurity. Social engineering in cybersecurity attacks.




























Let's personalize your content