MasterCard DNS Error Went Unnoticed for Years
Krebs on Security
JANUARY 22, 2025
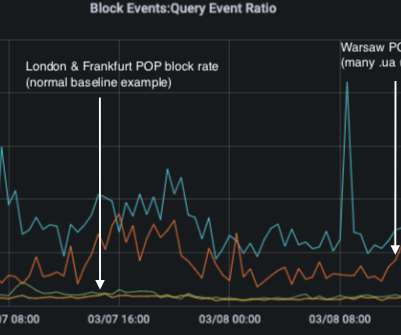
The payment card giant MasterCard just fixed a glaring error in its domain name server settings that could have allowed anyone to intercept or divert Internet traffic for the company by registering an unused domain name. A DNS lookup on the domain az.mastercard.com on Jan. 14, 2025 shows the mistyped domain name a22-65.akam.ne.


















Let's personalize your content