Threat Trends: DNS Security, Part 1
Cisco Security
MARCH 11, 2021
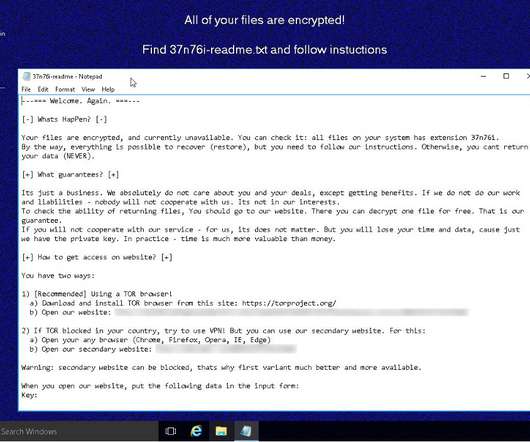
After examining topics such as the MITRE ATT&CK framework , LOLBins , and others, this release will look at DNS traffic to malicious sites. We’ll also look at malicious DNS activity—the number of queries malicious sites receive. Organizations and malicious DNS activity. Overview of analysis. Cryptomining.


































Let's personalize your content