Cybersecurity is Central to Digital Transformation
Security Boulevard
APRIL 6, 2022
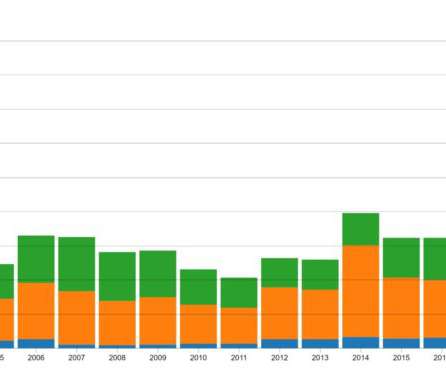
Digital transformation advances all business areas, fundamentally optimizing business processes and delivering value to customers. Spending on digital transformation is expected to reach $1.8 Spending on digital transformation is expected to reach $1.8 trillion in 2022. trillion in 2022.












































Let's personalize your content