Conti Ransomware Group Diaries, Part IV: Cryptocrime
Krebs on Security
MARCH 7, 2022
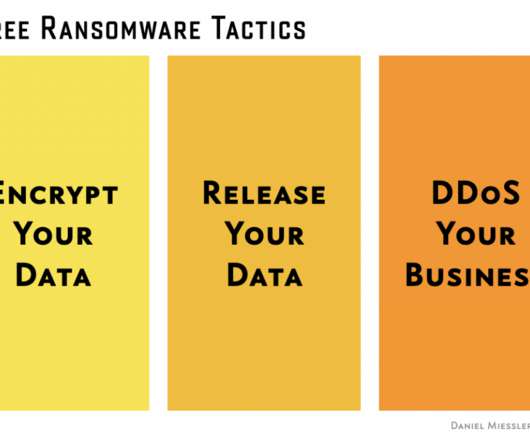
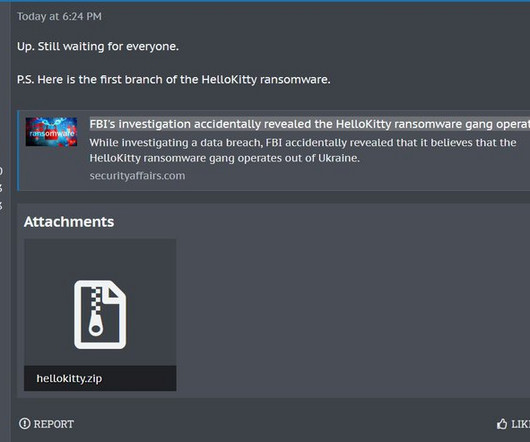
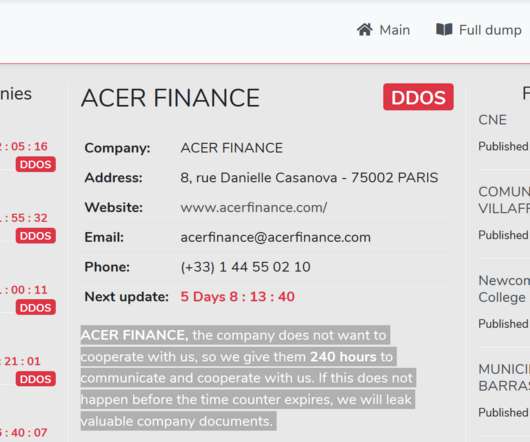
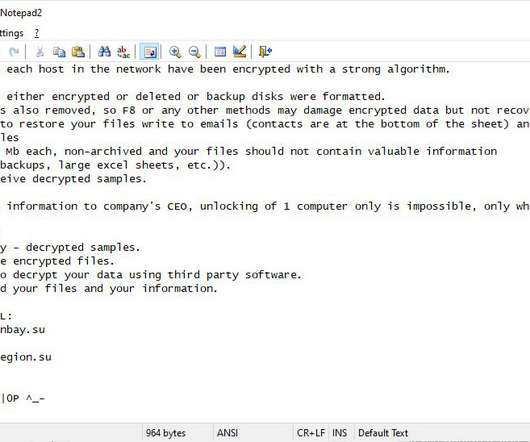
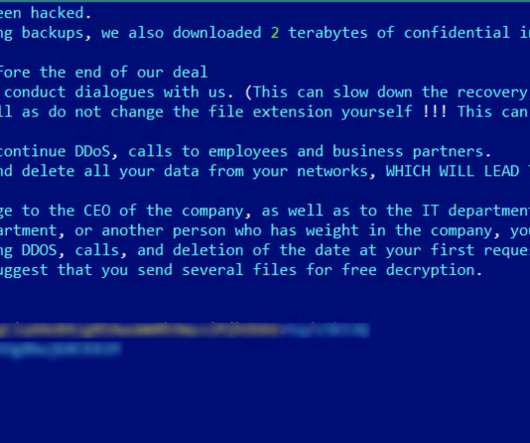
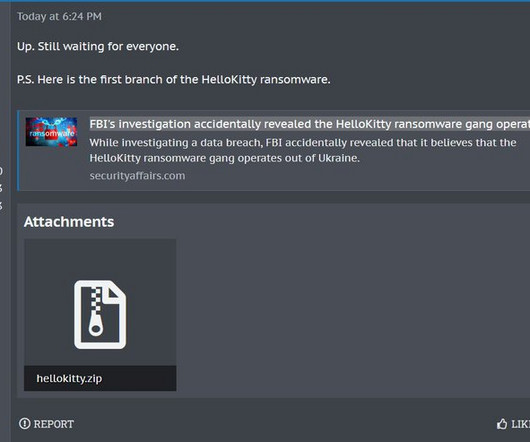
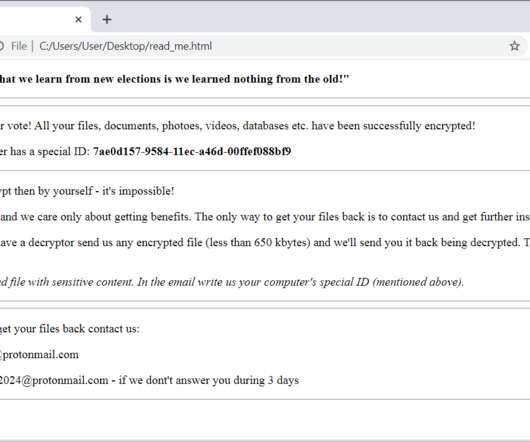
Three stories here last week pored over several years’ worth of internal chat records stolen from the Conti ransomware group, the most profitable ransomware gang in operation today. Before that, Jeffrey Ladish , an information security consultant based in Oakland, Calif., We release ddos. Crypto falls in price.

































Let's personalize your content