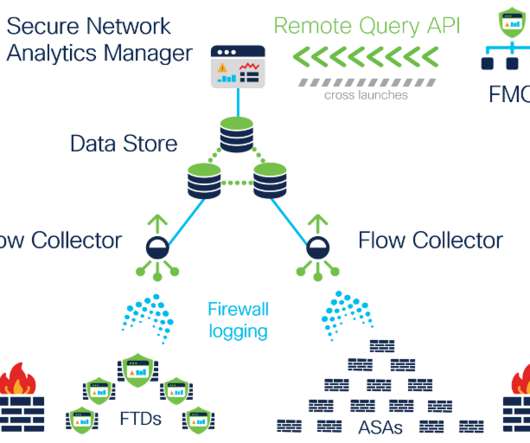
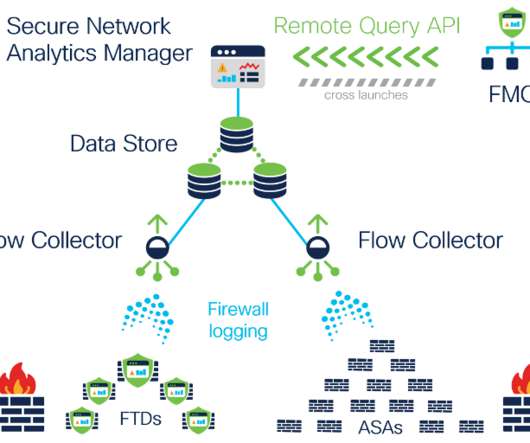
Introducing continuous remote worker visibility and expanded data collection with Secure Network Analytics Release 7.3.2
Cisco Security
JUNE 1, 2021
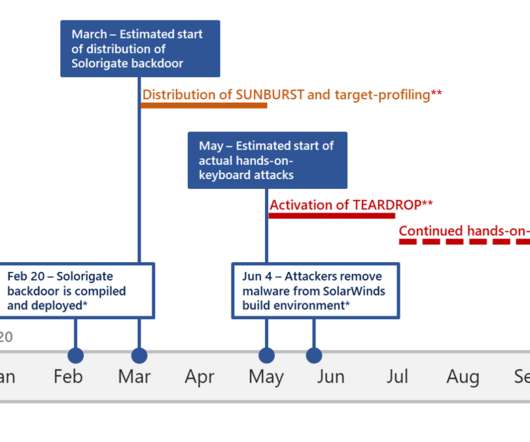
It’s no secret that last year’s abrupt exodus away from corporate offices presented organizations with novel challenges related to monitoring and securing their newly remote workforce. Expanded data collection to provide further extended visibility and enhanced context . With release 7.3.2,



























Let's personalize your content