New AI Threats Emerge as FraudGPT Creator Unleashes DarkBERT and DarkBART
eSecurity Planet
AUGUST 3, 2023
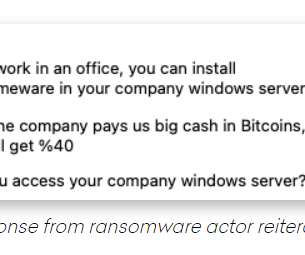
Daniel Kelley, a reformed black hat hacker and researcher at cybersecurity firm SlashNext, posed as a potential buyer and contacted the individual – “CanadianKingpin12” – who’s been promoting FraudGPT. Email Address By signing up to receive our newsletter, you agree to our Terms of Use and Privacy Policy.















































Let's personalize your content