RSA Conference 2025: Top Announcements and Key Takeaways from the Cybersecurity World’s Biggest Stage
eSecurity Planet
MAY 1, 2025
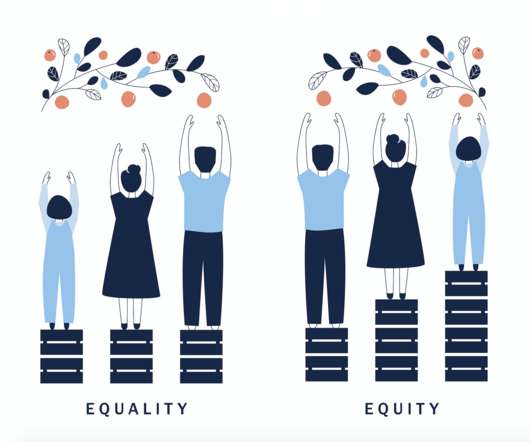
The RSA Conference 2025, held in San Francisco from April 28 to May 1, spotlighted the evolving landscape of cybersecurity, with a strong emphasis on artificial intelligence, identity security, and collaborative defense strategies. One Community) emphasized collaboration across diverse perspectives to tackle cybersecurity challenges.





















Let's personalize your content