Voice Phishers Targeting Corporate VPNs
Krebs on Security
AUGUST 19, 2020
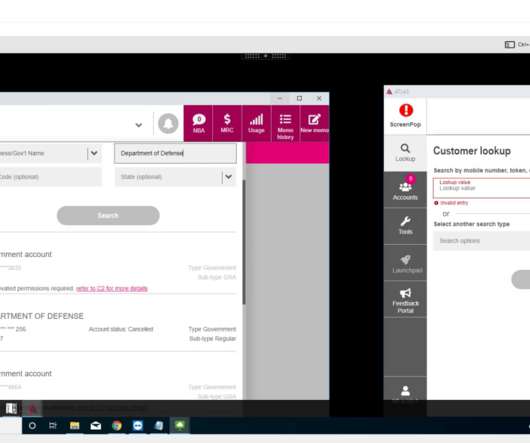
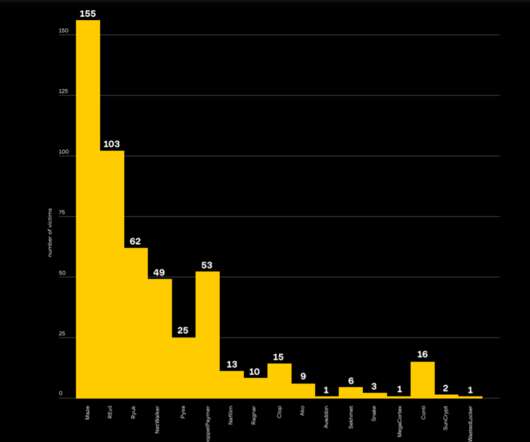
For now at least, they appear to be focusing primarily on companies in the financial, telecommunications and social media industries. Allen said it matters little to the attackers if the first few social engineering attempts fail. A phishing page (helpdesk-att[.]com) com) targeting AT&T employees. Image: urlscan.io.





















Let's personalize your content