Increasing Awareness of DNS Hijacking: A Growing Cyber Threat
Tech Republic Security
NOVEMBER 6, 2024
DNS hijacking is a growing threat that can redirect users to malicious sites. However, using passive DNS monitoring can help to protect data.
This site uses cookies to improve your experience. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country, we will assume you are from the United States. Select your Cookie Settings or view our Privacy Policy and Terms of Use.
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.
Used for the proper function of the website
Used for monitoring website traffic and interactions
Cookies and similar technologies are used on this website for proper function of the website, for tracking performance analytics and for marketing purposes. We and some of our third-party providers may use cookie data for various purposes. Please review the cookie settings below and choose your preference.

Tech Republic Security
NOVEMBER 6, 2024
DNS hijacking is a growing threat that can redirect users to malicious sites. However, using passive DNS monitoring can help to protect data.
The Hacker News
JULY 24, 2024
The Internet Systems Consortium (ISC) has released patches to address multiple security vulnerabilities in the Berkeley Internet Name Domain (BIND) 9 Domain Name System (DNS) software suite that could be exploited to trigger a denial-of-service (DoS) condition. "A Cybersecurity and
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

The Hacker News
APRIL 29, 2024
A previously undocumented cyber threat dubbed Muddling Meerkat has been observed undertaking sophisticated domain name system (DNS) activities in a likely effort to evade security measures and conduct reconnaissance of networks across the world since October 2019.

Malwarebytes
JUNE 1, 2022
If you’re an SMB, chances are that you’re already well-aware of the fact that cyber threats can wreak havoc on your business. That’s where DNS filtering comes in. But first, DNS in a nutshell. So normally, every time your customer types in your web address, their computer makes a request to a DNS server.
Krebs on Security
DECEMBER 19, 2024
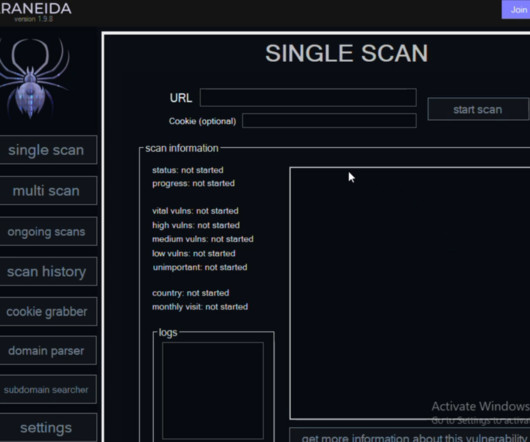
Cyber threat analysts at Silent Push said they recently received reports from a partner organization that identified an aggressive scanning effort against their website using an Internet address previously associated with a campaign by FIN7 , a notorious Russia-based hacking group. Araneida Scanner.

Krebs on Security
OCTOBER 11, 2022
. “Despite its relatively low score in comparison to other vulnerabilities patched today, this one should be at the top of everyone’s list to quickly patch,” said Kevin Breen , director of cyber threat research at Immersive Labs.

Heimadal Security
JULY 28, 2023
You scramble to find a solution to protect yourself and your company from these cyber threats. Enter […] The post DNS Protection: A Must-Have Defense Against Cyber Attacks appeared first on Heimdal Security Blog. Your heart races as you realize that your sensitive data and personal information may be at risk.

Security Boulevard
MAY 20, 2022
What Is DNS Spoofing and How Is It Prevented? What Is the DNS and DNS Server? . To fully understand DNS spoofing, it’s important to understand DNS and DNS servers. The DNS “domain name system” is then what translates the domain name into the right IP address. What Is DNS Spoofing? .

Krebs on Security
APRIL 13, 2022
.” “These could be the kind of vulnerabilities which appeal to ransomware operators as they provide the potential to expose critical data,” said Kevin Breen , director of cyber threat research at Immersive Labs.

Security Boulevard
JULY 9, 2024
Defense in depth and operational resiliency are the future for organizations that want to survive in the new world of cyber threats. Operational resiliency necessitates intelligence, visibility, and confidence: the three foundational pillars of protective DNS (PDNS). But Wait, What Is Protective DNS?

Security Boulevard
AUGUST 7, 2024
HYAS Protect protective DNS uses advanced data analytics to proactively block cyber threats, a feature unavailable in legacy systems relying on static DNS filtering. AV-TEST , one of the cybersecurity industry’s most trusted evaluators, rates HYAS as the most effective protective DNS solution on the market.

CyberSecurity Insiders
MARCH 29, 2023
alphaMountain has launched a new platform called “threatYeti,” designed to aid cyber threat analysts, security researchers, and in-house security operations teams with domain research.

Security Boulevard
APRIL 29, 2025
Chinas state-sponsored cyber operations, driven by groups like Volt Typhoon, Salt Typhoon, Brass Typhoon, and APT41, and amplified by techniques like Fast Flux DNS, are not chasing Hollywood apocalypsetheyre seizing Americas networks, turning our infrastructure into a weapon against us.
Security Boulevard
APRIL 4, 2025
Increase monitoring and logging of DNS and network traffic; and set up fast flux alert mechanisms. Share fast flux detection indicators, such as domains and IP addresses, with partners and threat intelligence communities via, for example, the U.S.s Automated Indicator Sharing and Australias Cyber Threat Intelligence Sharing Platform.
Security Boulevard
OCTOBER 2, 2023
Phishing Threats Are Increasing in Scale and Sophistication Phishing remains one of the most dangerous and widespread cybersecurity threats. Source: IBM Security: Cost of a Data Breach Report 2023) According to recent research, the number of phishing attacks vastly outpaces all other cyber threats. billion USD globally.

Security Boulevard
FEBRUARY 20, 2025
DNS attacks can lead to data breaches, phishing, and service disruptions. Learn about common types of DNS attacks and how to protect your domain from cyber threats. The post Types of DNS Attacks: How They Work & How to Stay Protected appeared first on Security Boulevard.

Security Boulevard
MARCH 18, 2025
Cyber threats are growing in sophistication, and adversaries are continually evolving their methods, targeting businesses, governments, and individuals with precision. It consolidates multiple layers of information and correlates them to deliver a contextualized understanding of cyber threats.

CyberSecurity Insiders
MAY 18, 2022
You know things are dire when the President of the United States uses his bully pulpit to warn American organizations they are likely to be the target of increased cyber threat activity and therefore have a responsibility to protect their infrastructure. So why aren’t more organizations taking advantage of protective DNS?

The Last Watchdog
DECEMBER 13, 2020
Gartner refers to this as the Secure Access Service Edge (SASE), which is a framework combining the functionality of Wide Area Network (WAN) with network security services to shield against any cyber threats or cloud-enabled SaaS. The cyber threats landscape. SASE is a sophisticated response to a complex, dynamic threat.

SC Magazine
MAY 26, 2021
This latest version of Chrome supports DoH, or DNS-over-HTTPS, said Sean Nikkel, senior cyber threat intel analyst at Digital Shadows. Nikkel said the DoH feature was previously only available in other browsers and operating systems and offers a much more secure method for making DNS requests.
Security Boulevard
FEBRUARY 23, 2023
Thankfully, nearly all malware depends on DNS at some point in their kill chain, making the protocol a critical vector for shutting down these threats. Some of the common forms these DNS-based attacks can take include: DNS spoofing: A malicious actor alters DNS records to redirect traffic to a fake website or server.

eSecurity Planet
JANUARY 6, 2021
Stack components impacted include DNS, IPv6, IPv4, TCP, ICMP, LLMNR, and mDNS. Forescout found DNS to be the most vulnerable due to its complexity, with TCP and IPv4 and IPv6 sub-stacks not far behind. DNS Cache Poisoning: 2. AMNESIA:33 leaves devices and networks open to four potential memory corruption threats.

Penetration Testing
NOVEMBER 18, 2024
A recent report from Infoblox Threat Intel sheds light on an underreported yet pervasive cyber threat: the “Sitting Ducks” attack, a domain hijacking technique that has enabled cybercriminals to weaponize... The post DNS Predators Exploit “Sitting Ducks” Attack to Hijack Domains and Expand Cyber Operation appeared (..)

Security Boulevard
MAY 6, 2021
Since this hybrid and remote way of working looks like it’s here to stay, businesses must ensure they have the right infrastructure in place to combat any cyber threats. This includes a layered combination of DNS networking, secure endpoint connections, and an educated and empowered human workforce.

SC Magazine
MAY 3, 2021
Hundreds of millions of protected endpoints and users, billions of DNS requests, and millions of authentications mean Cisco sees more threats and vulnerabilities than most anyone else. This creates a competitive advantage through stopping more bad actors getting onto the network in the first place.
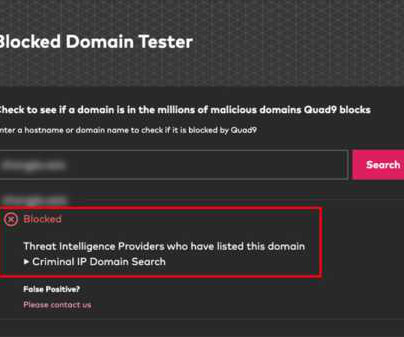
The Last Watchdog
MAY 13, 2024
May 13, 2024, CyberNewsWire — Criminal IP, a renowned Cyber Threat Intelligence (CTI) search engine developed by AI SPERA, has recently signed a technology partnership to exchange threat intelligence data based on domains and potentially on the IP address to protect users by blocking threats to end users.

CyberSecurity Insiders
MARCH 13, 2021
This activity was shortly followed by escalating activity involving brute force activity, remote code execution attempts, and exfiltration channel probing attempts all exploiting vulnerable DNS services on the domain controllers. The post Stories from the SOC – DNS recon + exfiltration appeared first on Cybersecurity Insiders.

SecureWorld News
MAY 16, 2024
Popular services include receiving actionable intelligence on threats targeting their systems and leveraging the NSA's leading malware reverse-engineering skills to remove cyber threats after breaches. It's in NSA's and DoD's best interests to help." Get started by filling out a Cybersecurity Services Contact Form.
Security Boulevard
APRIL 8, 2025
DNS Tampering, Trusted IP misuse and Redirection: Redirection and tampering of DNS: DNS and trusted host or IP tampering and redirection can be used to redirect users to malicious websites or to disrupt network traffic. Reverse Engineering: This technique analyzes software to understand its design and functionality.

Security Affairs
MARCH 5, 2019
Google Chronicle launched Backstory, the first global security telemetry platform designed to allow companies monitoring cyber threats. Google Chronicle announced Backstory, a cloud-based enterprise-level threat analytics platform that allows companies quickly investigate incidents, discover vulnerabilities and hunt for cyber threats.

Security Boulevard
APRIL 3, 2025
The post The Fast Flux DNS Threat: A Call to Action Against a Geopolitical and Hacktivist Nightmare appeared first on Security Boulevard. However, these same tools introduce significant security risksoften in ways organizations fail to anticipate.

Approachable Cyber Threats
FEBRUARY 1, 2024
Have a valid forward and reverse DNS record for sending IPs ❯ Additionally, for bulk senders: ○ Implement both SPF and DKIM ○ Publish a valid DMARC policy ○ Support one-click unsubscribe and honor user requests within two (2) days “What does this mean for me?” To get started: ❯ Have a DMARC Policy for your DNS. Don’t send spam.

Security Affairs
DECEMBER 22, 2021
Supports DNS callback for vulnerability discovery and validation. Government experts warn of sophisticated cyber threat actors which are actively scanning networks to potentially exploit the above flaws in vulnerable systems. Fuzzing for more than 60 HTTP request headers (not only 3-4 headers as previously seen tools).
Webroot
MAY 6, 2024
As we navigate through 2024, the cyber threat landscape continues to evolve, bringing new challenges for both businesses and individual consumers. The latest OpenText Threat Report provides insight into these changes, offering vital insights that help us prepare and protect ourselves against emerging threats.

Approachable Cyber Threats
OCTOBER 27, 2020
Luckily you can start to make a difference right now by implementing some changes to your DNS records. So for example, if you registered your website “www.mycompany.com” with GoDaddy, you would edit your DNS record on GoDaddy. Now that you have your list, head to your DNS provider and add a new entry. www.hivesystems.io).

Security Boulevard
MARCH 6, 2024
Traditionally, cybersecurity has been a reactive game: We respond to cyber threats as they arise, analyze the incidents, add pertinent information to “deny lists”, and update stakeholders on “what happened.” That's where technologies like protective DNS come in. It may sound difficult, but change always sounds hard at first.
eSecurity Planet
SEPTEMBER 17, 2021
Cobalt Strike Beacon Linux enables emulation of advanced attacks to a network over HTTP, HTTPS, or DNS. It’s a DNS-based communication that helps circumvent classic defense mechanisms that focus on HTTP traffic. A New Variant of Cobalt Strike. It provides a console where you can open a beacon session and enter specific commands.

Security Boulevard
JUNE 20, 2024
The right tools coupled with unique data function as preventative measures against threat actors using innovative methods to target and exploit organizations and individuals alike. With the number of cyber threats on the rise, no sector is truly safe from serious fallout. Download the use cases 1.
Security Boulevard
JANUARY 26, 2022
Note: This OSINT analysis has been originally published at my current employer's Web site - [link] where I'm currently acting as a DNS Threat Researcher since January, 2021. Sample personal emails known to have been currently in use by the "Jabber ZeuS" also known as "Aqua ZeuS" gang: donsft@hotmail[.]com. johnny@guru[.]bearin[.]donetsk[.]ua.

CyberSecurity Insiders
MARCH 5, 2021
The enterprises need to deploy a good NTA (NDR) solution that is capable of logging important metadata from the traffic of DNS and other important L7 application protocols. Data ingestion through DNS logs are also helpful, but it might not capture the signals if the attacker utilizes public DNS such as Google DNS (8.8.8.8)

Penetration Testing
DECEMBER 24, 2023
In the ever-evolving landscape of cyber threats, a new attack technique named SMTP Smuggling has emerged, threatening the integrity of email communication worldwide.

Hacker's King
OCTOBER 12, 2024
Maltego works by using "transforms" to extract data from a range of online sources such as DNS records, whois databases, social media, and web pages. In 2024, as cyber threats continue to evolve, using advanced OSINT tools is essential for both offense and defense in the cybersecurity landscape. Why Use Maltego?

eSecurity Planet
JANUARY 14, 2022
The combination of Prolexic, Edge DNS, and App & API Protector would be recommended for the highest quality of DDoS mitigation to keep applications, data centers, and internet-facing infrastructure (public or private) protected. It is architected for nonstop DNS availability and high performance, even across the largest DDoS attacks.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content