Cybersecurity Snapshot: SANS Recommends Six Controls To Secure AI Systems, While NCSC Warns About Outdated API Security Methods
Security Boulevard
APRIL 4, 2025
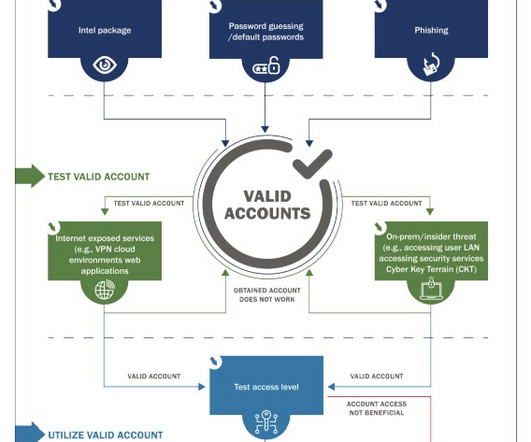
document outlines these six key security control categories for mitigating AI systems' cyber risks. Share fast flux detection indicators, such as domains and IP addresses, with partners and threat intelligence communities via, for example, the U.S.s The SANS Draft Critical AI Security Guidelines v1.1 Check out what they said.
















Let's personalize your content