LW ROUNDTABLE — How 2024’s cyber threats will transform the security landscape in 2025
The Last Watchdog
DECEMBER 16, 2024
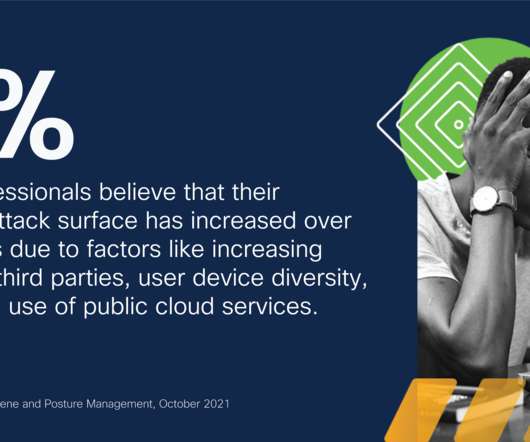
Sundaresan Bindu Sundaresan , Cybersecurity Director, LevelBlue In 2025, cybercriminals will exploit supply chain vulnerabilities, ransomware, IoT botnets, and AI-driven phishing. Rising IoT use demands standards to prevent device weaponization, while AI-enabled phishing challenges defenses. That’s the easy part. The hard part?
















































Let's personalize your content