Security Risks of AI
Schneier on Security
APRIL 27, 2023
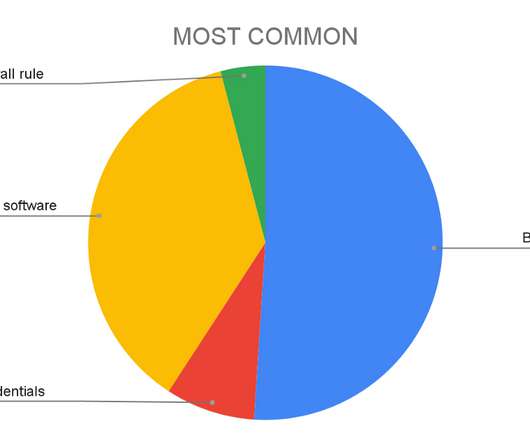
Stanford and Georgetown have a new report on the security risks of AI—particularly adversarial machine learning—based on a workshop they held on the topic. Many AI products are deployed without institutions fully understanding the security risks they pose.










































Let's personalize your content