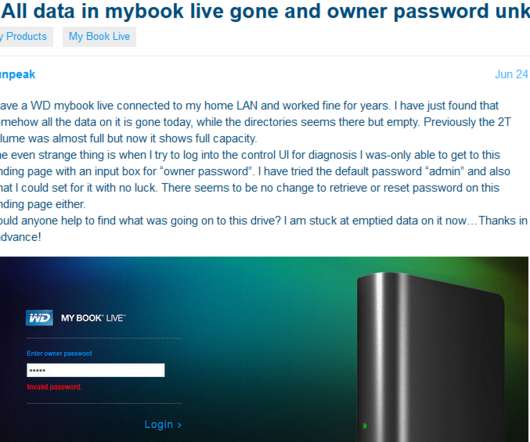
MyBook Users Urged to Unplug Devices from Internet
Krebs on Security
JUNE 25, 2021
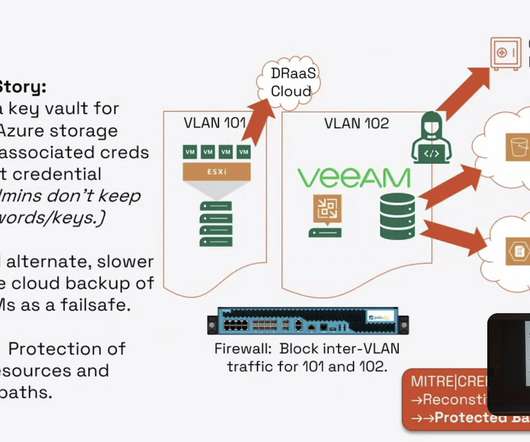
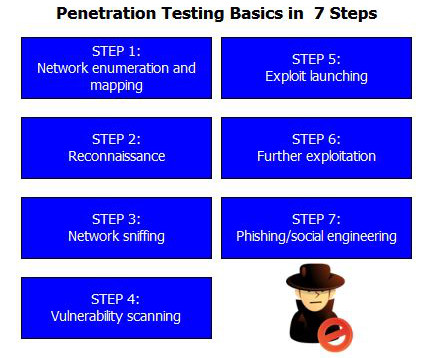
That response also suggested this bug has been present in its devices for at least a decade. We encourage users who wish to continue operating these legacy products to configure their firewall to prevent remote access to these devices, and to take measures to ensure that only trusted devices on the local network have access to the device.”








































Let's personalize your content