Recycle Your Phone, Sure, But Maybe Not Your Number
Krebs on Security
MAY 19, 2021
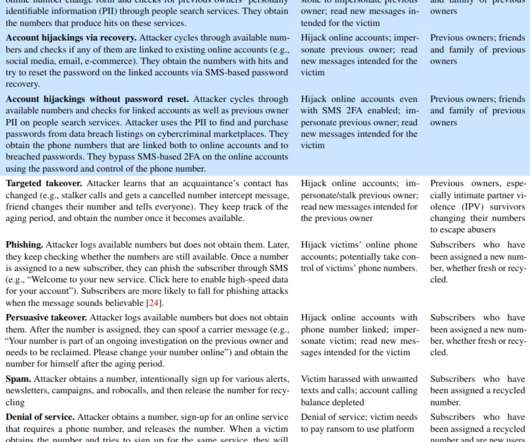
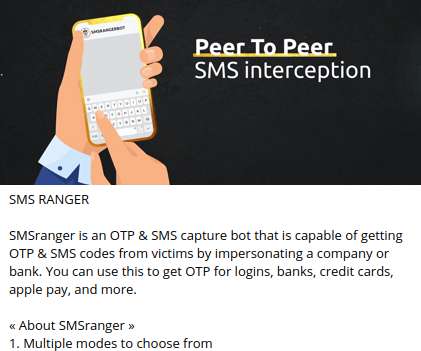
New research shows how fraudsters can abuse wireless provider websites to identify available, recycled mobile numbers that allow password resets at a range of email providers and financial services online. While you’re at it, consider removing your phone number as a primary or secondary authentication mechanism wherever possible.












Let's personalize your content