Roger Grimes on Prioritizing Cybersecurity Advice
Schneier on Security
OCTOBER 31, 2024
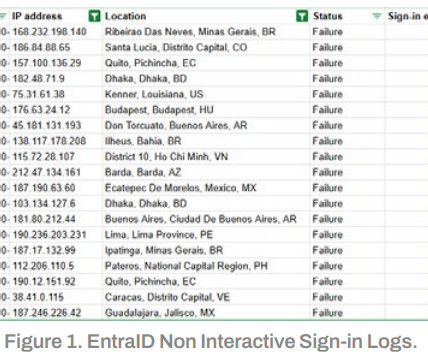
For example, we are often given a cybersecurity guideline (e.g., The catch is: There are two recommendations that WILL DO MORE THAN ALL THE REST ADDED TOGETHER TO REDUCE CYBERSECURITY RISK most efficiently: patching and using multifactor authentication (MFA). PCI-DSS, HIPAA, SOX, NIST, etc.) with hundreds of recommendations.













































Let's personalize your content