MY TAKE: How ‘credential stuffing’ and ‘account takeovers’ are leveraging Big Data, automation
The Last Watchdog
OCTOBER 16, 2019
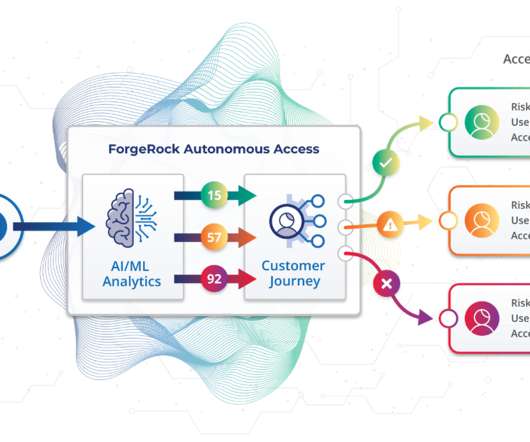
Related: Cyber risks spinning out of IoT Credential stuffing and account takeovers – which take full advantage of Big Data, high-velocity software, and automation – inundated the internet in massive surges in 2018 and the first half of 2019, according to multiple reports. Rapid 7 estimates that there are upwards of 1.5



























Let's personalize your content