Pairwise Authentication of Humans
Schneier on Security
FEBRUARY 10, 2025
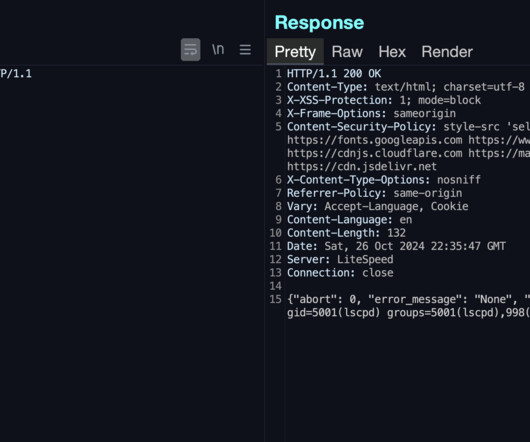
Here’s an easy system for two humans to remotely authenticate to each other, so they can be sure that neither are digital impersonations. To mitigate that risk, I have developed this simple solution where you can setup a unique time-based one-time passcode (TOTP) between any pair of persons.












Let's personalize your content