NIST Releases First Post-Quantum Encryption Algorithms
Schneier on Security
AUGUST 15, 2024
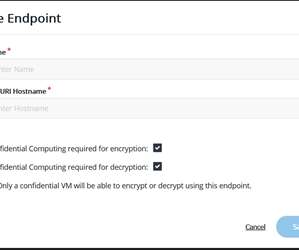
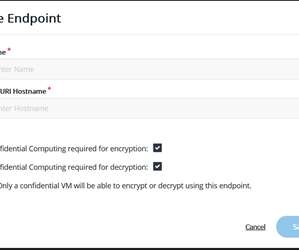
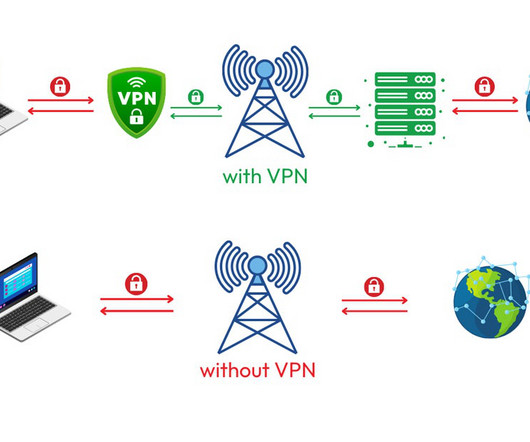
EDITED TO ADD: Good article : One – ML-KEM [PDF] (based on CRYSTALS-Kyber) – is intended for general encryption, which protects data as it moves across public networks. My recent writings on post-quantum cryptographic standards. NIST plans to select one or two of these algorithms by the end of 2024.












































Let's personalize your content