Zero Trust Network Architecture vs Zero Trust: What Is the Difference?
Joseph Steinberg
JANUARY 4, 2023
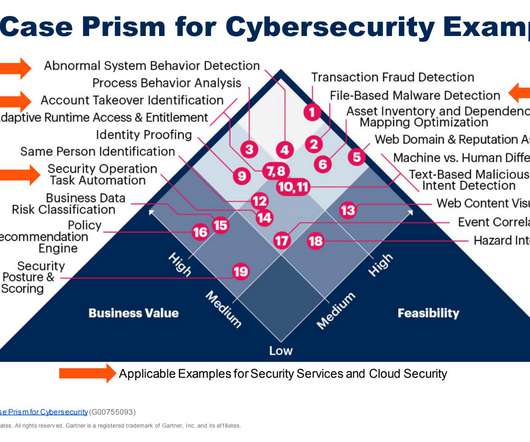
But, even those who have a decent grasp on the meaning of Zero Trust seem to frequently confuse the term with Zero Trust Network Architecture (ZTNA). Zero Trust Network Architecture is an architecture of systems, data, and workflow that implements a Zero Trust model. In short, Zero Trust is an approach.












































Let's personalize your content