MY TAKE: Securing the Internet of Everything: why self-healing devices are the next frontier
The Last Watchdog
FEBRUARY 10, 2025
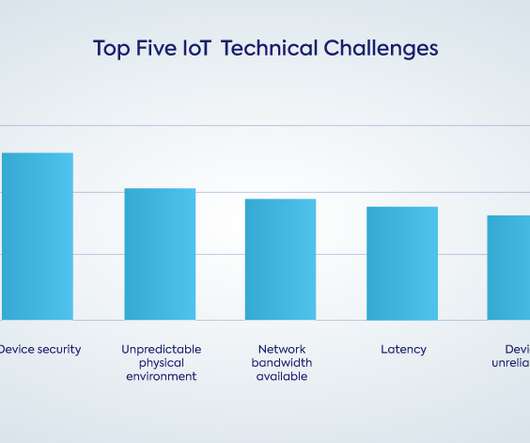
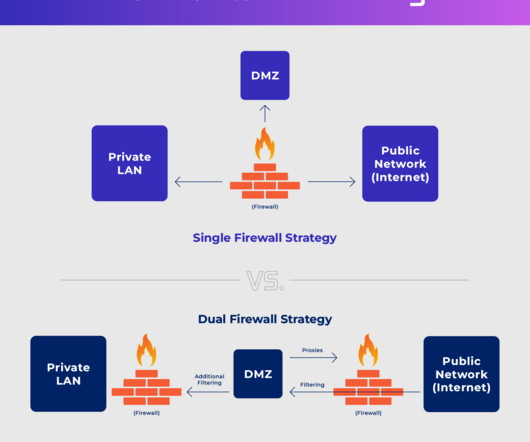
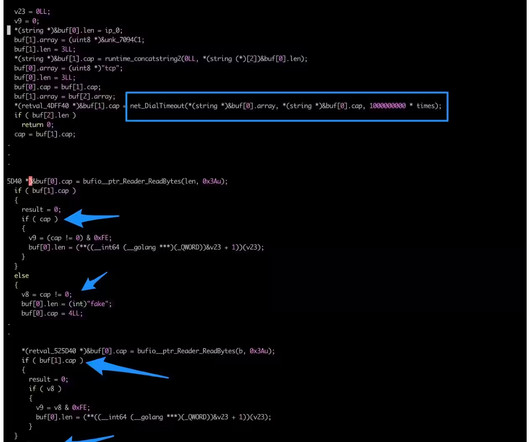
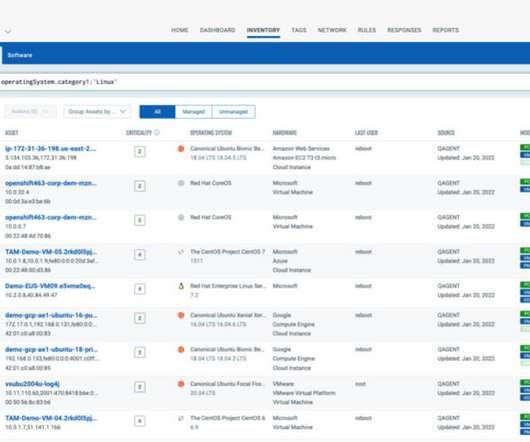
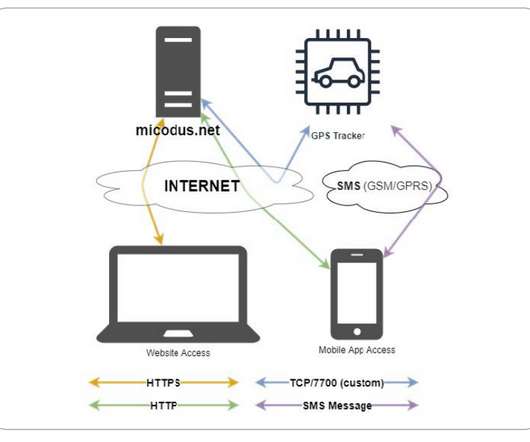
Were just getting started down the road to the Internet of Everything (IoE.) We went over how Zero Trust Architecture ( ZTA ) is gaining steam — and how it embodies a critical paradigm shift necessary to secure hyper-interconnected services. The chipmakers, software developers and device manufacturers all have a role to play.








































Let's personalize your content